Some cyber business risks only show up when you take a closer look. Supply chain blind spots are a perfect example. Behind these essential third-party connections, products and services can lurk unseen vulnerabilities that precipitate major cyber incidents – halting operations, triggering downstream chaos, and making headlines with their financial, reputational, and legal/compliance impacts.
As supply chains become increasingly digitized and complex, they provide cybercriminals a bigger “risk surface” to aim for. Organizations need to understand their supply chain dependencies in depth so they can map the risks and deploy effective resilience strategies to protect sensitive data and sustain business continuity. Yet according to the latest research from ESET and other sources, SMBs largely underestimate the potential risks they face from disruption caused by their supply chain, either from a malicious attack or operational outage.
What is a supply chain and what risks does it pose?
A supply chain is the total network of organizations, people, activities, information, and resources involved in moving a product or service from its origin to the final customer, encompassing sourcing, production, distribution, and delivery. Modern supply chains are often global and involve complex international logistics or connections.
Supply chain disruption gives rise to multiple, interrelated types of business risk. These include cybersecurity, operational, geopolitical, financial, reputational, compliance, environmental, and societal risks. In real-world scenarios the risks tend to blur. For example, data breaches linked to partners often have operational, financial, compliance, and/or reputational elements.
But perception does not always mirror reality when it comes to cybersecurity hazards. Perhaps reflecting the media’s recent focus on AI-powered exploits and geopolitical cyber conflict, ESET’s 2026 SMB Cyber Readiness Index released today found that 16% of Canadian and 17% of United States small businesses rate supply chain attacks among the threats they are most concerned about. Conversely, 34% Canadian and 32% United States SMBs identified AI-powered malware in their top threats.
This seems extremely low given the scale and frequency of supply chain incidents – and how broadly ‘supply chain’ really stretches. The 3CX compromise of 2023 – where bad actors trojanized a legitimate software update to the VOIP developer’s product, potentially exposing its 600,000 customers – showed how an incident affecting a single compromised vendor can cascade across industries. Notably, 3CX itself was the downstream victim of another supply chain attack, courtesy of a compromised Trading Technologies X_TRADER installer. It was the first-ever documented instance of one supply chain attack seeding another, and a reminder of how deep these chains can run.
More recently, the CDK and Change Healthcare ransomware attacks in 2024 and the Jaguar Land Rover (JLR) ransomware attack of August 2025 illustrate how an incident at a vendor that sits at a critical node propagates across an entire sector. JLR belongs on the list for a second reason: the intrusion reached the automaker through one of its IT service providers, placing it squarely in classic supply chain territory.
The faulty CrowdStrike update from July 2024 made the same point without an attacker involved, showing showed that supply chain risk isn’t only about malice. A botched update release travels the same rails as a malware-laden one, and dependence on a single vendor can turn one point of failure into a global disruption.
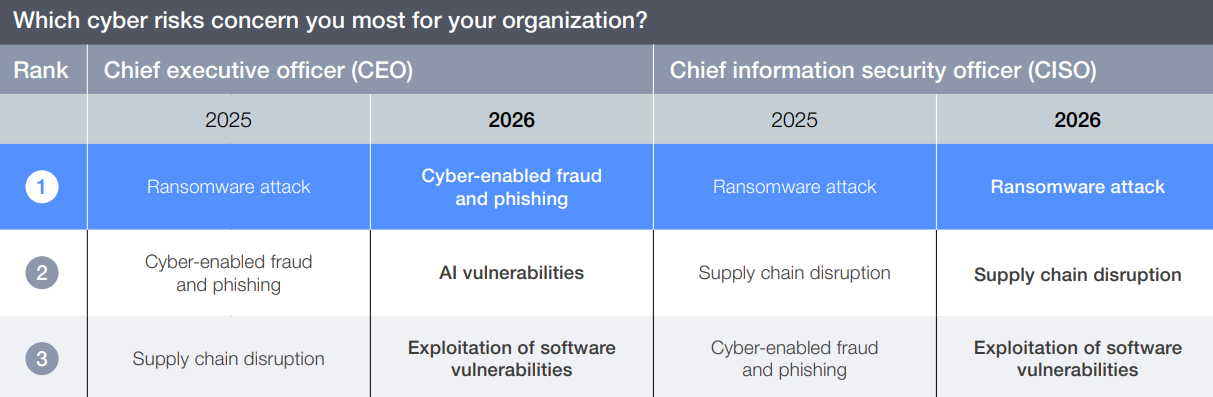
Echoing ESET’s findings, the World Economic Forum’s Global Cybersecurity Outlook 2026 asked business leaders across industries and regions to rank the cyber risks that concerned them most. CISOs rated supply chain disruption #2 for 2025 and #2 again for 2026, while CEOs rate supply chain disruption #3 for 2025. I find it surprising that supply chain disruption doesn’t continue to rank in a CEO’s top 3.
