I recently completed my 14th Virus Bulletin conference paper, co-written with Intego’s Lysa Myers, on “Mac hacking: the way to better testing?” to be presented at the 23rd VB conference in October, in Berlin. The paper itself won’t be available until after the conference, but the abstract is on the Virus Bulletin conference page here. Completing it reminded me that it might be worth rationalizing all (OK, most of...) my conference papers and other publications.
While some may be of more historical interest than topical, most of them still have some validity. Of the 13 preceding papers, all those that were written since 2006, when I first started to work with ESET, are on the WeLiveSecurity conference papers page (by kind permission of VB). All the papers there (written by an impressive range of ESET’s researchers) are listed in more or less chronological order, not by author or by the conference for which they were submitted. However, all 13 papers can now be found on a page of their own on the Geek Peninsula blog site, ordered chronologically.
For good measure, all the Virus Bulletin articles I could lay hands on have a page of their own, too: however, some are just links to their page on the Virus Bulletin web site (which generally means I don’t have an approved and proofed PDF copy), and some are only readable if you download the whole of the issue that included them. The latest, by the way, is an article that appeared in the May 2013 issue of Virus Bulletin.
Articles published since 2006 or so are also available on Virus Bulletin’s own page in HTML format. The most recent articles are only available to subscribers or for individual purchase. Other articles are only available to registered users of the web site, but registration is free. While earlier articles aren’t available individually on the VB site, the whole issue for each of those months is available to registered users.
