Instagram users have been the target of several new credential stealers, appearing on Google Play as tools for either managing or boosting the number of Instagram followers.
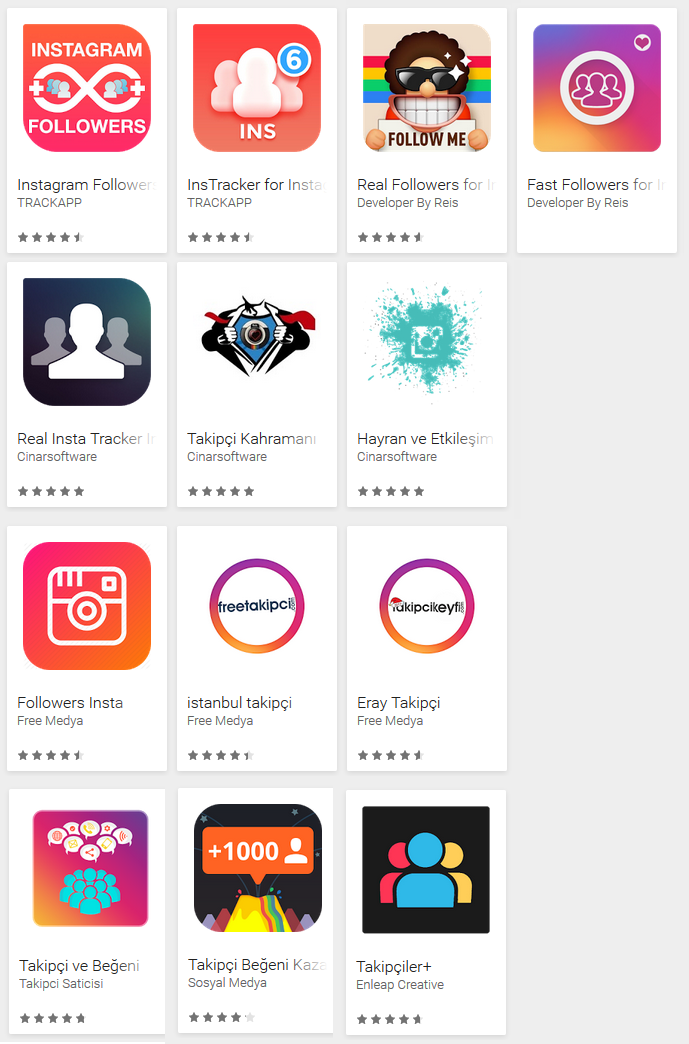
Figure 1 – The malicious apps on Google Play
Under the detection name Android/Spy.Inazigram, 13 malicious applications were discovered in the official Google Play store. The apps were phishing for Instagram credentials and sending them to a remote server.
While they appear to have originated in Turkey, some used English localization to target Instagram users worldwide. Altogether, the malicious apps have been installed by up to 1.5 million users. Upon ESET’s notification, all 13 apps were removed from the store.
How do they operate?
