On Monday, Google released the latest security update for Nexus devices running Android, as part of its previously announced plan to roll-out over-the-air patches on a monthly basis.
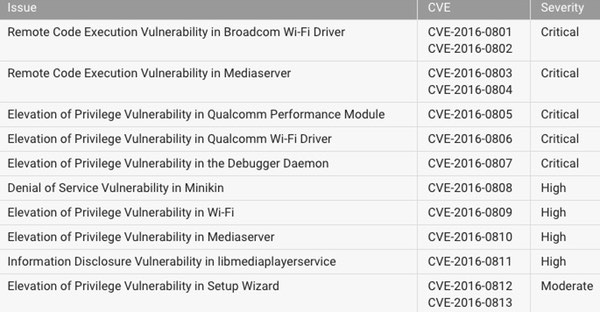
The most serious flaws, given a severity rating of critical, could lead to remote code execution - with malicious hackers running code on your device, without your permission or knowledge, without needing physical access.
For instance, the bug in Mediaserver could mean that simply opening an email, browsing a website or receiving a media file via MMS could mean that in the blink of an eye, malicious code is being run on your Android device.
If this sounds familiar then chances are you remember Stagefright, one of the biggest Android security scares of last year, which actually resulted in Google realising it needed to get more serious about patching Android and rolling out updates to users.
And then there is the critical remote code execution vulnerability in Broadcom's Wi-Fi driver, that could allow a hacker to run code on your Android device if they are connected to the same network as you, by sending boobytrapped wireless control message packets.
Clearly, these are vulnerabilities that nobody would want on their smartphone.
So, if you have a Nexus device my advice is that you should patch it as soon as possible. If you are comfortable with a bit of nerdiness you could download the latest firmware images from the Google Developer site. But most people, I would imagine, will prefer to wait until the updates arrive over the airwaves in the next few days.
 But remember this - these are flaws in Android, and the Nexus is just one brand of Android smartphone.
But remember this - these are flaws in Android, and the Nexus is just one brand of Android smartphone.
Google says that it informed its partners about the security issues described in the bulletin "on January 4, 2016 or earlier", so if you haven't received an update yet from your manufacturer/carrier then it's time to start the stopwatch.
Sadly, I strongly suspect that in some cases you'll find yourself waiting forever.
Over-the-air updates for Android are notoriously hard to get hold of for some devices.
Even if you desperately want to upgrade the operating system on your Android phone or tablet you might not be able, because update availability depends upon the assistance and goodwill of three separate parties: Google, your phone's manufacturer and your mobile phone carrier.
History, sadly, shows us that older Android devices are often left stranded without an easy update path. Although it may not be technically possible to deliver a patch to devices which may not have the power or resources to run the latest and greatest version of Android, more manufacturers need to follow Google's example in creating an easier path for OS updates to fix newly-found vulnerabilities.
This is a serious problem which, bearing in mind the regularity that critical security vulnerabilities are found in versions of Android, really needs to be fixed so fewer users are left in the lurch.