Overall, about 30% of data breaches involve a third party, a figure that doubled year-over-year, according to Verizon’s 2025 Data Breach Investigations Report (DBIR). The total economic cost of software supply chain attacks skyrocketed from $46 billion in 2023 to $60 billion in 2025, and is expected to reach $138 billion by 2031. Statistics like these should put cyber supply chain risk on every business leader’s short list of concerns.
What are the top cyber supply chain blind spots?
Supply chain cybersecurity risk concerns all possible ways that attackers could infiltrate a company’s networks or other IT infrastructure and steal its data by targeting vulnerabilities in the systems of third-party service providers, vendors, or partners. These attacks often exploit situations where communications are trusted by default, potentially compromising data, personal privacy, operational stability, or even national security.
Supply chain cyber vulnerabilities take various forms, such as:
- Compromising network-connected SMB suppliers with weaker security to create a backdoor into the target enterprise.
- Injecting malicious code into software components (e.g., open-source libraries) or updates, potentially compromising many users.
- Using phishing attacks and other social engineering ploys to steal privileged credentials or seed ransomware or other malware via a third-party such as an IT services company.
- Hacking or vulnerabilities in physical assets like chipsets or IoT devices at the source.
Some of the cyber supply chain blind spots that threaten many organizations include:
- Thinking your business is more resilient than it actually is (false sense of security) due to inadequate risk assessment.
- Geopolitically motivated incidents (see below), where “collateral damage” can harm numerous organizations not directly related to a conflict.
- Cyber vulnerabilities several levels deep in the supply chain where the end customer has no visibility (so-called fourth-party, nth-party, or indirect vendor risk).
- “Reverse” supply chain disruptions impacting a company’s customers.
- Assuming new and unassessed vulnerabilities along with new supply chain partners that were onboarded quickly due to geopolitical events, natural disasters, or other chaotic scenarios.
- Trusting communications with partners instead of leveraging zero trust principles to validate all connections.
- “Monoculture” issues, such as wide-scale reliance among MSSPs or cyber insurance providers on one or a few popular cybersecurity solutions that, if compromised, would wreak instant havoc on a large scale.
The sheer complexity of many modern supply chains makes identifying every single risk untenable. The question then becomes, where do you draw the line? How deep and detailed is your vendor risk assessment? And what level of supply chain cyber risk are you willing to accept as beyond your control?
What have been the impacts from major supply chain attacks?
Some of the most damaging incidents in recent memory hit organizations that sit at critical nodes in supply chains, and the resulting disruptions cascaded far beyond the original target.
A prime example of a cyberattack with an enormous blast radius is the JLR ransomware attack from August 2025. Attackers reached the automaker through an outsourced IT service provider, then disrupted production lines and IT services for over five weeks. The result was a global manufacturing shutdown that caused a 25% drop in vehicle production across the entire sector in the UK in September 2025. Parts demand crumpled overnight, forcing JLR’s suppliers and related businesses to lay off hundreds of workers and driving the UK government to issue a £1.5 billion emergency loan guarantee to forestall a national economic and workforce crisis. Deemed the costliest cyberattack in UK history, it resulted in over £1.9 billion in total economic damage.
The Marks & Spencer (M&S) attack of April 2025 followed a similar pattern. The hackers successfully employed social engineering against an outsourced IT service provider, impersonating employees and convincing help desk staff to reset critical system credentials. Contact details, birth dates, and order histories from millions of customers were apparently exfiltrated, and the company’s online and app-based order processing were down for weeks. The lengthy outage cost on the order of £300 million and inflicted lasting reputational damage.
Compromising commonly used open-source software libraries with malicious code is a similar and increasingly popular attack vector, with open-source malware proliferating 188% from 2024 to 2025.
In a stark illustration of geopolitical blind spots within the software supply chain, a malicious backdoor placed into a legitimate update to the popular M.E.Doc accounting software in 2017 caused widespread distribution. Intended to target the Ukrainian economy, the attack spread NotPetya wiper malware to organizations worldwide, sowing destruction estimated to cost $10 billion. The attack was later attributed to a Russia-aligned source.