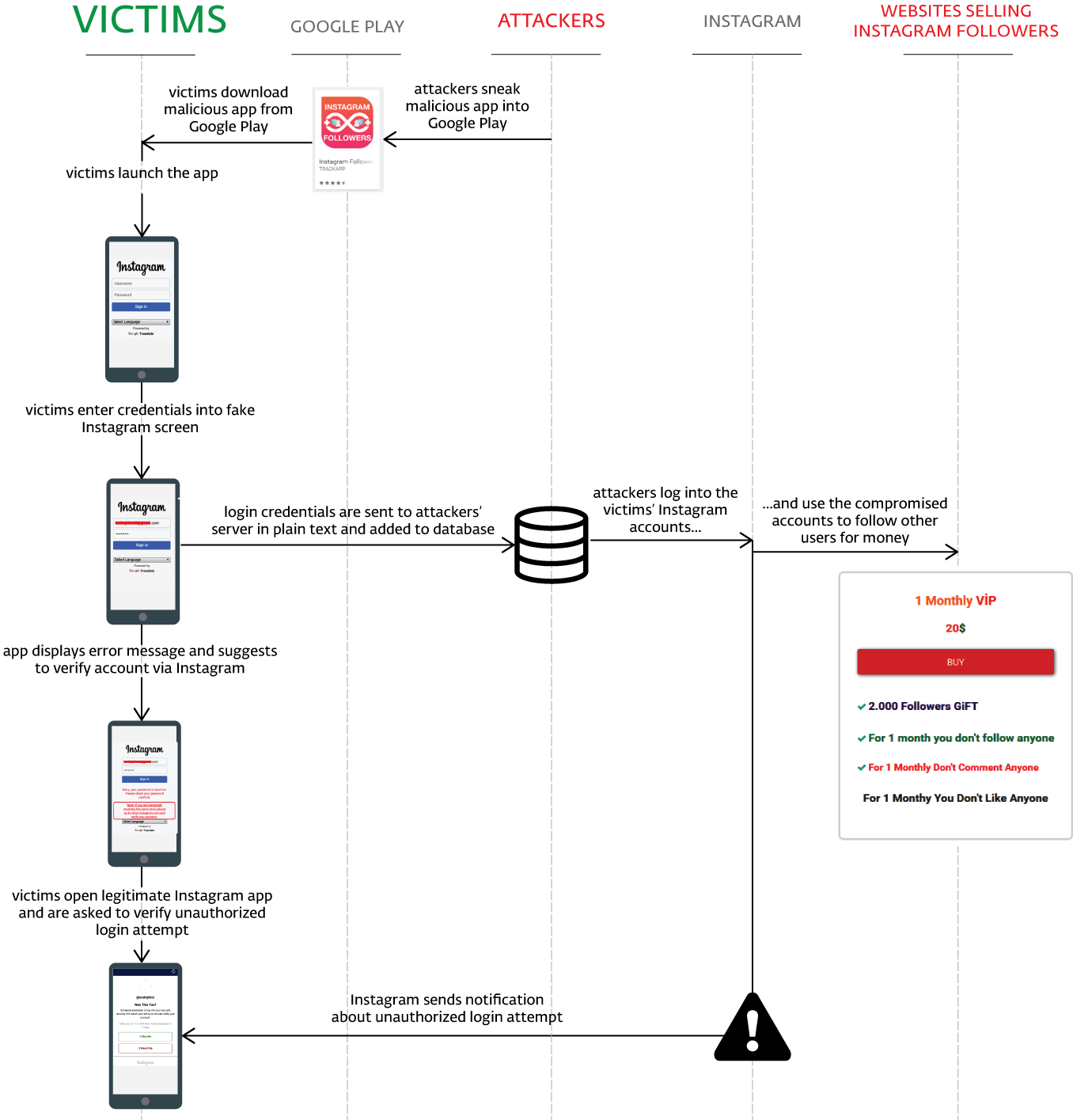
All the applications employed the same technique of harvesting Instagram credentials and sending them to a remote server. To lure users into downloading, the apps promised to rapidly increase the number of followers, likes and comments on one’s Instagram account.
Ironically, the compromised accounts were used to raise follower counts of other users, as we explain later in the article.
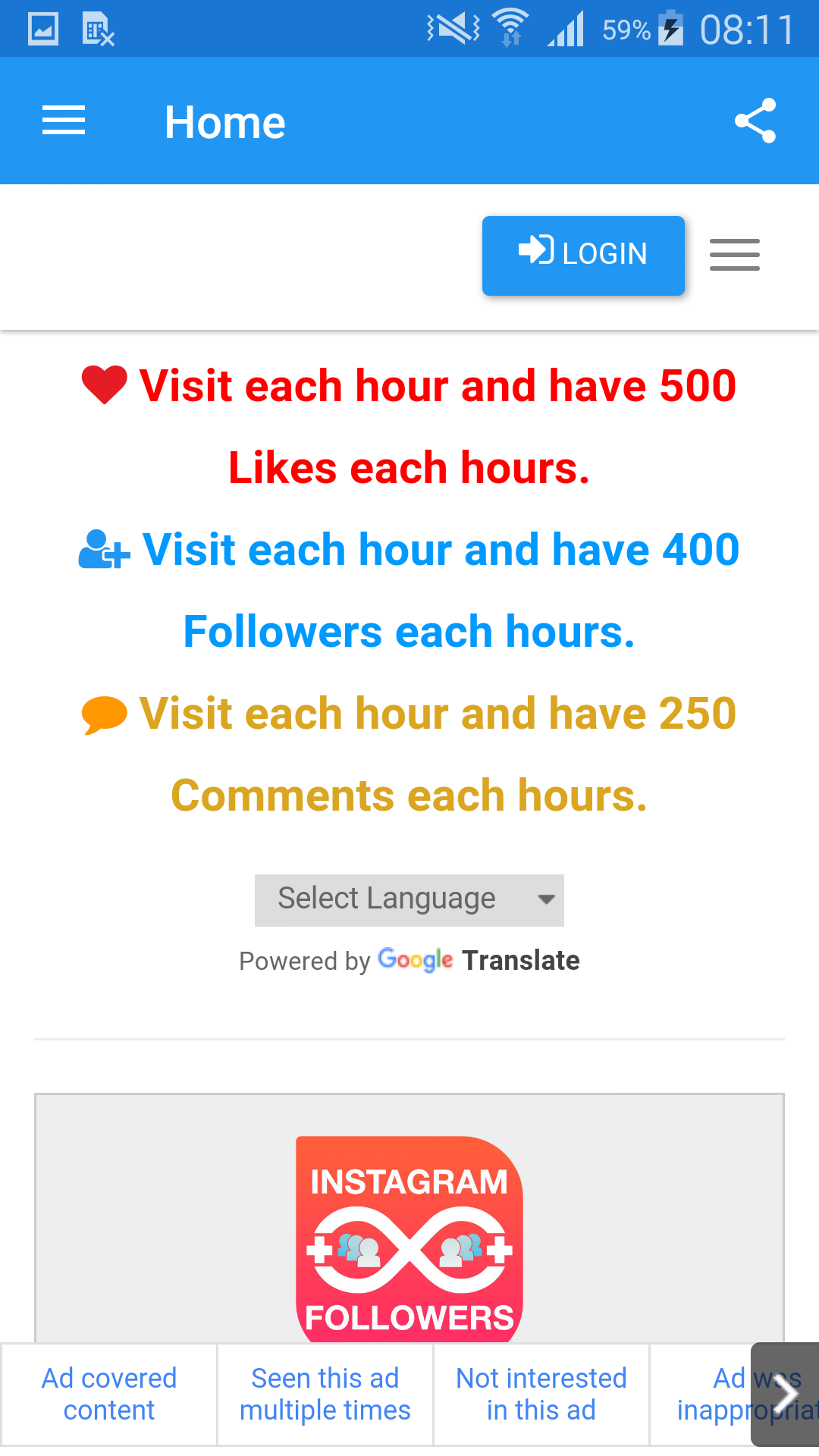
Figure 2 – “Instagram Followers” promising to boost Instagram engagement
As shown in the following screenshot from our analysis of one of these apps – “Instagram Followers” – it requires the user to log in via an Instagram lookalike screen. The credentials entered into the form