The Android platform for smartphones and tablets has had its share of security woes, many documented on these pages (I have included a list of relevant articles further down the page). But Android has also earned its share of supporters, a number of whom took me to task a week ago when Frederic Paul of ReadWrite published parts of an extensive interview that I gave right after the RSA Conference in San Francisco.
The Android Windows analogy
The title of Paul's piece was "In the security world, Android is the new Windows" and it attracted a lot of attention. Right now I can see the article has 68 comments and 376 Facebook likes. It has been tweeted 649 times. Not only that, our local NBC station noticed the article and recorded this segment for the evening news (which actually provided some useful fodder for my position on Android security as we shall see later). I figure that a topic this popular deserves some additional attention, starting with a quick explanation of why I think that, in terms of security, Android could be characterized as the new Windows:
Microsoft Windows became widely used, and very popular in some circles, despite being relatively insecure. Later versions of Windows were made more secure. I anticipate the same thing will happen with Android.
I was not referring to the way Android and Windows are architected. And I was not attacking Android. In fact, you could say that mine is a relatively positive perspective on a mobile platform that currently attracts, according to multiple sources, a lot of malware. Consider the recent security report from Trustwave:
As organizations embrace mobility, mobile malware continues to be a problem for Android, with the number of samples in Trustwave’s collection growing 400% in 2012.
Or how about this from our good friends at F-Secure, as reported by Red Orbit:
Android’s share of mobile malware rose sharply in the fourth quarter of 2012, accounting for 96 percent of all attacks.
Of course, ESET has its own stats on Android malware, but I'm holding those back for a moment because of something said by one of the Android fans commenting on Frederic Paul's article:
He [Stephen Cobb] pretty much disqualified himself after he mentioned they [ESET] offer an anti-virus product for Android. If you don't sideload and use common sense, you're fine.
In fact, this one comment pretty much captures the beef that several commentators had with the article, and me. They don't see malware on the Android as a big deal and they think I purposefully overstated the risks involved in using an Android device. My alleged purpose: To sell more licenses of ESET Mobile Security for Android. For the record, I'm not in Sales and Marketing. I am not paid to sell ESET products. My job is to assess a broad range of cyber security threats and articulate their relative importance to people who use digital devices. Here's an example of that:
If I thought using common sense and abstaining from sideloading was enough to keep you safe on an Android device, a position taken by some Android users, then I would tell you that. Right now, based on the scale of Android malware production and the weak points in the Android ecosystem, I don't think that is enough. I recommend installing protection against malware on your Android device.
Research-driven Android opinion and advice
When I was sitting in that Starbucks two weeks ago, talking to Frederic Paul, I was stating my professional opinion about the state of Android security, based on my analysis of a range of sources, most notably the research that my colleagues at ESET have carried out in this area. Here are some highlights of that ongoing research, and ESET's efforts to educate Android users on both the risks and defensive measures:
- Dancing Penguins: a case of organized Android pay-per-install
- Boxer SMS Trojan: Malware as a Global Service
- Don't pay high phone bills: SMS Trojans can trick you via premium-rate numbers
- Trends for 2013: astounding growth of mobile malware
- The Dynamic Duo for Securing your Android: Common Sense and Security Software
- The security of unlocking an Android based device, the future is near?
- Google responds to Android app Market security with stronger scanning measures
- Securing Your Holiday Tech Gifts, Part 2: Android Guide
- Free Android USSD vulnerability protection from ESET now on Google Play
Based on the above and my reading of other resources, such as the TrustWave Report, I think it is entirely true that Android is under attack from profit-motivated malware writers. Need more evidence? Look towards the back of the F-Secure Mobile Threat Report for Q4, 2012 and you can see that Android accounted for 81.5% of the mobile threats classified as "profit-motivated" in 2012 (141 out of 173 families). It is also true that there was a lot more malware targeting the Android platform in 2012 than there was in 2011, and this is where I will use some of ESET's own research:
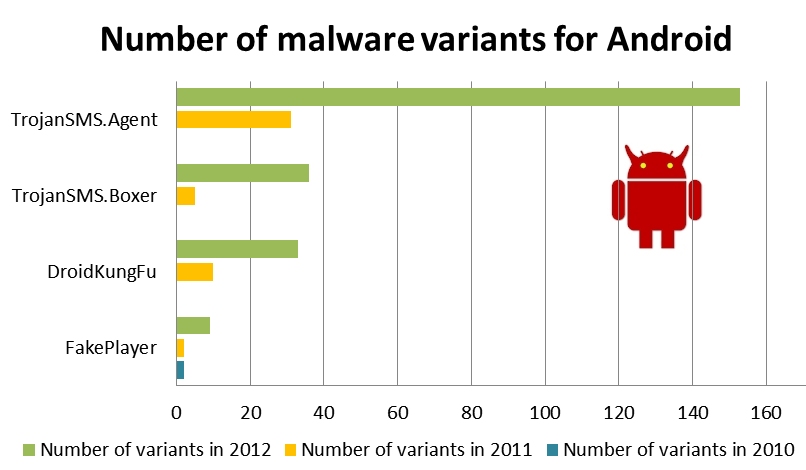
You can see that the number of variants for four different families of Android malware jumped dramatically. This is a strong indicator of increased activity by those who distribute malware. These ESET numbers are global and appear in the ESET report: Trends for 2013: Astounding growth of mobile malware (PDF).
