Over the course of two days at last month's Computer Security Congress, which was organized by la Coordinación de Seguridad de la Información/UNAM-CERT, researchers presented their work in various areas of security.
In the course of his participation, security specialist José Miguel Baltazar Gálvez presented a study entitled Identifying the Original Source of a Digital Image, a development of the Master’s Program in Security and Information Technologies of Mexico’s Instituto Politécnico Nacional, aimed at recognizing the make and model of a device used to create a digital photograph during the forensic analysis process.
Challenges in the digital imaging forensic analysis process
The increased use of electronic devices and their various features has been a factor in the development of the technical profile of a digital forensics analyst, a role responsible for ensuring certainty in the use of digital images intended to be used as evidence in legal investigations.
"The forensic analysis of digital images has become more significant in determining the origin and authenticity of a photograph."Since images can be used to determine responsibilities – or as part of evidence in administrative, civil, or criminal cases – the forensic analysis of digital images has become more significant in determining the origin and authenticity of a photograph in order to link an individual to a device, place, or event.
And since there are currently increasingly sophisticated image manipulation tools available, which make it difficult to identify characteristics of interest, it is fitting to apply this type of technique.
In this area, the main challenges facing analysts are to determine the origin of a digital photograph, the specific make, model, and device used to create the photograph, and whether the content in the image has been added, deleted, or modified.
Standard Operating Procedure (SOP): A proposal for analysts
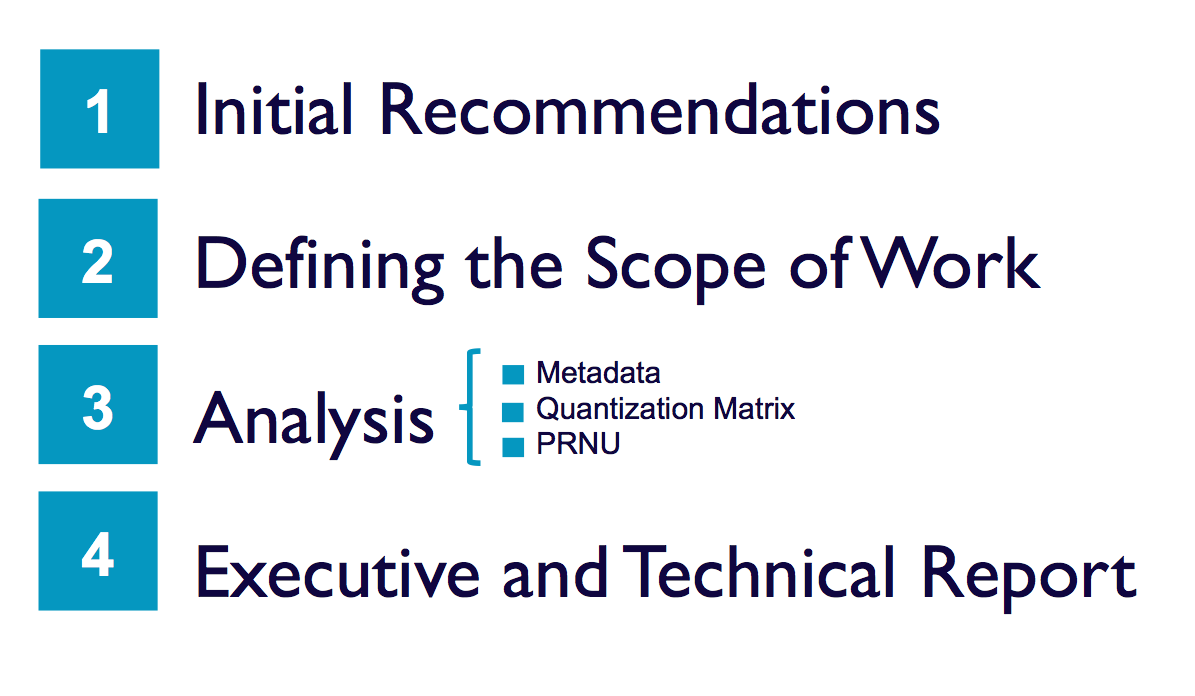
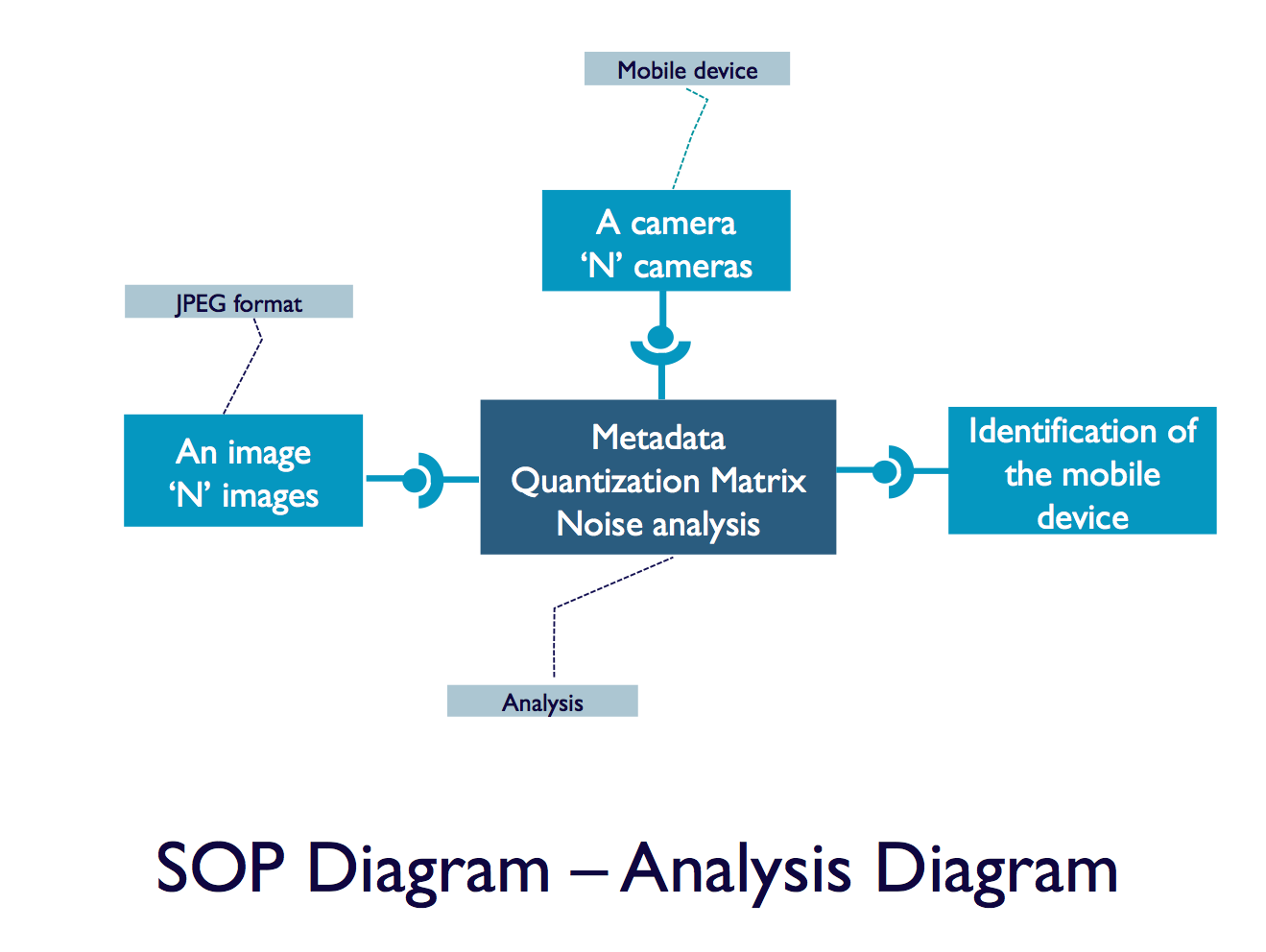
The research conducted by Baltazar Gálvez focuses on developing a Standard Operating Procedure (SOP) for identifying the image source using three techniques: analysis of metadata, analysis of the quantization matrix and analysis of Photo Response Non-Uniformity (PRNU). This SOP includes the following steps:
- Initial recommendations
This first stage involves creating the ideal conditions for identifying information of interest. Evidence (JPEG images) is acquired to start with, and preferably from two copies to ensure their integrity. The next step involves defining and properly managing the chain of custody, the safeguarding of evidence, and the characterization of the mobile device of the study.
- Defining the scope of work
The second stage focuses on the methodological application of the SOP. And since the purpose of the procedure is to identify the specific make, model, and device used to acquire a digital image, the organization of information is crucial for obtaining favorable results. Therefore, the following possible scenarios must be considered: one image related to a device, multiple images associated to a device, or several images related to multiple devices.