are then sent to the attackers’ server in plain text. After having entered the credentials, the user will find it impossible to log in, as explained in an “incorrect password” error screen.
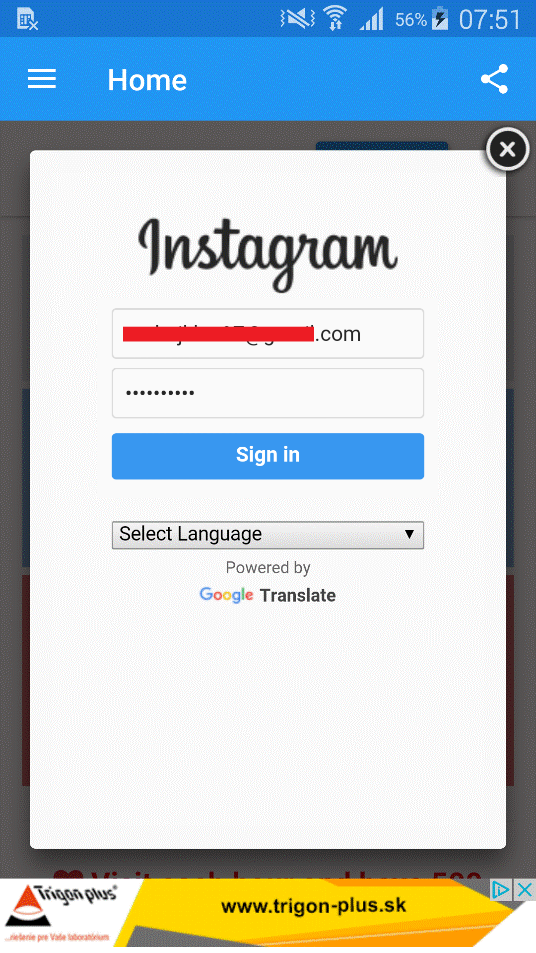
Figure 3 – Instagram login lookalike screen
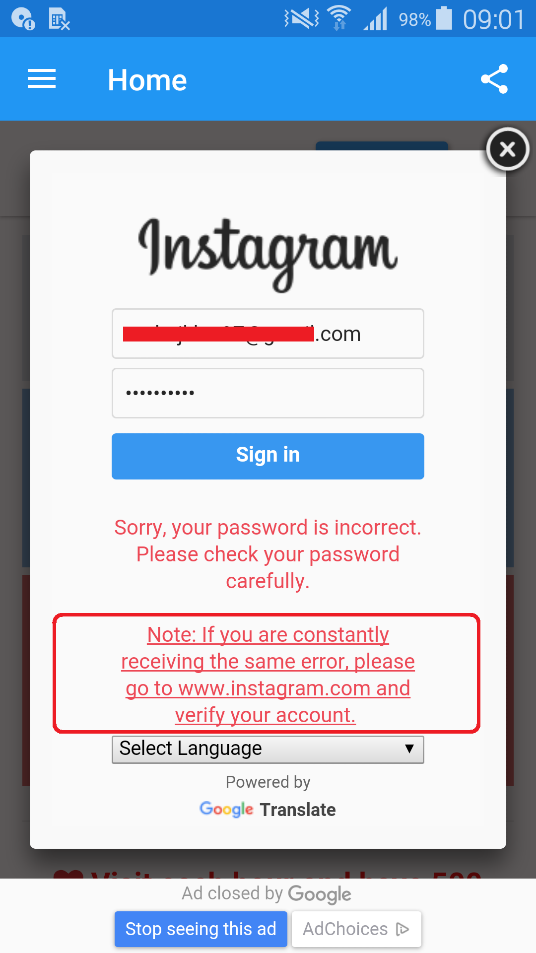
Figure 4 – “Incorrect password” error preventing the user from logging in
The error screen also features a note suggesting the user visits Instagram’s official website and verifies their account in order to sign in to the third-party app. As the victims are notified about unauthorized attempt to log in on their behalf and prompted to verify their account as soon as they open Instagram, the note aims to lower their suspicion in advance.
Figure 5 – Official Instagram notification about unauthorized login attempt
If the attackers are successful and the user doesn’t recognize the threat upon seeing Instagram’s notification, the stolen credentials can be put to further use.
What happens to stolen credentials?
You might ask yourself: What use is there for a couple of (hundred thousand) stolen Instagram credentials?
Apart from an opportunity to use compromised accounts for spreading spam and ads, there are also various “business models” in which the most valuable assets are followers, likes and comments.
In our research, we’ve traced the servers to which the credentials are sent off and connected these to websites selling various bundles of Instagram popularity boosters.
