Golf clubs and cybercrime couldn’t really sound further apart, but when it comes to cybersecurity, businesses of all sizes are targets and their owners must never assume anything is completely watertight. Golf is, however, more associated with business, so when I was recently asked to investigate and test the cybersecurity of an independent UK golf club, I thought it sounded like an interesting experiment.
Furthermore, the owner of the club claimed that I would “struggle” to hack them, as they have someone who is “on top of our security”. Saying this just made me extra determined and more up for the challenge!
I’ve not played golf in a few years, but back in my university days I spent a good handful of occasions hacking up the course with my 7-iron. However, more recently, I have turned my hand to a different kind of hacking, which is far more fun and much less ego-bruising.
With 14 years’ worth of experience in the cybercrime and digital forensics unit in the police, I now review and analyze potential cyberthreats facing businesses. Being able to understand criminal hackers often helps with revealing insights into their mindset, which can then lead to better protection for organizations.
At this point, I need to add a little disclaimer. Before I embarked on my escapade at this beautiful course in the stunning English countryside, I was granted full access and permission by the owner of the club to go wherever I wanted and to do whatever I desired – within reason, of course!
As with any good heist, research is vital. Although I am familiar with the surroundings, lingo and attire of a quality golf club, I needed to learn everything I could about the staff and this specific club in question; and this is where Google is your best friend. Armed with my online findings and a couple of quality techniques in my back pocket, I was pretty confident I could have some fun with my target golf establishment.
I decided to pose as a TV assistant producer, enquiring to do a reconnaissance visit for a new commercial and requesting to take some photos to report back to my producer. I phoned the club a week in advance and gave them my pre-context story. The business development manager answered the call and (naturally) loved the idea, excitedly inviting me to visit the club the following week.
A field day for hackers
I arrived at the course one sunny morning and headed straight to reception shortly after 9am, equipped with my laptop, USB drive, DSLR camera and a trusty high-visibility jacket. Once I had met with the business development manager who I’d previously spoken to, I walked off for an hour with my camera and took some photos of the course.
On my return, I showed him the photos and asked if I could use their private Wi-Fi, mentioning it would be safer(!), and requested the password, which was happily given to me. I then declared that I’d forgotten some paperwork which needed to be signed, so I asked him if I could pop my USB drive into his computer to print off a release form. He obliged and even said, “I wouldn’t normally let someone I don’t know do this but as it’s for TV, I’ll make an exception.”
