Some people change their smartphone or tablet almost as casually as they change their clothes. They buy and later sell mobile devices without the slightest concern about the information that, one device after another, they keep putting in the hands of total strangers. This article is aimed at all those people, and in it you will be able to learn what measures you can take to protect your privacy.
When you delete a file, is the data really deleted?
Unfortunately, no. With most IT equipment, deleting a file means telling the system that the next time it needs to write data, it can overwrite the space used by the file in question.
However, until the new write operation takes place, the information remains physically stored in the form of bits on the corresponding storage drive and can be recovered. This kind of deletion is known as logical deletion and is the procedure that almost all operating systems use.
In contrast, there is another kind of deletion called physical deletion which modifies the data bit by bit, by creating junk content on the storage medium. This procedure ensures that the data cannot be recovered, but it takes much longer and therefore usually is considered undesirable for tasks where the user experience is central.
What happens if you restore to factory settings?
That depends on the platform. Research carried out in early 2015 showed that on Apple and BlackBerry devices, when you perform a factory reset, the deletion of data is physical, thus preventing the information from being recovered later. However, not all Android devices were as lucky and it was possible to recover a lot of the data that had been stored on them.
RELATED READING: What to do you if your phone is lost or stolen
According to the researchers, the reason for this could be that Apple and BlackBerry have better control over their hardware and so can wipe the data on the device more effectively. Given that operating systems like iOS use encryption built into the hardware by default, factory reset only actually needs to delete the encryption keys physically.
In contrast, encryption is not included by default on Android and, according to the researchers' findings, information can be recovered even after running several factory resets.
What are the dangers of logical deletion?
Cell phones are very personal devices. Using them involves the use of totally private data, like credit card details, purchase records, contact details of friends and family, videos, photos (possibly including nude images of the user), schedules, geolocation, files and their associated metadata, web browser history, Wi-Fi connection history, logins and passwords for email and other cloud-based services, text messages, chats logs on social media, and a great deal of other information.
All this smartphone data could potentially provide material enabling a cybercriminal to orchestrate a social engineering attack against the handset's owner. Unfortunately, as some people have experienced first-hand, if this information falls into the wrong hands it can even lead to extortion and fraud in which the criminal blackmails the user by threatening to distribute the data.
Another great worry is that strangers might gain access to user accounts for apps installed on the device, like online shopping, banking, and social network apps. For this reason, taking preventive measures will enable us to feel more at ease and be better protected against such risks.
How can another person recover our personal information?
There are numerous tools designed to recover data stored physically on a mobile device. These utilities are known as forensic analysis tools and normally are used to break down the sequence of actions that led to an IT incident or to find evidence that could lead to a verdict in a court case.
However, some of these tools are free and can be accessed by people with malicious intentions to gain information they should not have access to.
So, how can you protect yourself?
As we already mentioned, for iOS users, a factory reset is sufficient. But what should Android users do? The simplest option for making it difficult to recover data is to encrypt the device before restoring the factory settings. That way, although someone could make a physical copy of the device, the bits of data stored on it will not make any sense to them.
Given that the decryption keys are, in turn, protected by the password set by the user, and even in the event of an unsuccessful reset, the attacker would have to carry out a brute force attack against the keys in order to gain access to them. And let's not forget that the more complex the password, the more difficult it will be to crack. This means that although encryption is not an infallible form of protection, it's enough to discourage most cybercriminals.
