Although it’s been some weeks since the height of the income tax season in many countries around the globe, the year 2020 has been looking less than normal even for cybercriminal activity. For several months, various threat actors have been attempting to impersonate governmental organizations, such as the Agencia Tributaria – the official tax agency of Spain. Here, we take a look at how the operators of Grandoreiro, an infamous Latin American banking trojan, have been using emails posing as the Agencia Tributaria in order to ensnare new victims.
Emails purportedly sent by the Agencia Tributaria
On August 11th, 2020, many Spaniards were receiving emails claiming to be from the Agencia Tributaria. These messages were using false sender information like “Servicio de Administración Tributaria” and the email address contato@acessofinanceiro[.]com in order to trick the recipients into believing they had received an official communication from the tax agency.
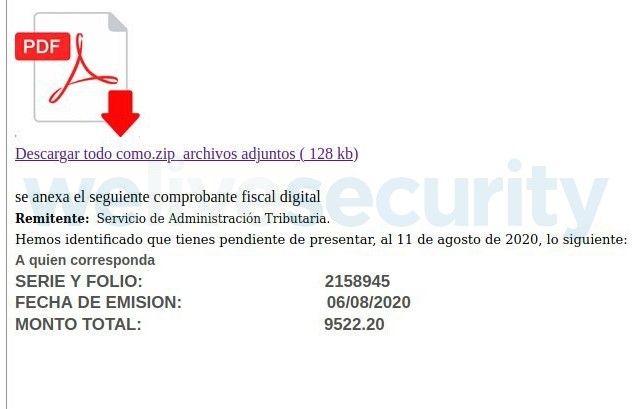
In the body of the message, the recipient is directed to download a ZIP archive that supposedly contains a digital tax receipt. It also advises that there is a document remaining to be submitted to the Agencia Tributaria along with a fee to pay. Although the message offers no guarantee of being an official communication, it is likely that some recipients have been tricked into downloading the linked ZIP file via the provided link.
The link redirects to a domain that was registered on the same day, August 11. However, looking at the information provided by whois – a service that provides identifying information about domain name registrants – the registrant's country is listed as Brazil, which could perhaps indicate the whereabouts of the operators of this campaign.

ESET also observed a few campaigns of Mekotio, another Latin American banking trojan, being distributed the same way only a few days later.
Download and execute
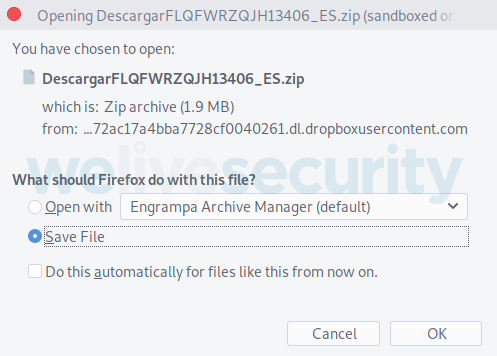
The infection chain in this campaign is typical for Latin American banking trojans. First, the file to be downloaded has been placed by the malicious operators either on a compromised domain, or in a cloud storage service like Dropbox. In such cases, the link in the email spam directs the recipient to a Dropbox link from where the ZIP file can be either opened or saved.
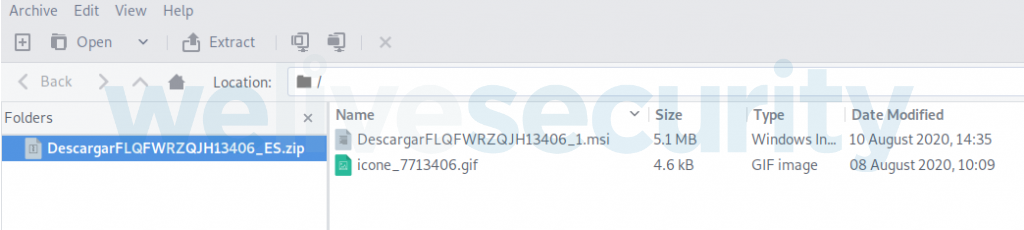
This ZIP payload contains an MSI file and a GIF image. Homing in on the properties of the MSI file reveals that it was compiled the day before, August 10. It should also be noted that the ZIP filename has the country code “ES” at the end. ESET researchers also detected other files in Dropbox with very similar sizes and dates of compilation, but with different country codes – possibly indicating that this campaign is targeting victims in various countries at the same time.
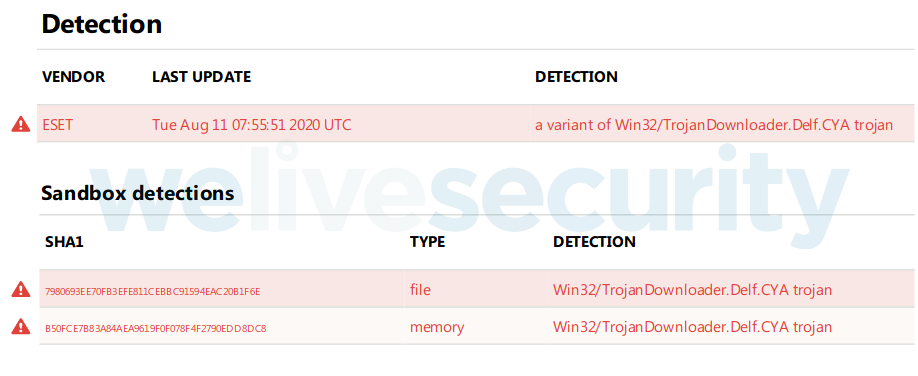
ESET security solutions detect this MSI file as a variant of Win32/TrojanDownloader.Delf.CYA, a type of malicious downloader responsible for introducing other malware into your system, especially from the Latin American banking trojan families, such as Grandoreiro, Casbaneiro, Mekotio and Mispadu.
In this case, we see a new variant of the Grandoreiro banking trojan that has been particularly active in Spain in the last few weeks.
Conclusion
Impersonating Spain’s Agencia Tributaria or other similar agencies is an old trick in the attackers’ book that has been used for a long time, especially during tax season. However, even when high season for income taxes has already concluded, this year has seen this technique being used by Latin American banking trojans and other threats specialized at stealing data.
For this reason, it is important to remain alert and to avoid clicking on a link in an email, unless you're absolutely certain about its provenance by verifying with the sender, and to consider the possibility that an email might be attempting to pose as a governmental agency. Using a robust security solution, capable of detecting and neutralizing these threats, goes a long way to quickly and easily increase your protection.
Note: A version of this article in Spanish first appeared on this blog of Ontinet.com-ESET España and was translated by ESET security writer Rene Holt.