Even hardware components like chips and circuit boards can potentially be exploited or weaponized, creating blind spots that are extremely difficult to detect or defend against. An ongoing example is the Kr00k firmware supply chain vulnerability (CVE-2019-15126) discovered by ESET in 2019. Attackers can force affected devices, including millions of smartphones, laptops, and IoT devices, to encrypt Wi-Fi transmissions with an all-zero key that allows for easy decryption. It’s likely that many affected devices still do not have firmware patches installed due to the mass scale of use.
And as an extreme example, the “Operation Grim Beeper” supply chain attack of September 2024 saw pagers and walkie-talkies used by Hezbollah members in Lebanon and Syria explode as part of an Israeli intelligence operation. Over 30 people were killed and 3,000 injured after equipment purchased by Hezbollah was systematically intercepted and weaponized for years. Talk about a supply chain blind spot…
What are key considerations around geopolitical supply chain risk?
With Iran launching drone strikes against Amazon Web Services (AWS) data centers in Bahrain and the UAE, geopolitical supply chain cyber risk is front-page news. Where kinetic and cyber warfare overlap, nation state actors and their proxies can exploit critical supply chain dependencies to perpetrate wide-scale economic sabotage for strategic ends that may include monetary theft. Collateral damage is part of the plan.
Some questions that organizations can ask to potentially reduce geopolitical supply chain risk include:
- Carefully audit all third-party hosting relationships, vendor access to your network, etc. Is your data moving through data centers in volatile regions – either directly or through service provider activities? Cloud service disruptions can propagate unpredictably through the supply chain.
- Are you reliant on hardware or software that cyber combatants are currently targeting with specialized attacks, such as Israeli-made OT hardware?
- Check whether your managed security solution provider(s) and other critical vendors have reviewed their own geopolitical cyber risk exposure. If a third party manages your incident detection and response (MDR) capability, for example, their solution becomes part of your attack surface.
How can organizations build supply chain cyber-resilience?
General strategies for mitigating supply chain cyber risk include rigorously vetting suppliers’ cybersecurity postures, adopting emerging technology to enhance monitoring, leveraging zero trust principles to reduce attack impacts, and creating and testing incident response and business continuity plans to build resilience and better manage supply chain related incidents. Your entire supplier web needs to be part of the risk assessment.
To build and operationalize supply chain cyber resilience, I recommend a sequence of activities that collectively build resilience over a one-year period.
First 3 months
- Nominate business and IT owners for supply chain risk.
- Identify all your third-party IT and business supply chain vendors and prioritize them by 1) Access to sensitive data, and 2) Criticality to the business.
- Create a policy that defines your minimum acceptable cybersecurity posture or controls for vendors.
- Check vendor compliance with your cyber requirements and replace them as needed.
First 6 months
- Continue to monitor vendor compliance with your cyber requirements.
- Describe key hardware and software supply chain risks (e.g., open-source dependencies) in business terms.
- Incorporate your cyber requirements into procurement activities and contract negotiations. Negotiate the right to monitor and audit critical vendors.
- Conduct a tabletop incident response exercise that includes strategic vendors.
First 12 months
- Implement lessons learned from your tabletop exercise.
- Audit vendors against contractual cyber requirements (e.g., average time to patch). Investigate supplier cyber incidents where relevant.
- Build redundancy and fail-safes into IT systems wherever possible, while avoiding solution “monoculture” issues.
- Review and update your cyber requirements policy.
- Monitor and respond to global cyber regulatory/compliance changes that impact your business.
Resilience is imperative
In a world of escalating threats and risky interdependencies, supply chain cyber resilience is a competitive differentiator at the survival level. Cybercriminals are keen to identify and target an organization’s third-party linkages either upstream or downstream. It’s possible that a chain of disrupted partners could face collective extortion pressure – effectively a “crowdfunded” ransomware scenario.
As a foundational resilience building block, firms must comprehensively map their critical third-party dependencies and vulnerabilities across digital and non-digital systems, including those that may not be obvious. Some ways to look beyond typical operational supply chain risk assessment include:
- AI-assisted continuous supply chain monitoring
- Automated supply chain dependency mapping
- Zero-trust supply chain architecture and connections
- Application of threat intelligence to supply chain configurations
- Extending resilience planning/considerations beyond internal systems to include the broader supply chain ecosystem
- Possible input and assistance from your cyber liability insurer, which may have data-driven insights into vendors’ supply chain cyber performance