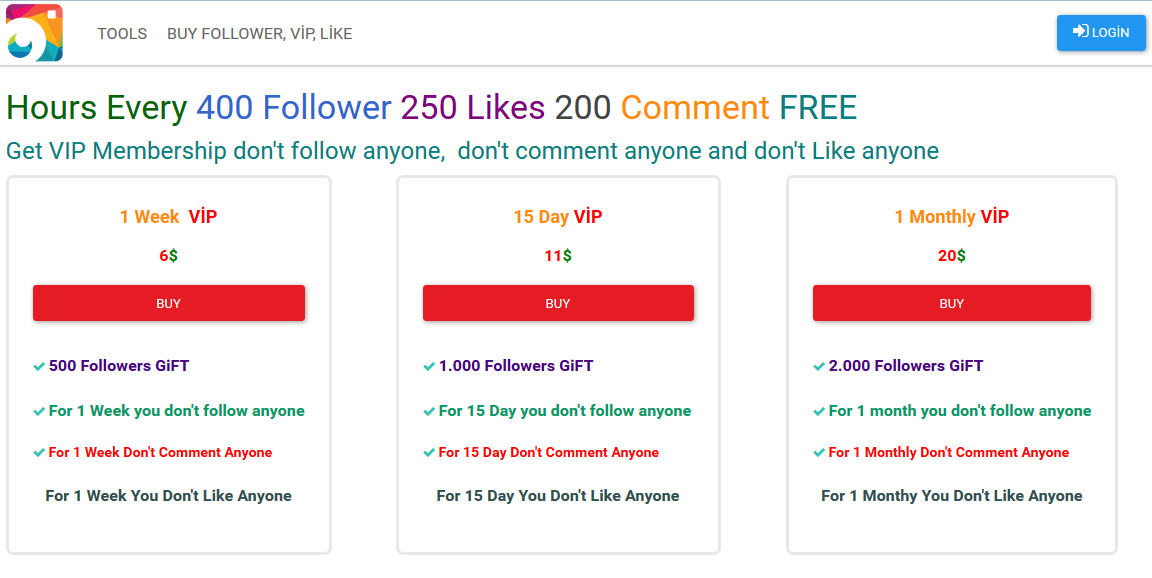
Figure 6 – Websites selling Instagram followers
The following scheme explains how this works:
How to protect yourself?
If you’ve downloaded one of these apps, you will find one of its icons under your installed applications. You will also have seen a notice from Instagram about someone attempting to log into your account, as shown in Fig. 4.
Finally, your Instagram account might appear to have increased following and follower numbers, or you might be getting replies to comments you never posted.
In order to clean your device, uninstall the above mentioned apps found in your Application manager or use a reliable mobile security solution to remove the threats for you.
To secure your Instagram account, change your Instagram password immediately. In case you use the same password across multiple platforms, change these as well. As malware authors are known to access other web services using the stolen credentials, you are advised to use a different password on each of your accounts.
To prevent your social media accounts being compromised, there are a couple of things to keep in mind when downloading third-party apps from Google Play:
Do not insert your sensitive information into untrusted login forms of third-party apps. To verify whether an app is to be trusted, check the popularity of its developer by numbers of installs, ratings and, most importantly, content of reviews.
However, don’t be too quick to jump to conclusions, as many of the ratings and reviews can’t be trusted. When in doubt, opt for high-quality apps marked as Top Developer or found in the Editor’s Choice category.
Last but not least, use a reputable mobile security solution to protect your device.
Samples
| Package Name | Installs | Hash |
|---|---|---|
| com.vavetech.superapp | 100,000 - 500,000 | 84E2A528571CE26735CC6EFE2F20D024F67B6F4F |
| com.instatakipcibegeni | 100,000 - 500,000 | F956C5ECFDB9939E98A3FEDEA877E2DAF91DA0CF |
| takipcivebegeni.app | 100,000 - 500,000 | E278821B390C3DD589A8B62E2CCA73E4AAFEEA98 |
| com.tr.takdrfsfaewewe | 10,000 - 50,000 | 470B9B632F4B66487010725CA84BC4923BFE5898 |
| com.tr.instracker | 1,000 – 5,000 | BA5E2937C57726CC8CCFCBA4034F02D6DD5BBC17 |
| com.tr.nsgrfllowers | 1,000 – 5,000 | F32C674DBA78A748256991A7DBB2409FDA0CF302 |
| com.tr.sdfgbvcderfdf | 1,000 – 5,000 | 80E0A0704D256A0D4A02AD894A6206D93010E554 |
| com.tr.yfASTngdYRl | 500 – 1,000 | 91CE430EA41F04C38EEB150F5E96928A0448263F |
| com.tr.insfollowfreeinsta | 500 – 1,000 | D73F268D46DDD3213B82DC288428701EA09FB949 |
| com.tkpcikahramani | 500 – 1,000 | B5AE6DBF283E0ABA19A896395F86C83808026D68 |
| com.tr.aerfhasFYHDJGXMS | 500 – 1,000 | 2D0AFB6B4BBB9C04BE826CA119CD6368A32A1289 |
| com.tr.aedgcawwwSSSjkm | 100 - 500 | 1757E843C80533C5DC7CF0699BB1D55147FFB349 |
| com.tr.aerfateharydar | 0 - 5 | E79050338EC9BBDC70DB8CAA4DC08EF3DAF0BA11 |




