There are a great many tools available to help quickly analyze the behavior of mobile malware samples, making the task easier for analysts, testers, and pen testers. In the case of Android, one such app is AppMon, which, through its binary instrumentation, provides access to the log showing which functions are being used and their respective parameters.
In this article, we will take a look at how it works.
How does AppMon work?
This app makes use of a powerful multi-platform dynamic instrumentation environment which we have already talked about a few times: Frida. AppMon includes a series of scripts based on this platform which enable analysts to spy on events triggered on the system by the app being studied, the results of which can then be viewed through a web interface with filters for searching and ordering.
As well as this, AppMon includes scripts which enable the user to intrude into the app, modifying its normal course of action, as can be seen in the video below. Of course, the analyst can also add their own scripts to the tool.
Furthermore, it enables the deployment of apps on both Android and iOS and, benefiting from Frida's flexibility, it can be run on multiple platforms (Linux, Mac OS, and also Windows by making some changes to the code).
Installing the app
The prerequisites for running AppMon are obviously to install Frida and also some Python modules, which can be done through the following command:
sudo -H pip install argparse frida flask termcolor
Then we can copy the project from the Github repository or download the corresponding compressed file. If you are using a Windows machine, you will also need to change the absolute path defined in the merge_script_path variable of the appmon.py file to point to the temporary folder in the Windows file system or indeed any other folder as required. For example, it may end up as follows:
merge_script_path = ‘C:/Users/<nombre_usuario>/AppData/Local/Temp/merged.js’
We have to create our own emulator with Android 4.4.x as Frida has only been demonstrated to be stable for 4.4.x, so that we can then transfer the files to Frida and launch the server, as we did previously in the tutorial for app deployment.
We're ready to go! Now we need to install the app we want to analyze. The best way to do this is via adb, because some emulators launch the app when it is installed via drag and drop, and if we are not ready to run the AppMon command we may fail to log some critical functionality.
Analyzing the sample
Let's run a sample of Android/Torec.A, a malware capable of logging messages and calls made and received on the device, as well as other critical information, and which can communicate via Tor. The app's Android Manifest file tells us that the packet's name is com.baseapp. We need this information so we can tell AppMon which process to intercept.
Next, we use our console to send the commands shown below:
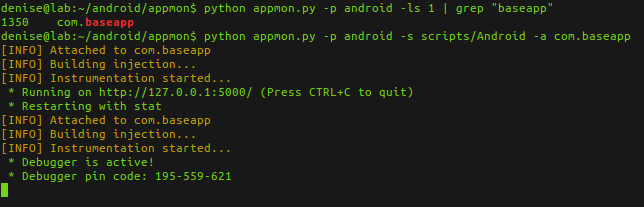
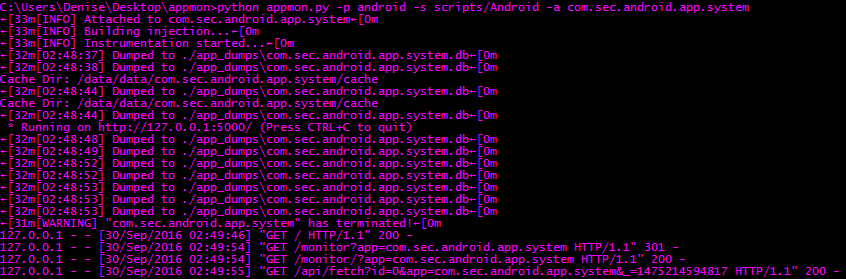
If we are on Windows, the console will look like that shown in the following image. We can see that AppMon creates a simple server using Python, which by default is launched on port 5000, where we can then access the filtering web interface, but only after we see on the console that something has been dumped.
