The Black Hat conference in Las Vegas this week is a major event in the cybersecurity calendar, happening every summer, and delivering a large amount of fresh security knowledge as well as a wide range of security training. So what can we expect from Black Hat 2015? We already know about a couple of the "headline" briefings owing to the growing tradition of media previews for some of the more attention-grabbing exploits, like car hacking and gun hacking (yes, gun hacking). I will get to these in a moment, but first some practical tips for those who will be at Black Hat and those who won't.
Maximum Black Hat
1. Have a plan. Decide what you expect to get from the event and plan accordingly. Are you going there to learn? If so, what are your key learning objectives? Are you going for the networking? If so, with whom and where? Can you set up meetings ahead of time? Without a plan you risk coming away from Black Hat feeling worn out but less than satisfied, like you failed to make the most of the opportunity. (See my final tip for a way to redeem the experience.)
As you do your pre-event planning, try to set realistic expectations. You probably can't go to every session you want/need to attend (unless you have mastered the art of being in two places at the same time). Of course, if you are going as part of a team, you can split up to expand your coverage and share notes later. Also accept that there may be chance encounters that lead you in unplanned, but instructive and/or productive directions.
2. Download the schedule now. One key to productive planning is the schedule. Start looking at it as soon as you can (there is a handy link to a PDF here). Highlight the sessions/briefings that interest you most, realizing that some may overlap. You can then make a second pass to narrow your choices down (and avoid the need to clone yourself). Personally, I would plan to attend the keynote on Wednesday and get there early to be sure of a seat. This session often sets the tone for the event, and this year's speaker, Jennifer Granick, is one of the finest minds in this space (and if my mind is not failing me, I first met Ms. Granick in 1995 at my first DEF CON talk, and I know she spoke at DEF CON 6 in 1998).
Other sessions of exceptional interest? That really depends on your personal and professional interests, but here's one briefing that got my attention: Repurposing OnionDuke: A Single Case Study Around Reusing Nation State Malware. I'm hoping this research will provide some solid proof points in an argument that antivirus experts have been making for decades: there is no good malware. You can find the story of this argument in a paper I co-authored: Malware is called malicious for a reason: The risks of weaponizing code.
Sadly, because there are people in government who still think they know better than the experts, weaponized malware is a current and present danger to the Internet. (In my opinion we should be protesting against it like we protested nuclear weapons.) The central technical argument in this debate, which this briefing looks set to demonstrate, is that nation state deployment of malicious code might as well be called "cyberweapon gifting to the bad guys." So, check out this Forbes preview article and the briefing by Joshua Pitts (9:45AM Thursday, in Mandalay Bay BCD).
Another session on my list, and not just because it features one of ESET's own researchers, Eugene Rodionov, is this: "Distributing the Reconstruction of High-Level Intermediate Representation for Large Scale Malware". What this briefing demonstrates is something that happens a lot behind the scenes in the security industry: security companies, such as Intel and ESET in this case, collaborate on research aimed at improving everyone's security. In this case the improvements are in malware analysis techniques at scale (Wednesday, August 5, at 3PM, South Sea GH, with more details here).
I will have some more thoughts on the headline making sessions in a moment but first, some homework.
3. Do some homework. I suggest reading the 2015 Black Hat Attendee Survey (PDF) survey to get a sense of what security professionals think is important right now. For example, 57% of those surveyed said that "sophisticated, targeted attacks" top their lists of concerns. However, only a quarter said that targeted attacks were among the top three IT spending priorities in their organization. Even less, one in five, indicated that targeted attacks were among the top three tasks on which they got to spend most of their time. All of which suggests that headline grabbing device hacks and vulnerabilities in the Internet of Things are not top of mind for corporate IT security folks right now. On the other hand, social engineering attacks, often discussed at Black Hat and even more so at DEF CON, were cited as a top concern by 46% of those surveyed. Sadly, these concerns were also thought to be shortchanged by companies in terms of time and budget.
