UPDATE (March 8): Google said late on Thursday that attackers targeted the flaw in Chrome together with a “serious vulnerability” in Microsoft Windows. The latter zero-day, affecting the Windows win32k.sys kernel driver, can be “used to elevate privileges or combined with another browser vulnerability to evade security sandboxes”.
That said, Google strongly believes that the vulnerability in Windows is only exploitable against Windows 7 32-bit systems, and advised users to consider upgrading to Windows 10, where recent mitigations work against the threat. Google reported the flaw to Microsoft, which is now working on a patch for Windows 7 systems.
Google has revealed that the update for Google Chrome, rolled out late last week, addressed a security hole that attackers were already exploiting in the wild.
“Google is aware of reports that an exploit for CVE-2019-5786 exists in the wild,” the company noted in an update on Tuesday after initially releasing the advisory last Friday. Also on Tuesday, a tweet by leading Chrome security engineer Justin Schuh added urgency to the issue: “[Like], seriously, update your Chrome installs... like right this minute”.
The vulnerability that affects the browser in Windows, Mac, and Linux was reported by Clement Lecigne of Google's Threat Analysis Group on February 27.
The security hole is a “use-after-free” memory corruption bug in the browser’s FileReader API, a browser component intended to enable web apps to read locally stored files. That said, exploitation of the vulnerability can result in more damage than the API’s name might imply. As revealed by a note by the Center for Internet Security (CIS), attackers may ultimately be able to execute arbitrary code remotely on the targeted system:
“Depending on the privileges associated with this application, an attacker could then install programs; view, change, or delete data; or create new accounts with full user rights,” reads the note. The zero-day can be triggered when a user is lured to a specially-crafted web page.
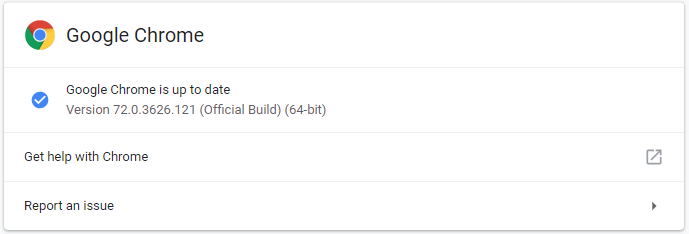
In light of all that, users are advised to update to Chrome version 72.0.3626.121 if they haven’t done so already. Arguably the easiest way to check if an update is pending is to type chrome://settings/help into the browser’s address bar and, if your browser is indeed out of date, follow the prompts.