A 21-year-old man from Kentucky, US, has been sentenced to 30 months in jail after pleading guilty to developing and selling a popular remote access Trojan (RAT) known as LuminosityLink, a statement by the US Justice Department reveals.
In his plea deal, Colton Grubbs admitted to authoring, marketing and selling the malware, knowing full well that some customers would use it to remotely access and control their victims’ computers without the victims’ knowledge or consent. The authorities charged Grubbs with conspiracy to unlawfully access computers in furtherance of a criminal act, conspiracy to commit money laundering, and the illegal removal of property to prevent its lawful seizure.
The actions that intruders could carry out on the victims’ computers by dint of the full-featured RAT ran the gamut – viewing and downloading files, logging keyboard presses, pilfering login credentials, mining virtual currencies, spying on the victims via their microphones and cameras, and participating in distributed denial-of-service (DDoS) attacks, to name just a few malicious actions.
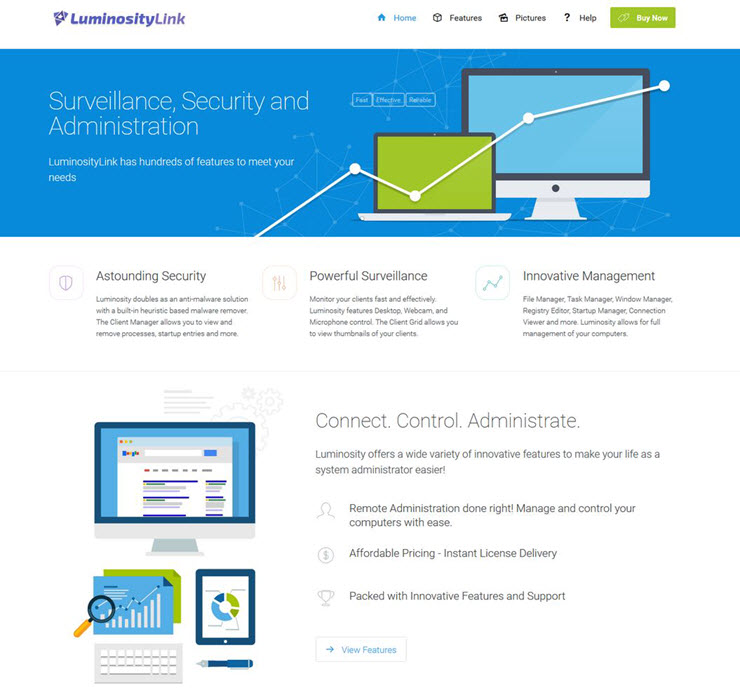
According to the prosecutors, over 6,000 people worldwide purchased the malicious software, which Grubbs sold for an average of $40 a pop. Using the “KFC Watermelon” username, Grubbs peddled LuminosityLink on the public internet forum HackForums.net, as well as selling on a dedicated website. Through posts and group chats, he also advised customers on how to break into and control computers using his malicious software.
Downfall
As we reported in February of this year, the international operation to crack down on a criminal network that distributed and used LuminosityLink took place in September 2017. Citing “operational reasons”, the authorities didn’t disclose the information about the clampdown until February of this year.
There was no word on the mastermind’s arrest back then. Per Bleeping Computer, however, it appears that Grubbs may have actually been nabbed as far back as July 2017, although there seem to be no official reports to confirm it.
In another interesting development, the plea deal (available via Krebsonsecurity.com) indicates that Grubbs somehow learned that the FBI would raid his home, which prompted him in July 2017 to attempt to conceal incriminating evidence from authorities. He hid the debit card with his Bitcoin account and the mobile phone containing his Bitcoin information, hid his laptop in his roommate’s car, removed the hard drives from his PC, and transferred the 114 Bitcoin from his LuminosityLink bitcoin account into six new Bitcoin addresses. Ultimately, this didn’t seem to have helped.
At first, Grubbs denied any wrongdoing, alleging that his creation was a legitimate utility for the remote administration of computers. He reversed course and entered into the plea agreement in July of this year.