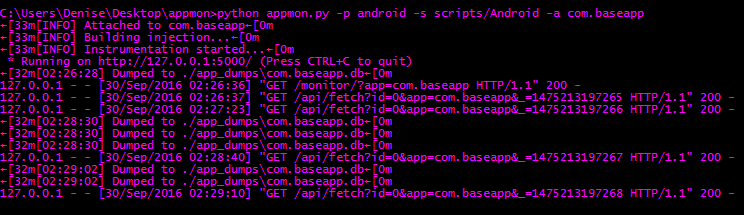
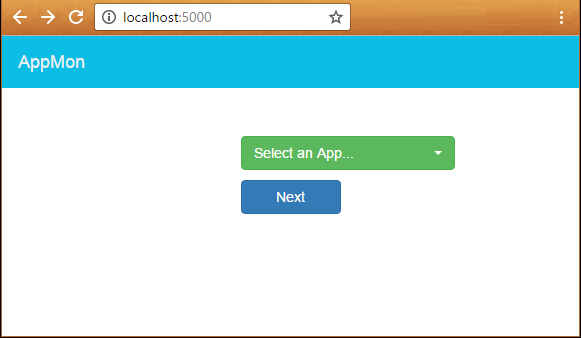
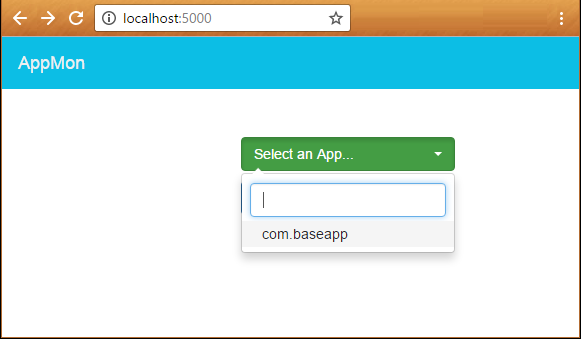
Then we can open the browser, select from the list the app we want to analyze, and click “Next”.
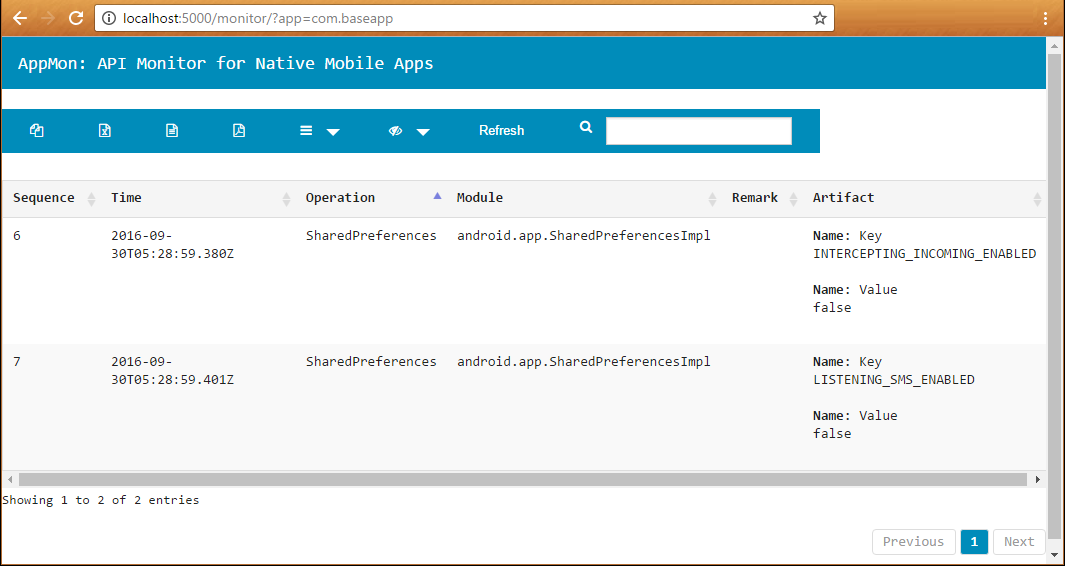
An event log will open, where we will be able to see some operations which have taken place on the system during the brief execution time:
Now let's carry out the same process with a sample of Android/Monitor.Rasatremon.A, which is a “couple tracker” app that has been deployed widely in Brazil. We install the app and launch the tools:
