Users of the popular cryptocurrency exchange Poloniex have been the target of two credential-stealing apps, discovered on Google Play disguised as legitimate Poloniex mobile apps. Apart from harvesting Poloniex login credentials, the fake apps also try to trick victims into making their Gmail accounts accessible to the attackers.
Poloniex is one of the world’s leading cryptocurrency exchanges with more than 100 cryptocurrencies in which to buy and trade. That alone makes it an attractive target for fraudsters of all kinds, but in this case, it was its lack of an official mobile app that the criminals used to their advantage.
With all the hype around cryptocurrencies, cybercriminals are trying to grab whatever new opportunity they can – be it hijacking users’ computing power to mine cryptocurrencies via browsers or by compromising unpatched machines, or various scam schemes utilizing phishing websites and fake apps.
The malicious apps
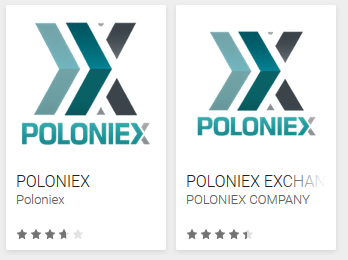
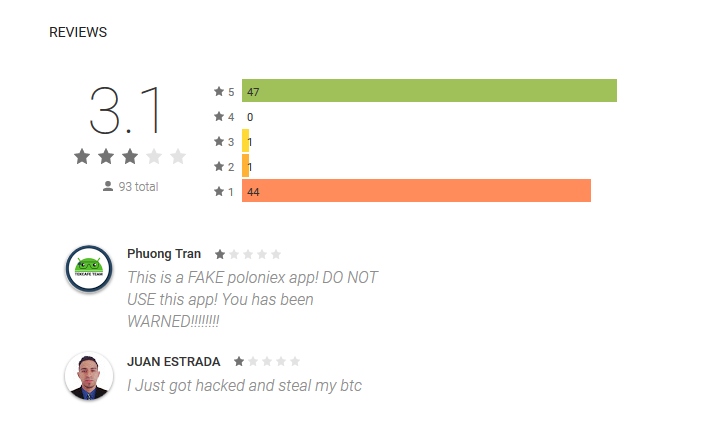
The first of the malicious apps sneaked into Google Play using the name “POLONIEX”, published under the developer name “Poloniex”. Between August 28, 2017 and September 19, 2017, the app was installed by up to 5000 users, even despite mixed ratings and bad reviews.
The second app, “POLONIEX EXCHANGE” with the developer name “POLONIEX COMPANY”, appeared on Google Play on October 15, 2017 and reached up to 500 installs before being removed from the store upon ESET’s notification to Google Play.
Apart from notifying Google, we also informed Poloniex about the malicious imposters.
How do they operate?
To successfully take over a Poloniex account using one of the malicious apps, the attackers first need to obtain credentials for the account. Afterwards, they need to gain access to the email account associated with the compromised Poloniex account to control notifications about unauthorized logins and transactions. Finally, the attackers need to make their app appear functional so as to lower any suspicion they might have raised in the process.
Both apps use the same method to achieve this.
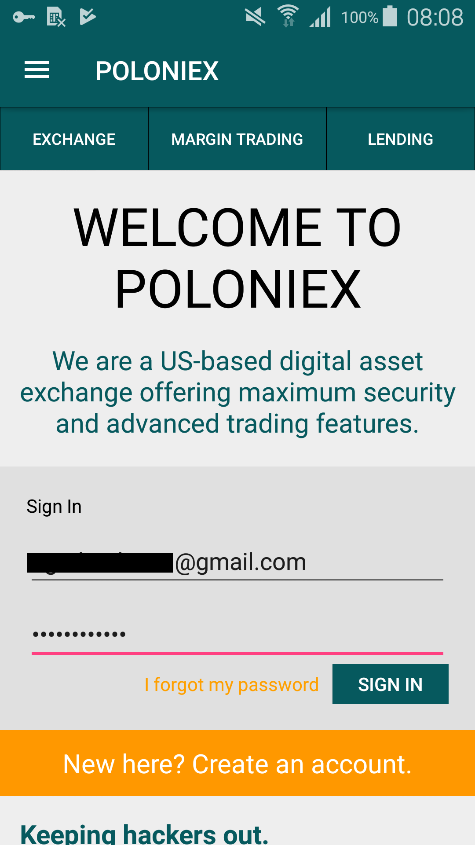
The credential stealing takes place right after the user launches one of the apps. The malicious app displays a bogus screen requesting Poloniex login credentials (Figure 3). If the user enters the credentials and clicks on “sign in”, the credentials are sent to the attackers.
In case the users don’t have 2-factor authentication (2FA) enabled on their Poloniex accounts, attackers now have access to those accounts. This means the attackers can carry out transactions on the users' behalf, change their settings, or even lock them out of their accounts by changing their passwords.
If the users do use 2FA, their accounts are safe from this attack. This is because Poloniex offers its users 2FA via Google Authenticator, which generates random login codes that are sent to users via text, voice call, or the Google Authenticator app – none of which can be accessed by the attackers.