- Analysis and development techniques
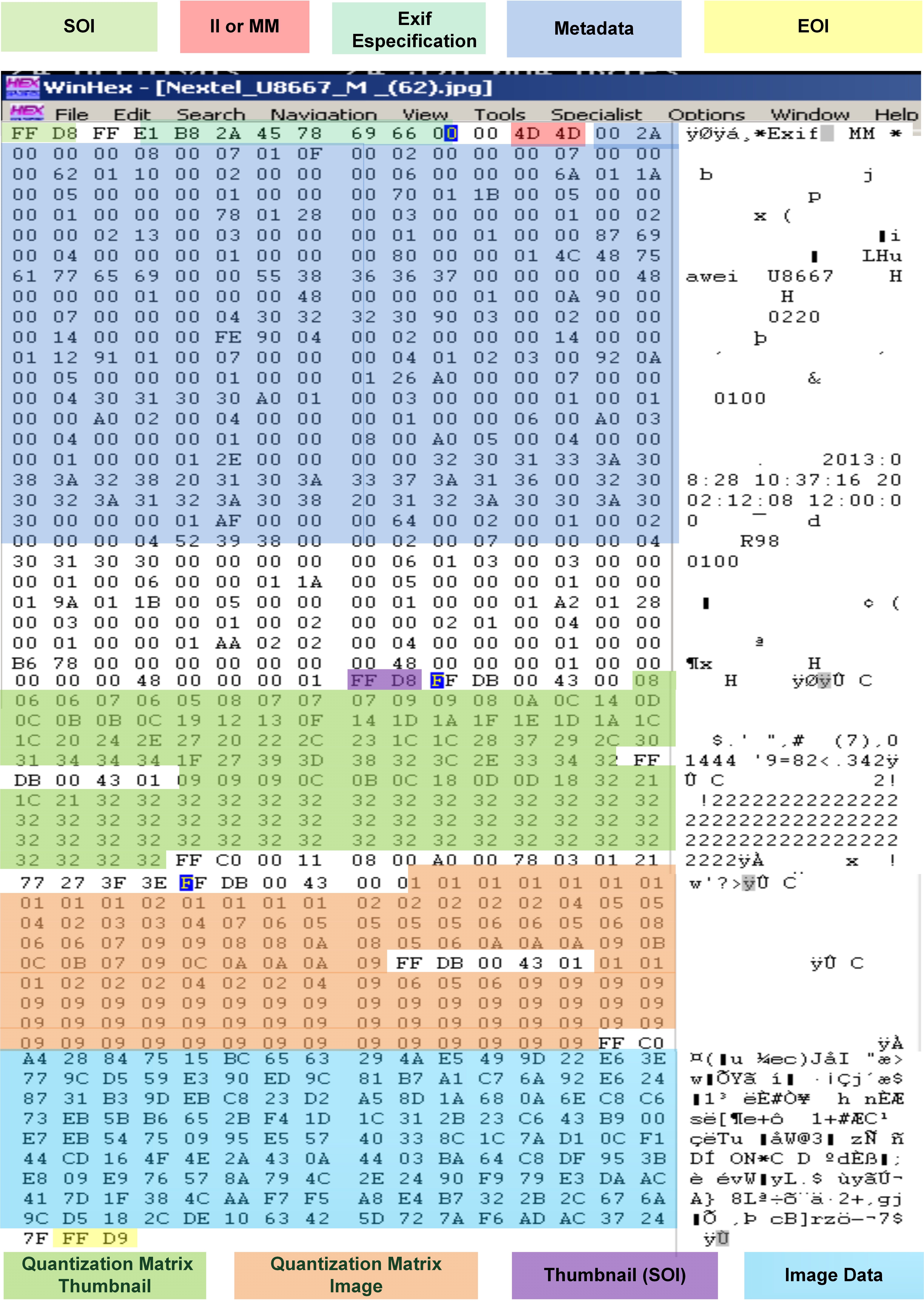
Metadata. The first analysis technique involves metadata, in which the data for the make and model of the device being studied is extracted, and then compared to the information of a reference image. Analysts must consider other technical elements during this process, such as the version of the software used, geolocation, or date of acquisition, so that this information can be correlated with other events. Although this is basic analysis, it is possible that the image has been altered, or that the metadata has been modified, so other techniques must also be used.
Analysis of the quantization or quantification matrix. To apply this technique, a reference is also required to carry out a comparison, but in this case the quantization matrices of each image are counted and extracted. Also known as the quantification matrix, it is a set of values used for representing this image; the number and content of each matrix are checked in this analysis. As in the previous case, if the image has been modified or the devices characterized are the same make and model, it is necessary to utilize another type of analysis, in this case PRNU.
Analysis of Photo Response Non-Uniformity (PRNU). Photo response noise is a characteristic of every sensor in a digital camera. In this analysis, it is necessary to have flat images (under the same light conditions with no scene) with the device, which allows a reference PRNU pattern to be generated. The PRNU pattern of the image to be analyzed is then obtained and contrasted through a correlation process. A digital image acquired with the device in question obtains a correlation value close to one, whereas for images that were not obtained with the analyzed device, the correlation values tend to be zero or may even be negative.
- Executive and technical report
The last phase of the procedure involves generating an executive and technical report on the results of the comparisons, based on the standard operating procedure. To do this, the information produced by the different analyses applied to the images studied is recorded in a document.
Analysis techniques and tools for digital forensic analysts
As part of his contribution, José Miguel presented the “AnálisisJPEG” tool for automatically comparing metadata and quantization matrices. At the end of his participation, he concluded that “the procedure and techniques proposed are a tool to help analysts”. For this reason, a thorough investigation must be carried out so that the information can be used as evidence in legal proceedings or simply to determine responsibilities.
Lastly, he recommended broadening the scope of existing techniques and developing new methods of analysis in the field of digital imaging. He also emphasized that the techniques and tools require interpretation and correlation with other events so that analysts can issue definitive conclusions.