Pyotr Levashov must be regretting his decision to go on a family vacation to Barcelona.
The 36-year-old Russian computer programmer was arrested by Spanish police on Friday in a joint operation with United States law enforcement agencies.
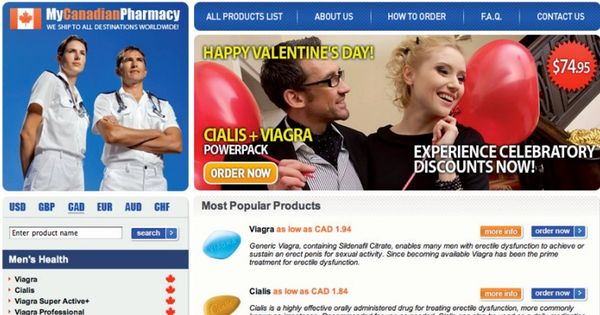
Levashov is accused of running the sprawling Kelihos botnet, which for several years has been commanding tens of thousands of Windows computers to spam out malware campaigns - including password-stealers, ransomware and fake anti-virus attacks - to innocent users' inboxes, as well as phishing emails, and advertisements for counterfeit drugs, make money fast schemes, and pump-and-dump stock scams.
Billions of malware-infected messages are thought to have been sent out by the Kelihos botnet every day.
US court documents allege that Levashov, who is also said to have gone by the online handle of "Severa", advertised his botnet for rent on underground message forums - offering to deliver one million spam messages for "legal" products such as adult websites, cheap mortgages and counterfeit goods for just $200. The price would rise, however, to $300 per million messages for spam designed to recruit money mules, and as high as $500 to distribute phishing attacks and scam emails to a million inboxes.
Now the US authorities have announced that they are working hard to dismantle the Kelihos botnet, preventing further infections by blocking malicious domains associated with the Kelihos botnet.
US law enforcement has obtained a warrant to redirect Kelihos-infected Windows computers to a substitute server, recording the IP addresses of affected PCs. The IP addresses of Kelihos victims will then be shared with other bodies who can assist with the removal of the malware, such as internet service providers.
Curiously, shortly after Levashov's arrest, Russian media reported his wife as claiming that his arrest was connected to the creation of malware linked to the presidential campaign of Donald Trump, although no mention of this is made in any of the legal documents released by the US Department of Justice, and officials at the DoJ have debunked any such association.
Pyotr Levashov has long been on the radar of US cybercrime investigators, having been charged back in 2009 with operating the "Storm" botnet - the precursor to Kelihos.
ESET researchers have previously described some of the characteristics and campaigns wrought by the Storm/Kelihos botnet in a technical paper: "Same botnet, same guys, new code".
There's no doubt that a life of cybercrime can earn its most successful overlords a considerable amount of money, but you will always have to live with the fear that you could be apprehended and - if convicted - spend years in prison. We have yet to see whether the US authorities are able to successfully convict Levashov for what he is alleged to have done, but he is surely already regretting that his trip to the sun.