Two weeks ago, reports that a vast compilation of stolen access credentials was being widely circulated, not only in the internet’s dark recesses, made the headlines. Before long, additional reports began to pour in that this trove of data, dubbed Collection #1, was far from the only massive and readily available aggregation of stolen logins.
Security journalist Brian Krebs, for one, wrote that Collection #1, which comprises 773 million login names and associated passwords, was just a portion of a far larger stash of stolen or leaked credentials that was circulating on hacking forums and via torrents. Besides, by some accounts at least a portion of the latter caches contains more recent data, thus potentially posing greater risks for users. Enter Collections #2 through #5, so nicknamed by their creator(s).
Research by Germany’s Hasso Plattner Institute (HPI) has shed some more light on the data sets. HPI found that the number of purloined login credentials that have been cobbled together into the five tranches totals 2.2 billion, reads the institute’s press release (in German).
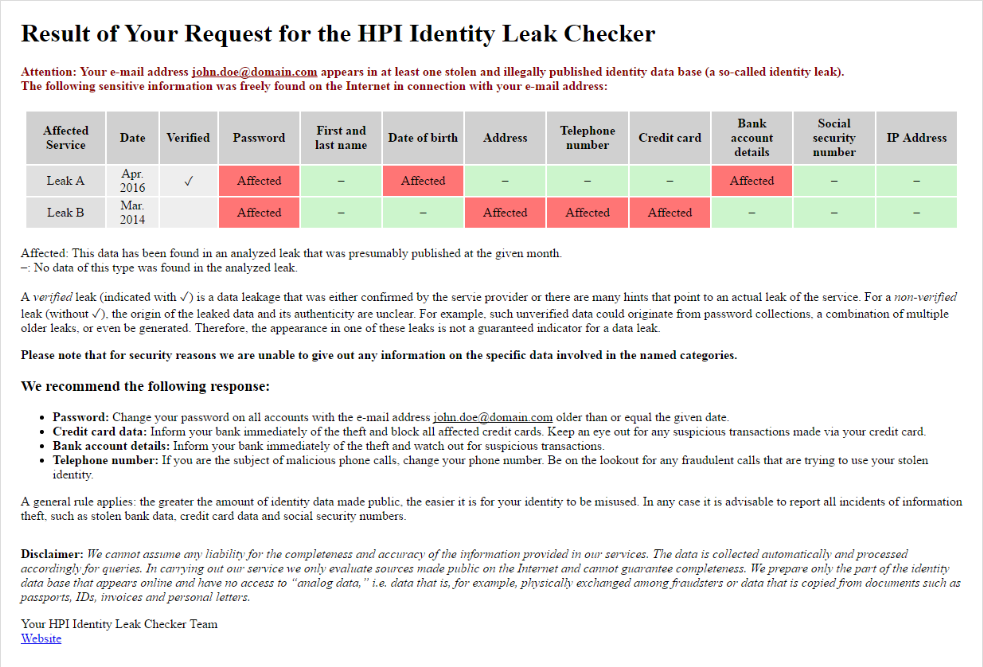
Importantly, the institute operates a service that is similar to Troy Hunt’s Have I Been Pwned (HIBP) site. Unlike HIBP (as of the day of writing, anyway), the Identity Leak Checker includes data from all five caches in their entirety, and then some – 8.16 billion data records.
You can use the tool to check if any of your email accounts, or an online account associated with your email account(s), may have been impacted by a known leak. In addition to login names and passwords, the tool can also show some other sensitive information of yours that may have also been exposed.
Databases of stolen login data can have far-reaching implications particularly because of the rampant practice of many netizens to reuse their passwords across multiple services. Attackers can exploit this with an automated technique known as ‘credential stuffing’ that can give them access to other and possibly higher-value online accounts where the victim uses the same access credentials.
Beyond using a unique and strong password for each account, it’s also worth setting up two-factor authentication (2FA) wherever possible. That extra factor is a simple measure that is very likely to help thwart account-takeover attempts.