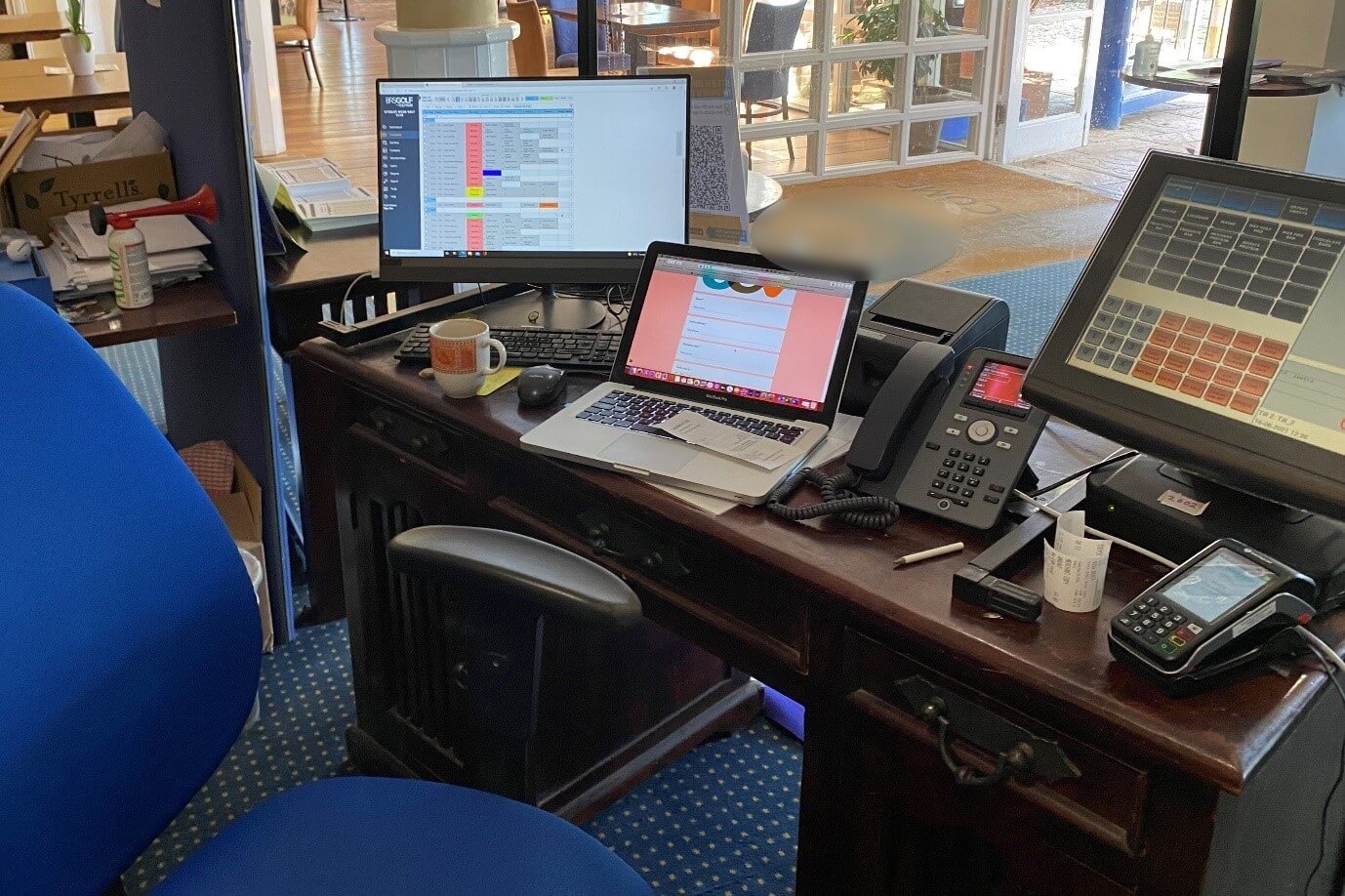
It was then that I witnessed the true horror show – something which I had not expected to see ever again. They were still using Windows XP!! Support for this operating system ceased in 2014 and it is highly dangerous when connected to the internet, so seeing this in the wild made me shiver with astonishment, even fright. To make matters worse, XP was running on the machine in the shop with their point-of-sale software on! With all the financial and sensitive data being run through this device, it would make for a very dangerous outcome if it were targeted.
Once I had pretended that the document I needed to print was missing from my USB, I offered to send a fake pre-release form via Google Forms in order to obtain some additional personal information from him, along with one of his passwords. He clicked on this link immediately and filled it out. In fact, he then took a call and left me with full access to two further machines with no one looking.
With access to the Wi-Fi password, USB drives and even unsupervised machines I could have completed any exploit I could dream up. From installing a remote access trojan or keyloggers onto the machines, to placing other malware, such as ransomware on the network to demand payment to decrypt the data, this was a hacker’s delight!
Leaving one’s workstation unsupervised and unlocked is a danger in any workplace, but particularly in a position where the public can simply walk in and coupled up with the other security faux pas, makes me realize that some businesses are still so far behind in their security.
Of course, I didn’t actually exploit the network at this golf club, but the lessons learned were vital and the seriousness is worrying. The amount of personal, sensitive, and financial data held on the network that I had full access to could be extremely costly. If compromised, the GDPR fines for leaking this kind of personal information could have been catastrophic. Joining a golf club comes with handing over a lot of information, so if a club were to lose this data there would be huge consequences and more than one victim.
Play the long game
The simplicity of hacking somewhere can be eye-openingly impressive. A quality backstory, a touch of charm and a spot of luck will get you into most areas that could be exploited. If the cybersecurity basics have been bypassed, however, the nefarious task in hand can be that much easier. A high-visibility jacket just helps to seal the deal.
Exploiting the weak or vulnerable is exactly what threat actors are good at, so we all need to up our games away from the golf course and start focusing on where those weaknesses are in our businesses.
On report to the golf club’s owner, he was somewhat shocked, yet equally unsurprised. He said himself that he never thought anyone would ever hack his business and wrongly assumed criminal hackers sit in hoodies and go after the big companies. The truth is, however, that every business is a potential target and if they remain so easily penetrable, they will remain rich pickings for hackers.