Some of the articles written since I started to work with ESET around 2006 are also available via the ESET Threat Center articles page (by permission of VB), but not on the WeLiveSecurity blog and papers resources page. Of course, there are many articles there written by other ESET researchers, too.
Some of the conference, workshop and expo presentations I’ve done on ESET’s behalf are available at the Threat Center page here along with presentations by other ESET researchers.
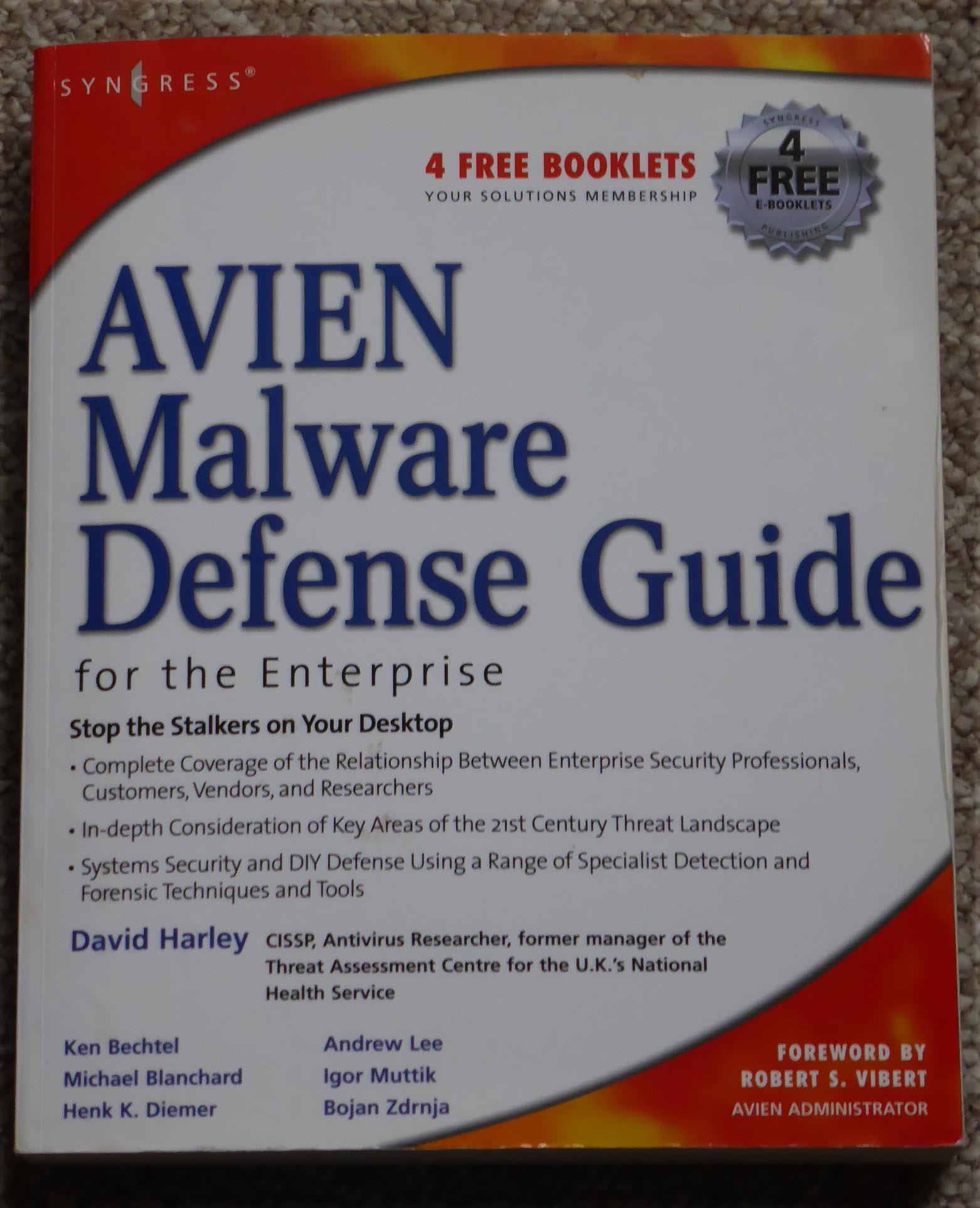
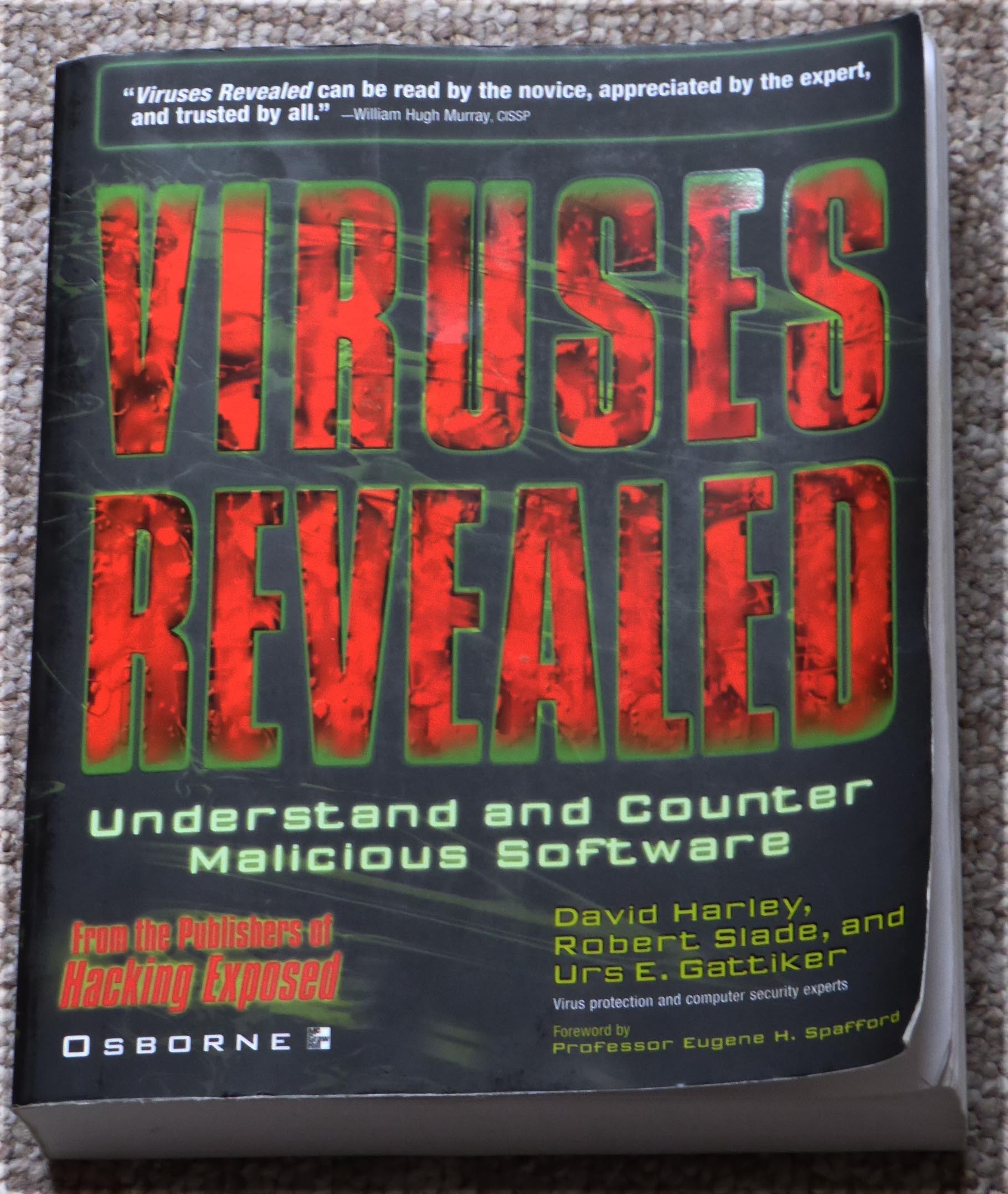
Of course, ESET researchers often write blogs and articles on ESET’s behalf for external sites and periodicals (and conferences) apart from Virus Bulletin, though VB has a special place in every AV researcher’s heart. Especially researcher’s as old as me… I can’t list everyone’s external articles here or on my own page, but an awful lot of mine (awful may be the operative word) are listed by site on Geek Peninsula. There’s even a not-quite-complete list of my (security) books. (The two shown here are the two that demanded the most of my time and energy...)
I can’t really imagine that anyone will want to look up everything I’ve ever written, but there are pointers to most of my security stuff on the Geek Peninsula site. If some future biographer or PhD student in information security thinks they might need more than that, let me know and I’ll be happy to put up a page for my scanned shopping lists, the notepad I keep by the phone, and my cheque stubs. (You think I'm joking? Jack Trevor Story claimed he never threw anything he'd written away, not even shopping lists.)
David Harley CITP FBCS CISSP
ESET Senior Research Fellow
* http://en.wikipedia.org/wiki/My_Back_Pages Not that I’m about to make some drastic change in my own output like composing all future blogs on a Strat. (Yes, that's a very old photograph, and I do own a Strat, but I don't blog on it. Not on security blogs, anyway. )