Update: For those interested in more information we will be reviewing the latest in cyber security covered at Black Hat USA 2015 in August 12 at 10 am PDT - join us!
As we published earlier "How's Black Hat 2015", we are covering Black Hat 2015 USA from Las Vegas. If you happen to be there pay us a visit at booth 927, play some foosball and try to beat our team!
This year at Black Hat, the focus was as much on hacking the intersections of data as on a specific computer platform. Don’t have a desktop computer anymore? Not to worry. The web site you regularly visited gets hacked and spews the data you gave it out across the globe, all at record speed. Got a mobile device? I’m sitting in a presentation showing how to handily root an Android device (along with suggestions on how to fix it). Got a new e-fridge? Yeah, they thought of that.
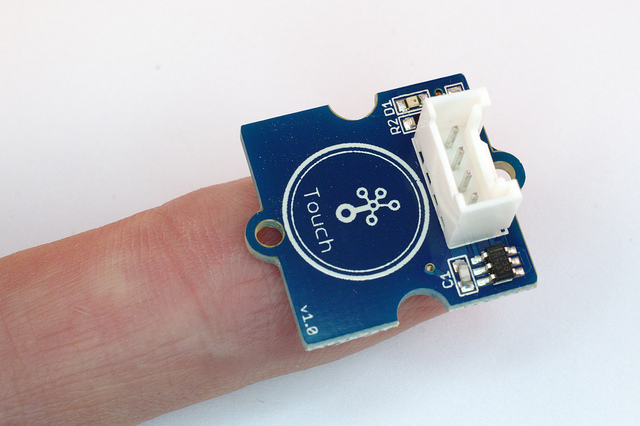
You see, many of the platforms being trotted out live or die by how fast they can reach the marketplace, not on how secure they can keep your information. The difference is now you have 30 e-devices you interact within your home, car and office, instead of a couple.
This means the scammers have an easier time hacking a particular platform or doodad you don’t think much about, and use it to pivot to other targets, harvest your information or perpetrate a host of other nastiness. Oh, and these devices are always on, which is handy if you’re hacking from the other side of the globe.
"This year the focus was as much on hacking the intersections of data as on a specific computer platform."
Hackers seem to be looking far and wide. One presentation focused on critical infrastructure honeypots set up to detect scammers attempting to fiddle with the knobs and dials of a petroleum-related technology. While it was interesting to note the source IPs involved and map them to a particular country, the better question is why scammers would be so interested in a target like this unless they had further intent. After all, it costs hackers time and money to do reconnaissance just like it costs you money to defend against the same. It’s hard to imagine why they would spend the efforts at digitally “shaking the front door to see if it’s locked” if they had no intention of digitally entering.
This year the tenor at the show was firmly rooted in hacker culture, which doesn’t always translate to traditional news media. Hype about stellar upcoming after-show parties replete with hacker tricks to be revealed when you get there has already translated into headlines some news venues struggle to fully explain.
Let’s just say that tips heard on the floor of Black Hat goings on may not necessarily be gospel truth. That part is especially true later in the evening at the party where you hear the “truth”. Also, discerning the finer details of a given exploit while competing with a deafening DJ mixing 90’s dance music with an electric violin (really) may not make for accurate rendering for mass media consumption.
"It is also true that if you hear it at Black Hat, it is a harbinger of what the word on the street will be soon."
It is also true, however, that if you hear it at Black Hat (even if somewhat slurred), it is a harbinger of what the word on the street will be soon. So next year brace for a mess of attacks against the IoT devices you pick up on the cheap, not to mention your old home router that manufacturers have no plan of fixing, or your new e-home security system, all managed from a simple button on your mobile device. Not that the bad guys are about to push that same button digitally and unlock your doors, but that kind of risk would certainly seems bound to be a focus of the security aware commentator in the coming years.