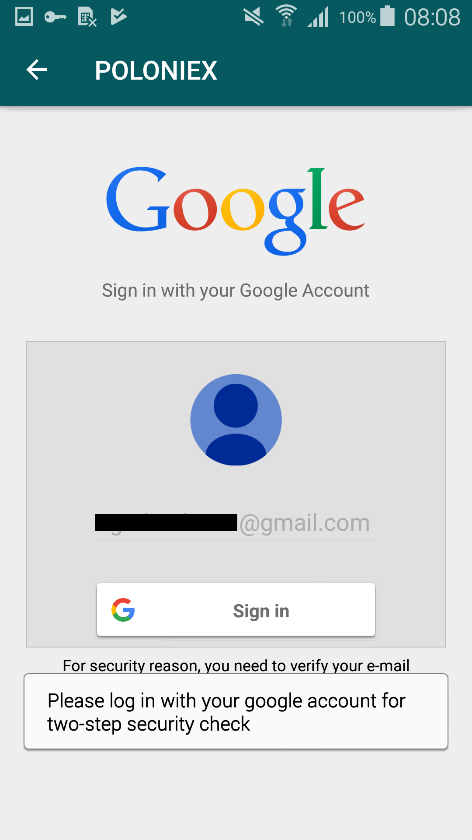
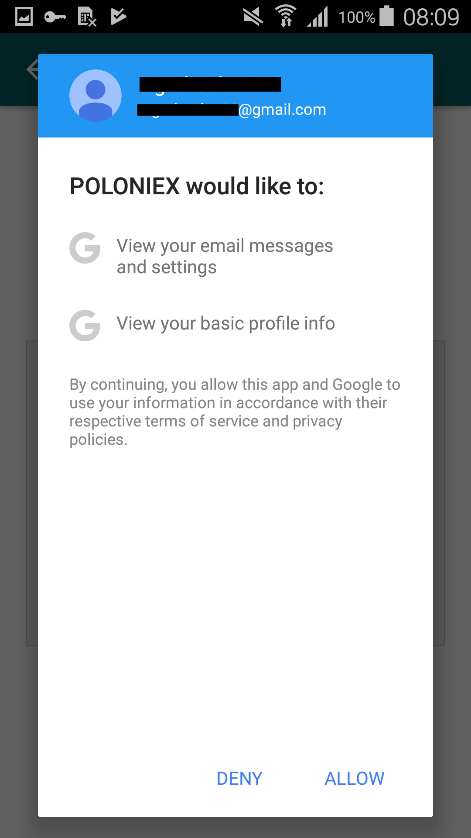
If the crooks are successful, they start working on accessing the user’s Gmail account. The user sees a prompt, seemingly on behalf of Google, requesting Google account login “for two-step security check” (Figure 4). After the user clicks on “Sign in”, the malicious app asks for permission to view the user’s email messages and settings, and basic profile info (Figure 5). If the user grants the permissions, the app gains access to the inbox.
With access to the user’s Poloniex account as well as to the associated Gmail account, the attackers can make transactions using the compromised account and erase any notifications about unauthorized login and transactions from the victim’s inbox.
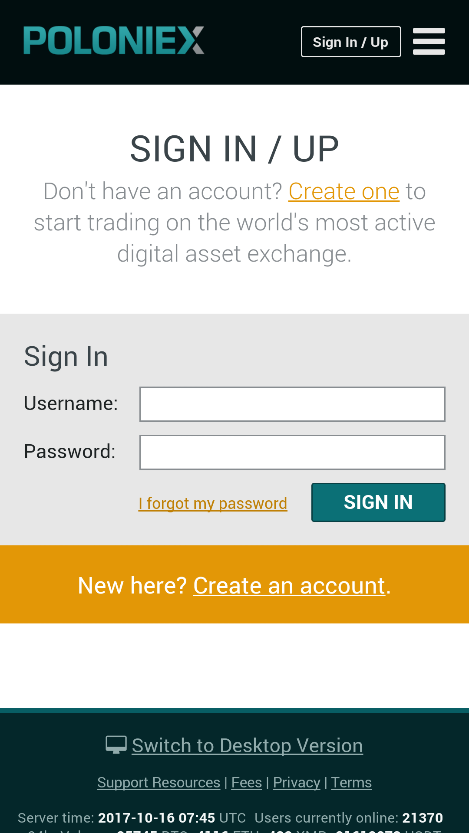
Finally, in order to appear functional, the malicious app directs the user to the mobile version of the legitimate Poloniex website, which requests the user to sign in (Figure 6). After logging in, the user can access and use the legitimate Poloniex website. From then on, the app will only open the legitimate website each time it’s launched.
How to protect yourself?
If you’re a Poloniex user and have installed any of these malicious apps on your device, start by uninstalling them. Make sure to change both your Poloniex and Gmail passwords and consider enabling 2-factor-authentication authentication for both services.
Here’s what you can do to avoid falling victim to fraudsters in the future:
- Make sure the service you’re using really offers a mobile app - if that’s the case, the app should be linked on the service’s official website
- Pay attention to app ratings and reviews
- Be cautious of third party apps triggering alerts and windows appearing to be connected to Google – misusing users’ trust towards Google is a popular trick among cybercriminals
- Use 2FA for an additional (and often crucial) layer of security
- Use a reliable mobile security solution; ESET products detect these credential stealers as Android/FakeApp.GV
IoCs |
|
|---|---|
| Package Name | Hash |
| com.poloniex.exchange | 89BE9AF09BB3B2CAD9EAF88FE0EF175E5F150044 |
| com.poloniexap.poloniex | 427CBAFD6E28C50708E26A481A9C8665C3315BCD |