Almost a year ago we warned about the spreading of Remtasu, and far from lessening, we have been able to identify numerous instances of this threat being propagated further.
Win32/Remtasu.Y variants are the most common in Latin America, mainly in Colombia but also in Turkey, Thailand, and other countries. One of the latest campaigns has been associated with a malicious tool supposedly aimed at obtaining Facebook account passwords.
Changes in social engineering
Up until last year, it was common to encounter campaigns associated with known entities such as DIAN, Avianca and Falabella in e-mail attachments with names related to collection accounts and invoices, concealing themselves to look like Microsoft Office files.
Although this type of ruse remains a threat, we have uncovered new ones using different Social Engineering mechanisms, such as Facebook, and the constant desire of a lot of users to take control of accounts from this well-known social network.
Although these files are from the same family as those witnessed last year, the way they are being spread is different. We are no longer seeing propagation through e-mail. They are instead coming from direct download sites. Once a user downloads and executes the file, their data is compromised.
Different means of propagation, similar behavior
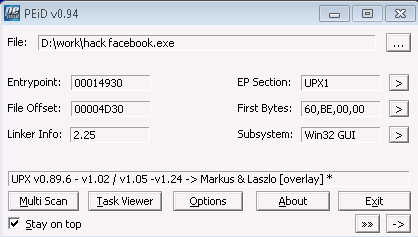
One of the examples examined by the ESET Research Labs can be associated with exactly this type of trick. One particular feature we found was the use of UPX compression.
Once the file was uncompressed, we were able to see the functions implemented in the malicious code, giving us an idea of the scope of this kind of threat.
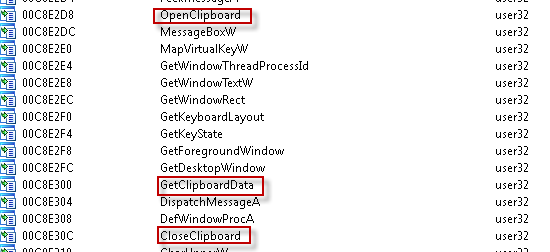
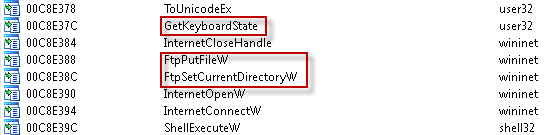
For example, this variant has the specific feature of opening and obtaining information the user has in their clipboard. As well as being able to access this data, the malicious code can capture keystrokes and store all the information in a file which is subsequently sent to an FTP server, as can be seen in the imported libraries.
As is to be expected in this type of threat, the virus always seeks a way to remain on the computer even when the victim reboots their system or attempts to find the threat in the list of active processes.
In this case, the malware replicates itself, saving the copy in a folder that it also creates within the system32 folder. The new InstallDir folder remains hidden inside the system files, making it difficult for users to access.
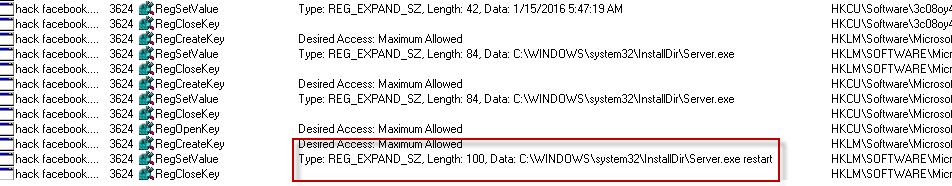
The copy of the malicious code uses a name that can give rise to confusion among users, even if they seek out information about the virus on the Internet. Differing from previous instances, where the filename was similar to system processes such as csrss.exe, for example, in this case the name is fairly generic. This leads to doubts in users' minds as to whether or not it is a legitimate or a malicious process.
Win32/Remtasu in 2016
It is important to point out that in the first weeks of 2016, we have witnessed 24 different variants of this family of malicious code being spread, with Win32/Remtasu.Y representing over a quarter of those detected, closely followed by the variant Win32/Remtasu.O at 23%. This means that almost a half of the viruses detected from this family correspond to just two variants.
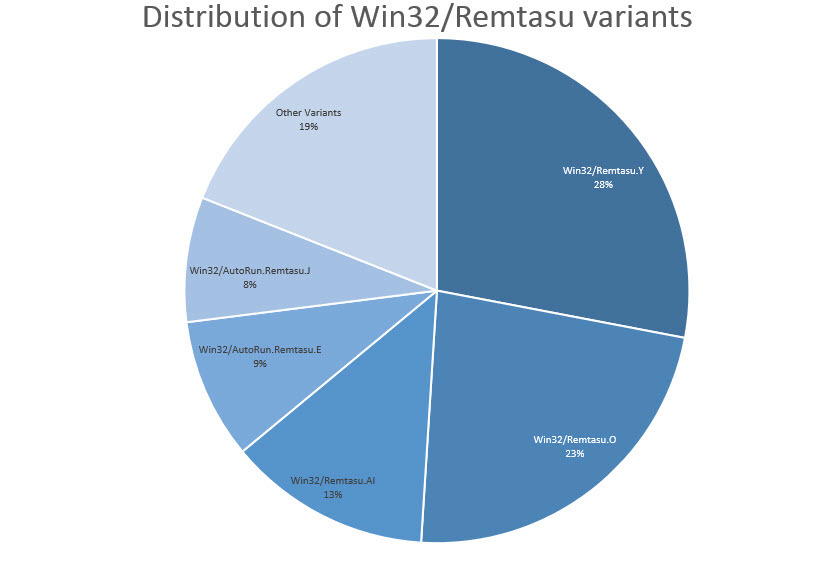
As a further data point, it is worth mentioning that 65% of Win32/Remtasu instances were detected among users located in Colombia. Thailand provided the second largest number of instances detected at 6%, but this is mainly the variant Win32/AutoRun.Remtasu.E, which differs from the cases seen in South America. The third and fourth place countries are Mexico and Peru, with 3% and 2% respectively.
We should note that although having security software can help in detecting malicious content that tries to download itself, taking care over what you click on will always bring further protection against such threats.
For our part, the ESET Research Labs will carry on analyzing these and other similar viruses to keep you informed about the characteristics of the threats we see in the region.
Sample analyzed
| SHA1 | Nombre del archivo | Detección |
| 03AA8D8BFDF54BF390B03D1886E34C71865592EA | hack facebook.exe | Win32/Remtasu.Y |




