Win32/PSW.OnlineGames.OUM is a malware that aims to steal credentials for online games. It targets popular game titles such as World of Warcraft, Star Wars Galaxy, Lineage 2 or Guild Wars. Active since 2006. This malicious software is amongst the most detected threats by ESET, taking the 7th position of the Top 10 most detected threats between January and April 2011. In this blog, we will describe the update process used by this malware.
When executed on a system, Win32/PSW.OnlineGames.OUM creates a registry key named urlinfo which contains the version number of the threat.
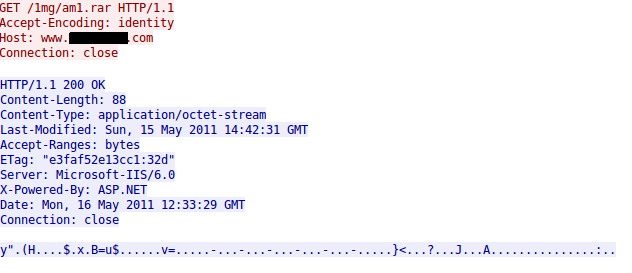
It will then look for an update by starting an instance of iexplore.exe and injecting code inside of it which will request a file from a URL that is hardcoded in its binary.
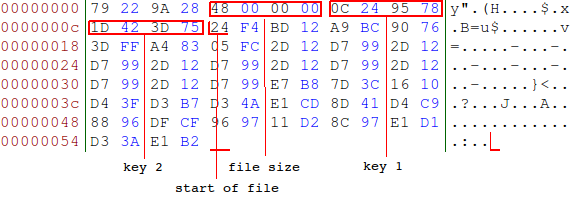
The downloaded binary blob contains an encrypted file and the keys to decrypt it.
Offsets:
0x04 : DWORD – size of the file
0x08 : DWORD – key #1
0x0C : DWORD – key #2
0x10 : The start of the encrypted file
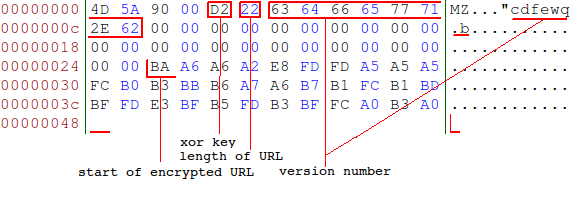
The file is decrypted by adding both keys to each DWORD of the encrypted blob. If bytes are remaining after the decryption process, they are appended to the end of the decrypted file. The following screenshot shows the decrypted file. The version number is visible, but the update URL is once again encrypted, this time with a simple XOR key.
Offsets:
0x04 : BYTE – XOR key
0x05 : BYTE – length of URL
0x06 : STRING - version number
0x26 : encrypted URL
If the update’s version is newer than the one already installed, Win32/PSW.OnlineGames.OUM then proceeds to download a second file from the decoded URL. This file is also encrypted with the same method and contains a new executable.
A new executable is usually made available every day. This leaves little time for anti-virus vendors to update their detection signatures. To this day, ESET has found more than 3000 different samples of this threat.
A cautious malware
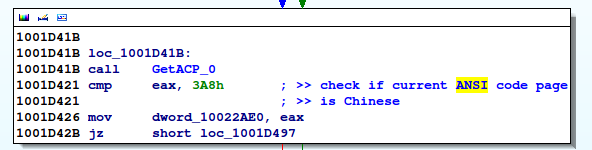
An interesting behavior we observed in Win32/PSW.OnlineGames.OUM is that it tries to avoid infecting computers located in China. It does so by checking the installation language and the keyboard layout.
The installation language is checked by comparing the value of the SYSTEMCurrentControlSetControlNlsLanguageInstallLanguage registry key to the constant 0804, which corresponds to Simplified Chinese.
As for the keyboard layout, it is checked by calling the GetACP function. The value 0x3A8 also corresponds to Simplified Chinese.
If any of those checks are positive, the process is aborted and the computer is not infected. This mechanism is very efficient; as seen in the figure below, very few infection cases have been detected in China when compared to the rest of the world (the color chart goes from blue to red, red denoting a high infection rate).
This concludes our presentation of the Win32/PSW.OnlineGames.OUM update process. In the second part of this series, we will examine the way this threat effectively steals game credentials.
Sebastien Duquette
Malware Researcher