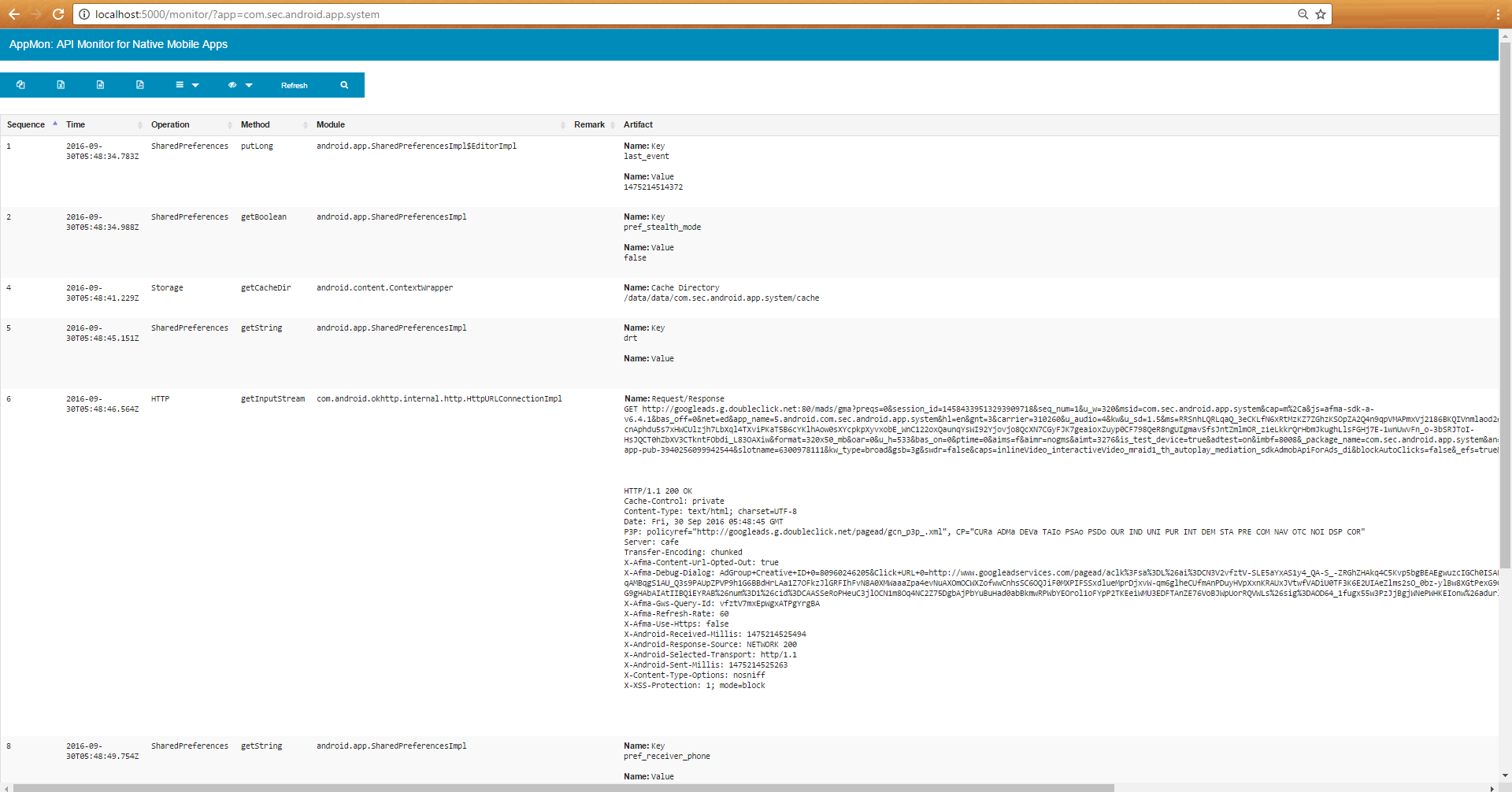
After using the app for a while, we can see the results in the browser, among which we find full details of which network packets have been sent using the HTTP protocol:
This is a brief demonstration of what AppMon is capable of. Likewise, the app enables us to recover encryption keys and many other parameters, depending on the analyst's needs. All in all, it's a great app for cutting the time needed to carry out an analysis.