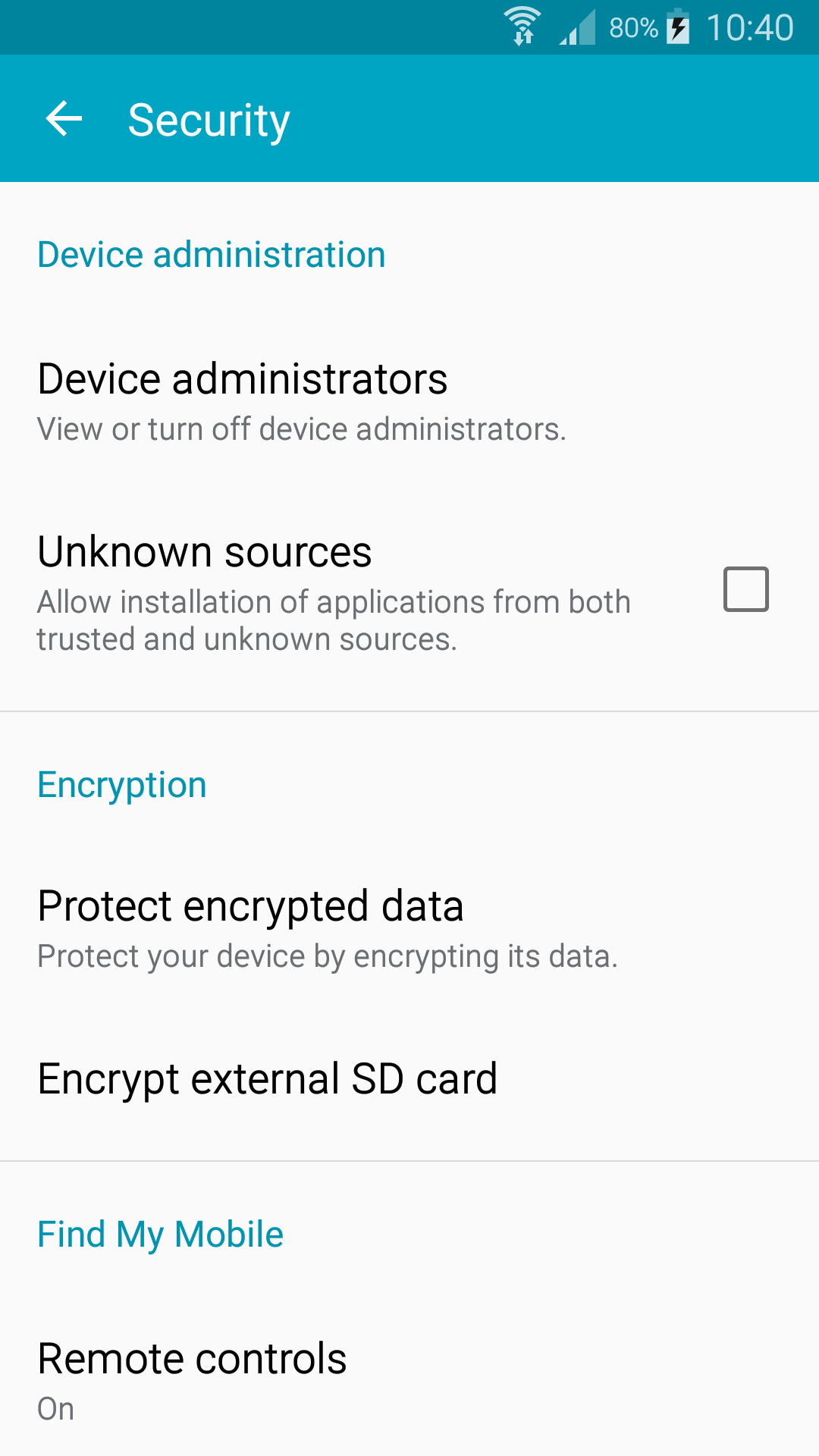
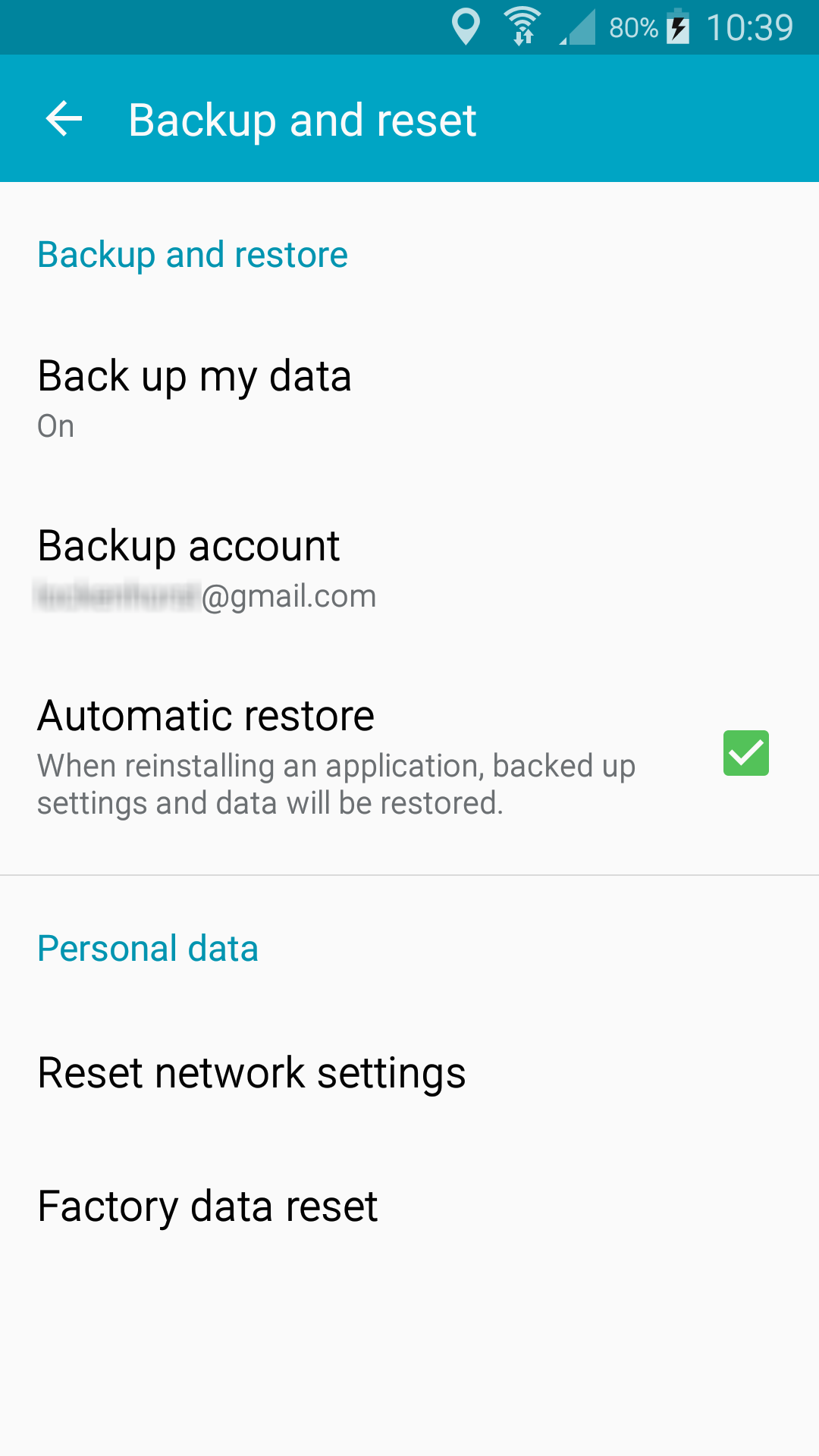
You can encrypt your Android system by going to Settings > Security > Encrypt device, and the reset options are located in Settings > Backup & reset > Factory data reset. Another way to format the memory is by accessing the device's recovery mode, however, the results of this method are the same.
It is also possible to find apps on Google Play Store that promise to overwrite the parts of the memory that have been marked as free by the operating system, but that might still contain the original data. The user will need to carry out a factory reset both before and after running the app. In addition, they will need to avoid using Google Play Store to install the app on the cell phone, so as to avoid entering their Google account data into the phone again.
Finally, don't forget to remove the SIM card and also the micro SD card. Now that you know how to wipe your data, be sure to protect your privacy before getting rid of a device.