From 2011 to 2012, Android malware grew by a factor of 17X - ESETWhile that report came out a couple of months ago, my remarks to Frederic Paul after the RSA Conference were probably more influenced by what fellow ESET researcher, Cameron Camp, had been doing at RSA. Cameron performed a live demonstration of the complete compromise of an Android device using code and stratagems freely available on the Internet. Admittedly, Cameron's attack depended upon a temporary lapse in user vigilance while surfing the web, but as any seasoned security professional knows, such lapses are all too common. And the price can be heavy. This attack dumped the entire contents of the device to a remote server, silently and almost instantaneously. After the demo, Cameron pointed out the potentially sensitive nature of the information that might be stored on an Android smartphone: SMS messages, email, email attachments, photos, contacts, account credentials, and so on.
Play hacking and Android's security prospects
Clearly, Android is coming under heavy attack, like Windows did once it became popular. But what about the rest of my Windows analogy, that the security of the Android platform is likely to improve moving forward? We do see encouraging signs in the recent announcement of Samsung's SAFE initiative (SAmsung For Enterprise). Central to this initiative is Samsung's Knox. Steve Patterson of Network World said this of the secure enterprise enhancement to Samsung's Android devices: "not unique, but it is brilliant nevertheless." Over at TechRepublic, Jack Wallen has more details of the whole Security Enhanced (SE) Android architecture, which he describes like this
SE Android provides the mechanism to isolate applications and data into different domains to reduce tampering and the bypassing of application security. It also works to prevent any damage to sensitive data caused by malicious software.
So yes, there are security improvements on the way for Android devices, but it is not yet clear which devices will be protected, and at what cost. And will all consumer Android devices get this level of protection? Until they do, it is just not enough to rely on the common sense of Android users to avoid malware. Even the advice to "only get your apps from the Google Play store" is under threat from malfeasance. Consider the interesting Android security revelation from a recent article by Brian Krebs: Mobile Malcoders Pay to (Google) Play. Brian describes "a brisk market for hijacked or fraudulent developer accounts at Google Play that can be used to disguise malware as legitimate apps for sale."
In other words, Google still faces serious challenges trying to keep the bad guys out of the Android ecosystem. Despite this, there are plenty of Android users who act as though all apps in the Play store can be trusted all the way. No, you still have to think carefully before granting any permissions to any apps you put on your Android. Brian describes one Underweb buyer:
offering $100 for sellers willing to part with an active, verified Play account that is tied to a dedicated server. Unsurprisingly, this particular entrepreneur also sells an Android SMS malware package that targets customers of...[Brian then names a few of the 66 financial institutions targeted by this piece of malicious code].
With Windows 8, Microsoft has delivered the highest level of security yet for its popular operating system, about a decade after the company was sued by the FTC for making inflated claims about the security of one of its products. In the interim, many Windows users learned to be both suspicious and careful when it comes to software installs. Now go listen to the college students that Consumer Bob interviewed for the piece on NBC that I link to at the top of this article. Clearly, that learning, those elements of suspicion and carefulness, are not there yet for many Android users. That's why, when Brian says "a modicum of common sense and impulse control can keep most Android users out of trouble," I have to say, with all due respect, that "most" is not good enough for me.
Bottom line: I actually think there's a good chance Android security will improve a lot faster than Windows security, but until it does, and until security awareness among Android users rises considerably, I'm not going to stop recommending that people put anti-malware on their Android devices.