ESET has published a new decryption tool for Syrian victims of the GandCrab ransomware. The developers of this infamous malware family released the keys on an underground forum following a tweet from a Syrian victim who had lost pictures of his deceased children to the encrypting malicious code.
They want 600 dollars to give me back my children, that's what they've done, they've taken my boys away from me for a some filthy money. How can I pay them 600 dollars if I barely have enough money to put food on the table for me and my wife?
— جميل سليمان (@kvbNDtxL0kmIqRU) October 16, 2018
[wls_document_promo id="https://download.eset.com/com/eset/tools/decryptors/gandcrab/latest/esetgandcrabdecryptor.exe" text="Download the decryptor " button="Click here to download"][/wls_document_promo]
In their public message, GandCrab’s operators quoted “political and economic situation as well as relations with CIS countries” as the reasons for their decision. The group has also emphasized that this was an exception and keys for other countries or victims would not be shared even if GandCrab operations are seized in the future.
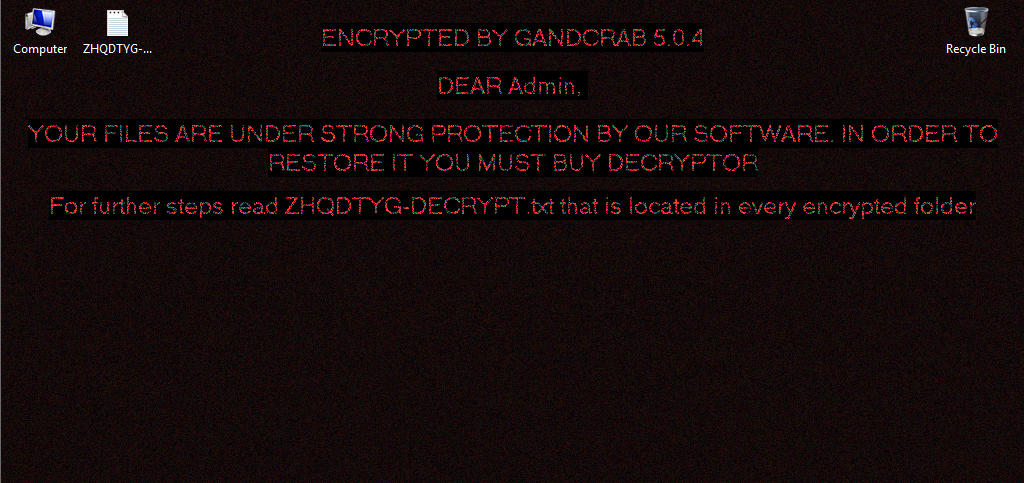
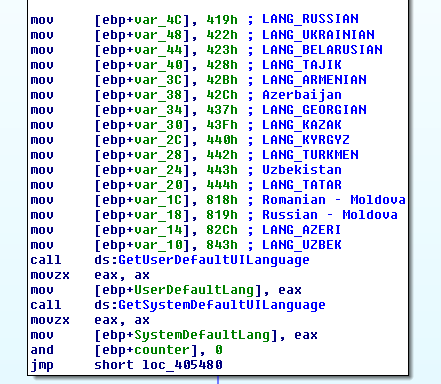
As reported by BleepingComputer.com, the released batch only encompasses keys for Syrian victims. Malware operators also stated that it was a mistake to keep Syria on the list of targeted countries. It is unclear if this will change in any future GandCrab campaigns, as the latest variant (5.0.4) does not list languages used in Syria among the exemptions (see Figure 1).
The ESET GandCrab decryption tool is designed to decrypt files of 979 Syrian victims irrespective of the malware version they were affected with (1.0 to 5.0). Users can download the decryptor here. For further instructions and information, please refer to our GandCrab decryptor knowledgebase article.
This is not the first time malware authors have released keys for a prevalent ransomware family (or its variants), allowing cybersecurity companies to create decryptors. Previously, ESET has released such tools for TeslaCrypt, several variants of Crysis, as well as for earlier variants of the AESNI ransomware.
How to avoid ransomware infections?
Prevention is essential in keeping users safe from this long-known threat. We recommend that all users keep their operating systems and software updated, use reliable security solutions with multiple layers of protection, and regularly back up all important and valuable data at an offline location (such as external storage).
Businesses are advised to:
- Reduce attack surface by disabling or uninstalling any unnecessary services and software.
- Scan networks for risky accounts using weak passwords and ensure they are improved.
- Limit or ban the use of Remote Desktop Protocol (RDP) from outside of the network, or enable Network Level Authentication.
- Use a Virtual Private Network (VPN) for employees accessing company systems remotely.
- Review firewall settings and close any non-essential ports that could lead to an infection.
- Review rules and policies for traffic between internal company systems and any outside network(s).
- Password-protect the configurations of your security solutions to prevent them from being disabled by an attacker.
- Segment the company LAN into subnets and connect them to firewalls to limit lateral movement and the possible impact of ransomware, or other attacks, within the network.
- Protect backups with two- or multi-factor authentication.
- Regularly train staff to recognize cyberthreats and how to handle social engineering attacks.
- Permit shared file and folder access only to those who need it, including making content read-only, and only changing this setting for staff who must have write access.
- ESET recommends that its customers also enable detection of potentially unsafe/unwanted applications (PUSA/PUA) to detect and block tools that can be misused by attackers to disable the security solution.