The trojan downloader Nemucod is back with a new campaign. This time however, it has changed the payload served to its victims – ransomware is not its go-to malware. Currently the “weapon of choice” is a backdoor detected by ESET as Win32/Kovter, in this instance mainly focusing on ad-clicking.
As a backdoor, this trojan allows the attacker to control the machine remotely without the victim’s consent or knowledge. The currently used variant can perform four main activities: 1. Download and run a file, 2. Gather various information and send it to a C&C server, 3. Store its own configuration data in Windows Registry entries, and 4. Control its own “click-function”.
"In the recently observed wave, malware operators are mainly focusing on the ad-clicking capability delivered via an embedded browser."
In the recently observed wave, malware operators are mainly focusing on the ad-clicking capability delivered via an embedded browser. The trojan can activate as many as 30 separate threads, each visiting websites and clicking on ads.
The number of threads can change according to commands from the attacker and can also alter them automatically – since Kovter is monitoring free memory and CPU usage. This helps the trojan not to overload the system and keep a low profile.
However, when the computer is idle, the malware may allocate more resources to its activities until further user activity is detected. When set in Kovter’s configuration it can also check whether the infected machine runs in a controlled or virtual environment and reports this fact to the attacker.
To deliver Kovter, the attackers behind the campaign use the Nemucod downloader disguised as an email ZIP attachment. Posing as a fake invoice, cybercriminals try to convince users to open it (unaware that it contains an infected executable JavaScript file).
This technique is used to avoid detection in some mail scanners and to reach as many victims as possible. If the user falls for the trap and executes the infected file – the Nemucod downloader – it downloads Kovter onto the machine and executes it.
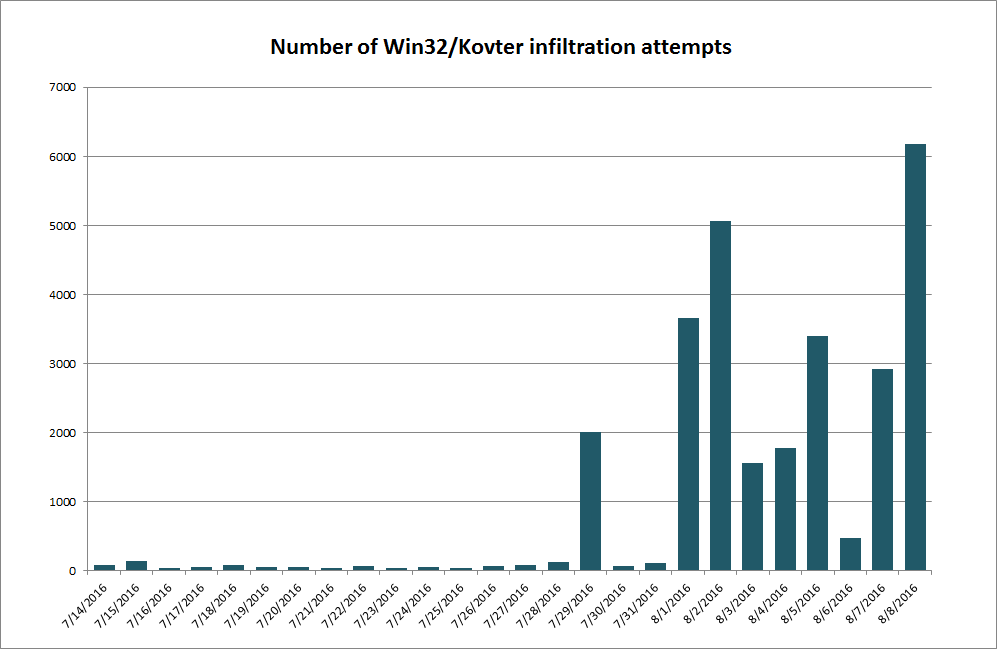
Similar Nemucod campaigns have been around for quite some time. ESET warned the public of the threat in late December, 2015, and again in March, 2016. However, past waves primarily tried to download ransomware families, most frequently Locky or the now discontinued TeslaCrypt, instead of the current ad-clicking backdoor.
How can you avoid this threat?
- If your email client or server offers attachment blocking by extension, you may want to block emails sent with .EXE, *.BAT, *.CMD, *.SCR and *.JS. files attached
- Make sure your operating system displays file extensions. This helps to identify the true type of a file in case of dual extension spoofing (e.g. “INVOICE.PDF.EXE” is not displayed as “INVOICE.PDF”).
- If you frequently and legitimately receive this type of files, check who the sender is and if there is anything suspicious, scan the message and its attachments with reliable security solution.