Another useful piece of homework is to load up on trail mix before you head to Vegas. The trail from your hotel room to the briefings could be a brisk 15 minute walk. Although there are plenty of eating places in the hotel, they often have long lines, not to mention high prices (I found it hard to find get warm food with a beverage for under $18 last year). Also consider your caffeine strategy. The lines at the Starbucks are usually very long at those times that you normally feel the need for coffee. (There may be a sponsored relaxation area near the briefings, but last year the coffee there cost $5 a cup, and that was basic coffee, not espresso.) And then there's the need to stay hydrated. A pro-tip from ESET researcher Cameron Camp is to have your cab driver stop at a convenience store on the way in from the airport to the hotel; pick up a 30 pack of bottled water for a fraction of the price they charge at the hotel.
Trucks, cars, guns, and other hacks
For many years, Black Hat has generated pre-conference announcements that catch the media's attention, and this year is no different. Widely anticipated is the technical briefing on the hacking of a Jeep Grand Cherokee that was featured in WIRED (and about which I have already opined here). This is another big TAW4: Threat About Which the World Was Warned (pronounced "tor-for"). There is some controversy around this one, with some well-respected security researchers disapproving of the way the exploit was demonstrated, namely on a public highway. On the other hand, it could be argued that this very "real" aspect of the demonstration was required to end the complacency that in the past has greeted mere parking lot demos of vehicle hacking. Indeed, if Fiat/Chrysler/Jeep/Dodge had heeded the warnings issued by security researchers in years gone by, then they could have saved millions of dollars in direct costs to fix the vulnerability that some of their vehicles possess right now, not to mention the untold tens of millions in brand damage. The briefing is Remote Exploitation of an Unaltered Passenger Vehicle by Charlie Miller and Chris Valasek, 4:00PM Wednesday, Mandalay Bay EF.
Another pre-conference story that has gained some press attention is the hacking of a "smart rifle" which was also highlighted by WIRED. Here again, the manufacturer seems to have missed some very basic security precautions. Obviously, there are not many smart guns on the streets right now, so the main point of this research, at least for me, is the further evidence it provides that manufacturers of things are failing to get security right when they try to add these things to the Internet of Things. The briefing is When IoT Attacks: Hacking a Linux-Powered Rifle by Runa A. and Michael Auger, 2:30PM Thursday, Lagoon K.
If you use GPS, for targeting or driving or whatever, you might want to catch the session on GPS devices which connect to the Globalstar satellite network. Apparently they are vulnerable to man-in-the-middle hacking, as reported in Reuters. Colby Moore will be doing the briefing Spread Spectrum Satcom Hacking: Attacking the GlobalStar Simplex Data Service on Wednesday at 10:20AM in Southseas GH.
Continuing the car theme, and the argument that big companies spend too little time thinking through cybersecurity implications in the product development life cycle, there is another vehicular hack, reported here by Reuters. This session is at DEF CON, not Black Hat, but many people extend their stay in Vegas for the weekend to take in both events. If you have the stamina, it is worth doing. This particular session is Drive It Like You Hacked It: New Attacks and Tools to Wirelessly Steal Cars. Be sure to get there early as popular DEF CON talks can fill up.
Final Takeaways
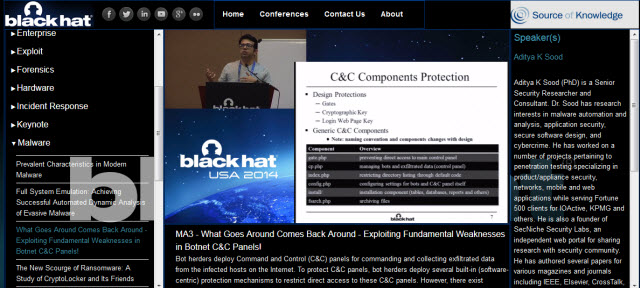
If you can't get to all the sessions, don't worry. You can buy recordings. In previous years I have found the quality of these to be very good. I got the 2014 sessions, Black Hat and DEF CON, delivered to me about 35 days after the events. They arrived on a pair of USB keys but also came with online portal access, which is very handy. As you can see here, there is video of the presenter alongside the slides.
You will get info on how to order the recordings when you check in (the vendor Source of Knowledge will have booth next to Exhibitor Registration on Level 2).
Finally, don't forget to have some fun. There are numerous diversions in Vegas, but Black Hat itself provides many, like the foosball competition at the ESET booth in the exhibit hall. Stop by booth 927 and test your skills.