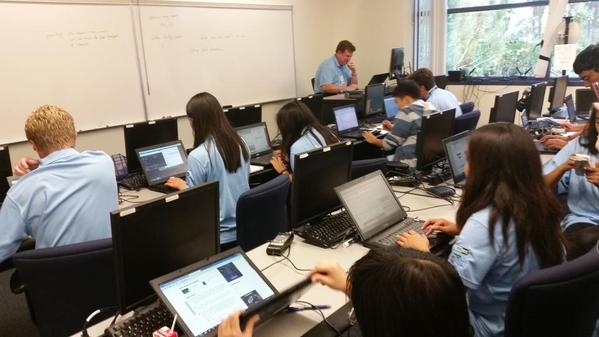
Last week, I participated in a program that aims to develop the skills, mindset, and moral code required defend networks against criminal abuse: Cyber Boot Camp. This annual event is a joint project of Securing Our eCity and ESET, with the help of numerous volunteers and sponsors. This year, five days of intensive education were delivered to some four dozen students between 12 and 18 years of age, on a campus of National University in San Diego. Students achieve a place at Cyber Boot Camp through participation in the San Diego Mayors' Cyber Cup. My team and I were there as part of ESET's commitment to both cybersecurity education and the local community. (ESET's North American headquarters are in San Diego, California.)
 I can honestly say that I learned a lot during those five days, and I was one of the instructors.
I can honestly say that I learned a lot during those five days, and I was one of the instructors.
I'm pretty sure the students learned a lot too, under the leadership of fellow ESET security researcher, Cameron Camp, the technical genius behind the "target" network that the students are encouraged to explore/attack throughout the week.
Each day, guest speakers brought insight and information to the camp, including the law enforcement and military perspectives. This year, the camp included sessions on drones and mobile devices as penetration tools. From Aryeh Goretsky, ESET Distinguished Researcher, students learned about Android malware as well as Advanced Persistent Threats. A foundation class in network architecture and breakout sessions on coding and encryption were provided by Gene Anderson, a cybersecurity systems designer with Leidos who is also an Adjunct Professor at UCSD. Roger Fraumann, another San Diego CISSP, did a class on security issues with the Apple Mac OS X platform.
7 lessons
On the final day, I challenged students to write their own account of the camp and I hope to publish some of those accounts here in the coming weeks. The following are some of the lessons that I saw students learning during the course of the week.
1. Do not leave your computer unlocked. A basic lesson, yes, but one that many companies fail to impart to employees. Students who were assigned laptops for hands-on sessions in the War Room soon found that other students were playing the role of adversary. People got locked out in various ways when they left their machine running with no password or a weak password. Later in the week the instructors had to impose a moratorium on changing BIOS passwords (there is only so much "reality" you can simulate in a classroom, although Cyber Boot Camp takes things beyond most schoolroom classes).
2. Denial of service is shamefully easy. The three pillars of information security are Confidentiality, Integrity, and Availability. One common attack against the last of these is Denial of Service, or DoS, which can be executed by one machine, or by multiple machines - known as a distributed denial of service or DDoS. You can reduce the availability of a system to do its legitimate work by sending it loads of bogus requests for information. Criminals do this as part of extortion schemes and some people do it out of spite, hiring so-called "booter" services that are basically DDoS for hire, often disguised as "system stress testing". While denial of service is a real problem for companies, it is a fairly crude attack and not one to be proud of.
3. Understanding network basics is key. It is entirely possible to use a network without understanding how it functions, but if you are trying to attack or defend a network, you really need to understand network architecture and protocols. Students from different schools had different levels of network knowledge (see lesson 4 for more on why that might be). To make sure everyone had the same baseline understanding, Gene Anderson put on a foundation class in network architecture that was very helpful.
4. Understanding computer basics is also key. Believe it or not, many schools in California don't offer computer science classes, so even though you might use computer applications in class, like Microsoft Word or Excel, you don't get a foundation course that explains things like BIOS, OS, FAT, MBR, GUI, CLI, OSI, TCP/IP, SMTP, and such. Some students may learn this stuff after hours in Computer Club, but there could be gaps in knowledge, and those gaps can translate into vulnerabilities (see #1). It's pretty clear that the bad guys spend time studying the basics -- malware writers for example sometimes do clever things with the Master Boot Record (MBR) to achieve persistence on an infected machine.
5. Cyber is everywhere. While the boot camp classrooms provided an array of network targets to explore, we also went mobile, exploring the ways in which digital technology impacts everything from mobile communications and satellites to Unmanned Aerial Vehicles or UAVs, also known as drones. We learned how GPS can be used to keep a drone at a fixed location, even when there's a wind. But beyond this, some instructors talked about how careers like law and law enforcement also need people with good knowledge of cybersecurity.
6. There's a shortage of people with cybersecurity skills in America. Many instructors pointed this out. And in fact, the shortage is also global. There was a credible report published earlier this year that estimated the shortfall in the global information security workforce will be 1.5 million in five years. So, unless human beings suddenly stop committing online crime, there should be well-paid jobs in this field for many years to come.
7. Communication skills are also important. Being a total geek and getting deep into coding and networks and such can be a lot of fun, and rewarding, but it also helps if you know how to communicate. If two people of equal skills and experience apply for a cybersecurity job, the employer is likely to hire the one with the better communication skills. The security workforce survey mentioned in #6 found that 90% of security professionals rated "communication skills" as a key contributing factor to being successful in security, sharing the top spot with "broad understanding of the security field" among all success factors (and ahead of technical knowledge).
Bonus tip: Takes notes. Mr. Goretsky pointed out that we can get so used to doing things on computers and phones that we forget to write down all the things we need to remember, or that should be documented. So he gave us all paper notebooks and pens and a lesson in how to take notes so that they can assist your research, capture lessons learned, record meetings, and document good ideas you have.




