Websites are being told that they have until September 30th to pay extortionists $720 worth of Bitcoin, or else suffer a distributed denial-of-service (DDoS) attack.
Thousands of companies around the world are thought to have received emails in the last few days claiming to come from "Phantom Squad" with the subject line "DDoS Warning".
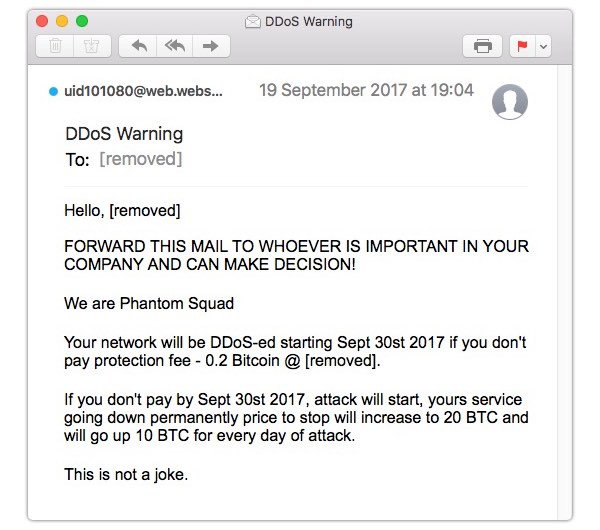
The emails reads as follows:
FORWARD THIS MAIL TO WHOEVER IS IMPORTANT IN YOUR COMPANY AND CAN MAKE DECISION!
We are Phantom Squad
Your network will be DDoS-ed starting Sept 30st 2017 if you don't pay protection fee - 0.2 Bitcoin @ [removed].
If you don't pay by Sept 30st 2017, attack will start, yours service going down permanently price to stop will increase to 20 BTC and will go up 10 BTC for every day of attack.
This is not a joke.
Of course, the name "Phantom Squad" is one that is familiar to those tracking denial-of-service attacks. A group called Phantom Squad has previously associated with DDoS attacks launched against the likes of the PlayStation Network, Xbox Live, Steam, and other video gaming services.
The 0.2 Bitcoin demanded by the threatening emails is equivalent to approximately US $720. In the grand scheme of things that's not a large amount of money for internet criminals to demand when threatening to launch a DDoS attack which could blast a website off the internet. It's certainly peanuts compared to the kind of financial damage that could be done to a major online gaming site if it was knocked offline.
From the looks of things, the emails are being sent to all manner of organisations - in what appears to be more of a scattergun approach, rather than targeting specific victims. Is it possible that whoever is responsible for the current spate of emails is asking for a relatively small amount of money in the hope that smaller companies will be panicked into paying up, even if there is no evidence that the extortionists will follow through with their threats?
After all, there's no evidence that the emails really do come from the same "Phantom Squad" that launched high profile attacks against the likes of Xbox Live in 2015, and Steam the following year. It's worth considering that whoever has sent the extortion emails may be deliberately using the notorious name of "Phantom Squad" to make the threat appear more significant.
Normally when a website is threatened with a sustained DDoS attack, the criminals will prove that the threat is real by causing a brief outage on the site in advance, or cause an unexplainable spike in traffic. There is clearly more reason to be alarmed if you have found any evidence that someone has already being deliberately stressing your web servers.
If you do fear that your site might be a potential victim of a DDoS attack it can be worth reaching out to a DDoS mitigation provider and your service providers to see how they might be able to help. At the very least your web host is going to appreciate getting early warning that there might be an upcoming attack on the way.
But the very nature of the spammed out emails, and the sheer number of messages sent to a wide variety of companies demanding such a small amount of money, suggest that this may very well be an example of someone trying to scare your company into paying up rather than presenting a serious threat. In short, the emails might be fake.
My recommendation, obviously, is not to pay ransoms to blackmailers. Secure email service ProtonMail paid a ransom to DDoS blackmailers in 2015, only to later regret their decision. And resist any temptation to try to make contact with those who are trying to extort money from you - it may only encourage them to focus their attention on you in future.