Video games, websites and even apps are all in the sights of hackers hungry for better scores, more money and public notoriety.
In the world of cybersecurity, some targets are obvious. For example, financial service providers and the retail stores aren't rarely targeted as they hold lots of money. Hacking a media organisation, meanwhile, can sometimes give cybercriminals publicity.
Other victims, though, are perhaps more surprising. Take hackers’ fascination with game services.
Gaming companies don’t seem like an obvious choice for cybercriminals, and yet one of the biggest hacks of all time, of Sony’s PlayStation Network in 2011, reportedly resulted in 77 million account holder details being compromised, 12,000 credit card details being leaked, and the company’s stock price crashing overnight.
Hackers go after gaming services for many reasons, from seeking cheats to trying to exploit the value of digital game copies and in-game items. And at the top of that chain is stealing from the games developer itself - in April, for instance, we reported that one teenager in Indiana pleaded guilty to being involved in a hacking ring that was said to have stolen data worth more than $100 million from one major games developer.
With that in mind, we look at five of the ways attackers are targeting games companies and their users.
1. DDoS attacks to cause disruption
Denial-of-service (DoS) or distributed denial of service (DDoS) attacks are often used by attackers to take down a website or web service, by essentially flooding the recipient’s web server with too much traffic – thus making the server ‘fall over’ and the service go offline.
A number of so-called hacktivism groups, including ‘Lizard Squad’, have used DDoS attacks in the past, including on gaming sites. Perhaps most famously, the Lizard Squad knocked Sony’s PlayStation Network and Microsoft’s Xbox Live offline last Christmas Day, causing thousands of gamers to be unable to access both services.
DDoS attacks also played a starring role in the 2011 breach of Sony PlayStation Network, while security vendor Incapsula said that one unnamed video games provider faced a prolonged 38-day DDoS attack last year.
Fortunately, DDoS attacks can be quite quickly recovered from and more often result in embarrassment rather than financial or data loss.

A series of DDOS attacks knocked Sony's PSN network offline for Christmas Day last year.
2. Spoofed websites for grabbing credentials and more
Malware unfortunately gets dished up on all kinds of websites, and that can include both legitimate websites from reputable businesses and faked websites designed to steal from unsuspected users.
Forbes reports that Amazon’s $600 million game streaming service Twitch saw its website become infected with malware back in March, but more often hackers look to direct users to copied or spoofed websites in order to unknowingly infect them with malware, to steal their log-in credentials or even so to spread their malware onto more victims.
This was the case earlier this year when it was discovered that a fake Steam webpage was being used to propagate malware. Or indeed, earlier this week when malware was discovered in seemingly legitimate games including Cowboy Adventure and Jump Chess.
3. Stealing money with ransomware and scareware
Ransomware on a game? That seems unlikely, right? Wrong. This March it was discovered that cybercriminals were infecting gamers’ machines with ransomware, stopping them from playing their favourite games, and requiring Bitcoin payment in exchange for the safe return of their encrypted game files.
Once infected, the malicious program would seek out the users’ saved games and encrypt them. The victim would have to pay at least $500 (£340) in Bitcoins to get their games back.
The malware was said to affect 40 separate games, including favourites like Call of Duty, World of Warcraft, Minecraft and World of Tanks.
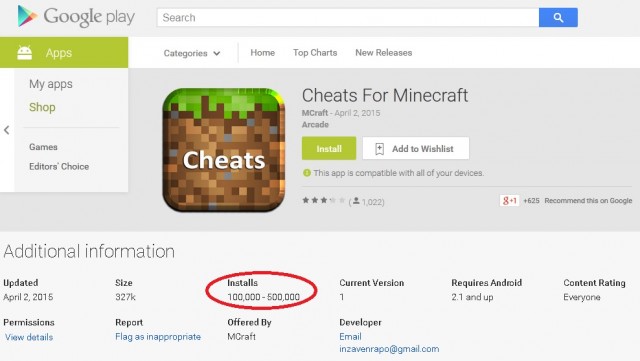
Cybercriminals also look to make financial gain through scareware apps. In May, ESET revealed the discovery of 30 scareware Minecraft apps on Google Play. In this case, the apps – which pretended to be cheats for the Minecraft – falsely claimed the users’ machine had a virus, which could only be removed by activating a premium-rated SMS subscription that would cost 4.80 EUR per week.
4. Brute force attacks and keyloggers to spy on passwords
Attackers are always after log-in usernames and passwords, and this is largely irrespective of what sector the victim's business happens to be in. Gaming sites are not exempt from this, as Sony, Ubisoft and others will testify.
That said, with a number of attackers being gamers themselves, and with gaming offering numerous rewards, it’s easy to see why one of them might want your log-in details for GTA or Assassin’s Creed.
The most common way of getting these is via simple guessing, but attackers will also likely look to carry out brute force attacks (an attempt to crack a password by using a library of passwords), and keystroke logging (software to record the keys struck on a keyboard).
5. Social engineering for all of the above
Attackers are leveraging social engineering techniques, like phishing, to scope out and attack their intended victim.
For instance, perhaps he would look you up on Twitter or Facebook before sending targeted spear phishing emails directing you to a spoofed website. Or maybe the same email would be sent with a weaponised document containing malicious code.
Steam users found out the hard way last November, after a free screensaver phishing scam, in which the screensaver secretly contained a hidden Trojan.
Phishing was also used in an advanced cyber-attack, as documented by Dell SecureWorks last July. Security researchers said then that a group, codenamed Threat Group-3279 (TG-3279), was hitting the video games industry with a wave of cyber-attacks designed to steal source code, with aim making these games free to use, to develop tools to cheat, or to use the source code for competing products.
Crucially, Dell said that the attackers would carry out initial reconnaissance work on the intended victims (for that, read social engineering), before launching their attack.
PlayStation photo: oneinchpunch / Shutterstock.com