(Update 2/25/14: Apple now has an update to fix the SSL flaw for OS X. Details are here on the Apple site.)
If you use an iPhone or an iPad, right now would be a good time to install iOS 7.0.6. You can do this via the Settings icon, under General, where you will see something like the screen below.
 Now I'm guessing that a lot of people who use iPhones and iPads won't be entirely clear about what "a fix for SSL connection verification" implies. After all, this is fairly technical language, as is the explanation of the problem that Apple provides here.
Now I'm guessing that a lot of people who use iPhones and iPads won't be entirely clear about what "a fix for SSL connection verification" implies. After all, this is fairly technical language, as is the explanation of the problem that Apple provides here.
(Update: this problem also existed in numerous versions of Mac OS X, but has now been fixed in the 10.9.2 update.)
The practical implication of the problem is clear, as our good friend Graham Cluley puts it, until you update your i-device or Mac it will have "a critical vulnerability that could allow hackers to intercept what should have been secure communications between your device and SSL-protected websites."
SSL is what online banks and stores use to protect your electronic interaction with them. It is signified by the little padlock icon that shows up in the browser address bar, next to "https://address" and so on. As Graham notes, the problem Apple is fixing with this update potentially means that "online attackers could grab your userid or passwords as you attempted to log into popular websites."
Since SSL is also used to verify software updates, sometimes called patches, those present another possible avenue of attack for the bad guys looking to take over these devices. What does that mean? You should perform your iOS 7.0.6 or Mac OS X 10.9.2 update over a trusted network, not the open Wi-Fi at your local coffee shop (unless you know the owner is also security geek or you're a security pro yourself and installed the system for her).
At this point my main concern is that the bad guys have reverse engineered the fix and now know how to target the vulnerability on unpatched systems. A serious secondary concern is that not everyone with an i-device is seeing a message from Apple urging them to upgrade. In the past, I know the Settings icon on my iPhone has sported a numeric badge telling me that I need to upgrade, but I have not yet seen one for iOS 7.0.6. (and a non-scientific survey of friends tells me I am not alone).
Another potential obstacle to rapid and universal plugging of this attack vector is that "a fix for SSL connection verification" does not read like an appealing reason to upgrade, particularly for the millions of users who have no idea what SSL is, despite using it every day. So let me just repeat that this is an important update. Encouraging friends and family who have iOS devices to go ahead with the update is the right thing to do.
As for Apple Mac laptops and desktops, the situation is that they too have this SSL vulnerability and the update is not yet released. If you, like me, are using a Mac, you need to stay alert for the release of the fix and install it right away, over a known good network.
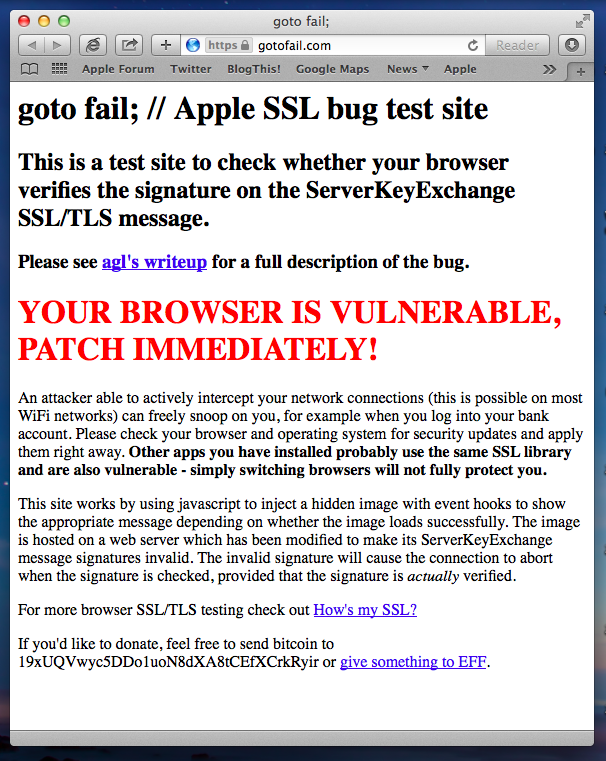
One precaution you can take is to use Firefox or Chrome as your browser as these will abort vulnerable connections. You can check this using a web page at gotofail.com. The results from Safari on my Macbook Air right now says this:
As of 2/25/14 we have updated We Live Security with information about the Mac OS X update. Let me leave you with one more tip, this from our good friends at CrowdStrike:
- On unpatched mobile and laptop devices, set “Ask to Join Networks” setting to OFF, which will prevent them from showing prompts to connect to untrusted networks.
Have any questions on this issue? Leave us a comment and one of our researchers will respond as soon as they can.




