The massive campaign that spread the WannaCryptor (aka WannaCry) ransomware wasn’t the only large-scale infection misusing the EternalBlue and DoublePulsar exploits, leaked by Shadow Brokers.
The same mechanism has been misused by black hats as early as the end of April, when they opted for off-the-shelf Monero cryptocurrency mining software instead of the encrypting payload.
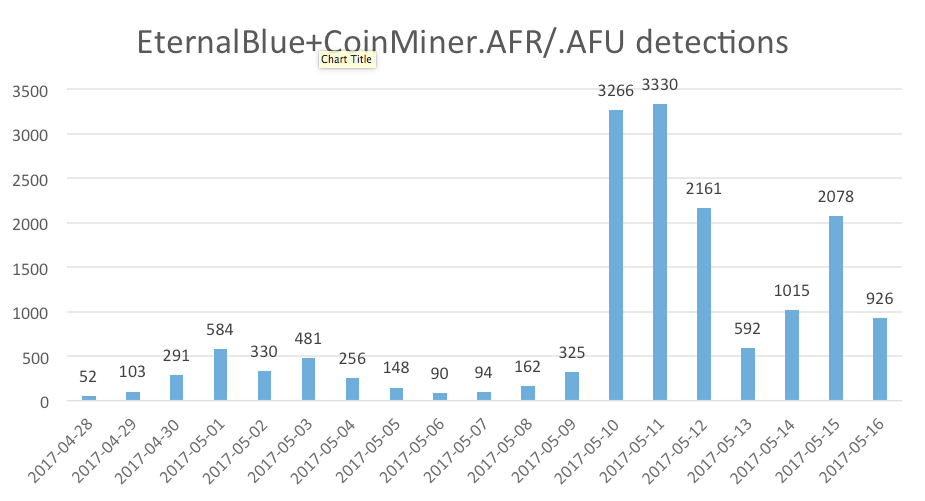
This campaign, detected as Win32/CoinMiner.AFR and Win32/CoinMiner.AFU, started only a few days after the NSA tools leaked online. ESET had network detections for the vulnerability deployed on April 25th – only three days before the first attack attempts by these miners.
The biggest uptick has been recorded only hours before the worldwide ransomware outbreak, on May 10th. On this day, mining malware detections increased from hundreds to thousands of detections per day. We have seen such attempts in as many as 118 countries, with Russia, Taiwan and Ukraine topping the list.
However, the mining software consumed system resources so intensively that in some cases it rendered the infected machines unresponsive.
The miner attacks also blocked port 445, used by the EternalBlue exploit to get into the machine, basically closing the door for any future infection using the same vector – including WannaCryptor. If the miners hadn’t taken this precaution, the number of WannaCryptor infections could have been even greater than reported.
So how bad was the WannaCryptor attack?
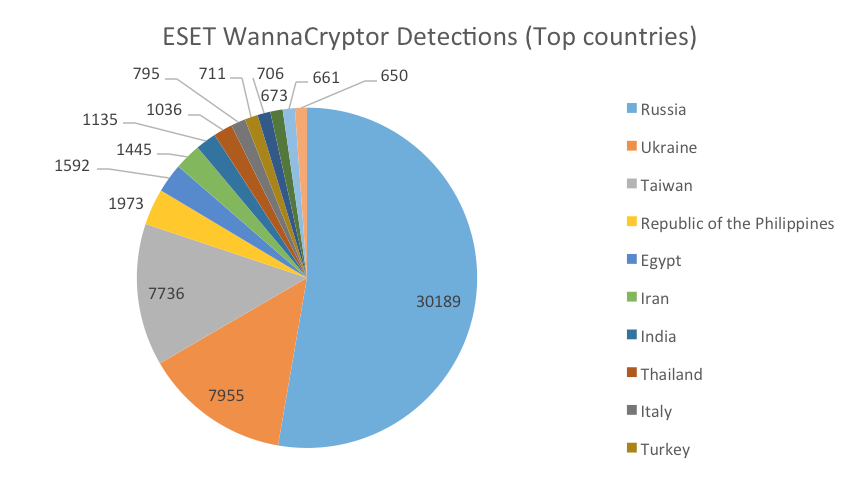
According to ESET systems, since only Friday, over 14,000 users out of those with enabled ESET LiveGrid® have reported as many as 66,000 WannaCryptor attack attempts on their devices.
These attacks were mainly targeting Russian computers, with over 30,000 attacks, followed by Ukraine and Taiwan, where in both cases they were close to the 8,000 mark.
The chaos that ensued after the WannaCryptor global outbreak seems to have motivated other black-hats to scale up their efforts too. We have seen a significant increase in the number of malicious emails sent out by the notorious Nemucod operators, spreading another ransomware: Filecoder.FV.
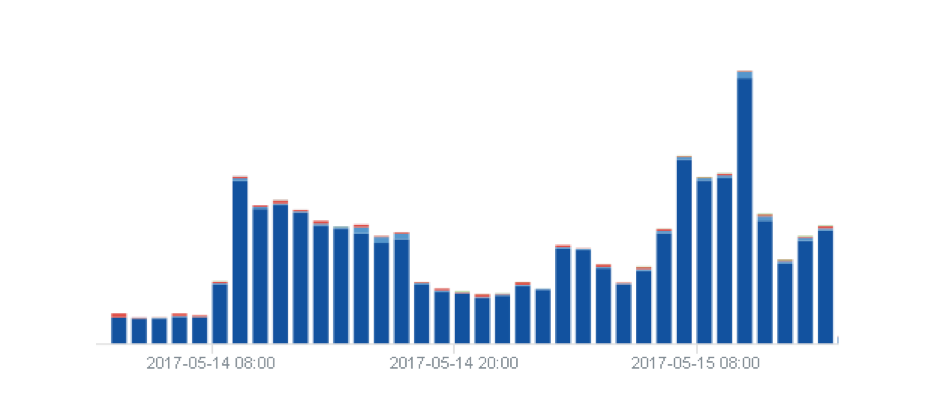
Figure 1 – Increase in JS/Danger.ScriptAttachment (Nemucod operators) detections after the WannaCryptor outbreak.
Also, WannaCryptor fakes have emerged trying to ride the wave of its fame by using the same GUI and layout. However, the encrypting capability was missing in all seen instances.
What should you do to stay safe?
- The EternalBlue exploit uses a vulnerability in the Windows that has been already patched by Microsoft, so the first thing would be to update and patch your operating system.
- Use a reliable security solution that utilizes multiple layers to protect you from similar threats also in the future.
- It is best practice to keep backups on an offline hard disk or location that will not be hit in case of a network infection.
- We recommend that users don’t pay the ransom – be it the case of true WannaCryptor or any other ransomware. There were no reported cases where such step would lead to decryption. On the contrary, there have been multiple stories documenting the opposite – no decryptor or key being sent after the payment was made. Also, there seems to be no way for the attackers to match the payment to the specific victim who sent it to one of the shared BitCoin wallets.
For more on the WannaCryptor, aka WannaCry, ransomware attack, check out this feature, which answers some key questions.




