Whatever your views on the AshleyMadison.com website, the data breach it suffered earlier this year has increased the cybersecurity threat level for all organizations. That's because a large amount of information stolen from the site was published on the Internet last week, all of which can be assumed to be sensitive, given the site's infamous slogan: "Life is short. Have an affair." In terms of IT security you should be taking action on several fronts. In this article I suggest four action items every organization should consider, but first I explain why an Ashley Madison response plan is needed.
What companies need to know
Right now, as many as 30 million people, most males, mostly in North America, could be dealing with the fact that sensitive information about them may have been published on the Internet last week. The files were made public by the criminal or criminals who stole them from the Canadian company, Avid Life Media, which operates several dating sites, including AshleyMadison.com. Some of the people listed in those files may work for your company, but that is only one aspect of how the situation could impact the security of your organization. Here are the main threats as I see them right now, although others may emerge:
- Phishing: Intense interest in the Ashley Madison data makes it ideal bait for email and SMS phishing campaigns, designed to trick people into clicking on links to websites or attachments, potentially revealing identity data and credentials, not to mention infecting systems with malicious code. Targets extend well beyond people who actually visited AshleyMadison.com; they include anyone keen to know who visited AshleyMadison.com (think suspicious partners, friends, family, employers, government agencies, and so on).
- Blackmail: Threats to reveal a person's connection to Ashley Madison have already been made and payments for silence have been noted. By my calculation, as many as one in five US males between 20 and 74 could have some connection to Ashley Madison* (remember, Avid Life Media did not delete information when people cancelled).
- Scams: A wide range of ethically-challenged entrepreneurs will seek to exploit the current situation, for example making offers to remove a person's information from the Ashley Madison files (just to be clear, that is impossible to do). Look for HR (human resource) departments to be targeted with offers of "cheater lists". Expect other forms of access to the stolen data to be offered to a curious public for a fee, fraudulently of course.
- Departures: Some people may feel obliged to quit their jobs if their connection to Ashley Madison is revealed. Depending on their role in your organization, this could have a serious impact on productivity, morale, corporate knowledge, and so on. Of even greater concern is the possibility of suicide, with several possible cases already under investigation.
What was revealed?
Before getting to the action items, it is important to be clear about the current situation. The data stolen from Ashely Madison is now available to anyone suitably versed in MySQL and Excel who wants to go find it and download it, although doing so is in itself a risky proposition (you can safely assume that there will be many bogus offerings as well as infected packages, as shown in our previous article). The data includes records of accounts that people created on the website and credit card transactions used to pay for various features. In developing your response plan it is important that everyone involved understands the following:
- Simply knowing that a person's name or email address is in the Ashley Madison data dump tells you nothing about that person or their moral standing.
- Many fake accounts were created in the names of real people.
- Many fake accounts were, allegedly, created by the company in order to pad membership, notably female members.
- Many people only showed a passing interest in the website, yet their data was captured and retained.
- Some people who were curious about the site registered but decided that was a mistake and requested that their information be removed; however, Avid appears to have ignored many such requests and retained the data.
- Although fake account names and non-obvious email addresses were widely used by visitors to the site, many real names do appear on the credit cards that they entered on the site (also, the company also appears to have started requiring email addresses for credit card transactions after 2010).
- Many people went to the website with no intention of having an affair.
- Many people went to the website with no intention of doing anything unethical or immoral (think singles, divorcees, widows and widowers, open marriages, and so on).
Regardless of your personal beliefs or the corporate culture of your organization, the most pragmatic way to approach this whole situation is probably through empathy and understanding, not judgmental moralizing. The latter is apt to result in false accusations and a climate of fear which is not conducive to resolving matters efficiently and effectively.
Response plan action items
These response plan action items parallel the threats noted above. How you implement the items will obviously depend upon company size, structure, and culture. However, I urge you not to simply ignore them because you find the whole situation distasteful.
- Phishing: Send out a message to all employees letting them know to be on alert for Ashley Madison related messages in email or texts. Warn them not to open such messages. Explain that clicking on links in, or attachments to, such messages is a very bad idea. Of course, you may well have filtering and detection software installed at various points in your systems. But make sure these are fully updated and operational. And do not rely on them. Alerting your employees is also important, not least because their home systems may not be similarly protected, leaving open possible routes of infection from personal accounts to work systems.
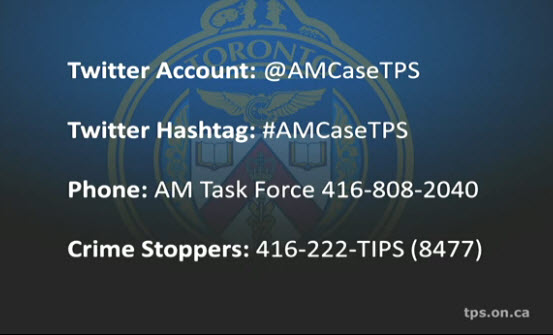
- Blackmail: Let all employees know that they there is someone within the organization to whom such attempts can be reported, in confidence, and without judgment. Also share the contacts published by the Canadian law enforcement agencies that are investigating the situation:
- Scams: A company-wide communication on how to avoid Ashley Madison related scams, at home as well as at work, is a low cost preventative measure that could save a lot of people a lot of trouble and money. Even a simple statement will help: "Be advised that a variety of scams related to the Ashley Madison data breach are likely to target people online and possibly over the phone. All offers to remove a person's information from the leaked files are bogus. Some companies are offering "email lookup" services access as a way to gain addresses for spam. Offers of "cheater lists" and other access to the leaked data are also likely to be fraudulent, not to mention illegal. If you have any questions on this or related matters, you can discuss them in confidence by [insert contact process/name here]."
- Departures: A good HR department will already have processes and resources related to suicide prevention. Now is a good time to refresh those and let employees know that help is available. Also consider a communication to managers and supervisors, alerting them to the facts of the situation and urging alertness for signs of employees in distress. A reminder to handle any aspects of the Ashely Madison matter with sensitivity would also be a good idea. For the record, the Suicide Prevention Hotline number for the US and Canada is: 1-800-273-8255; in the UK, the preferred number is Samaritans on 08457 90 90 90; Australia has Lifeline on 13 11 14; and suicide prevention hotlines for other countries are listed here (with thanks to Graham Cluley for rounding these up).
These four action items are the main ones that I see right now, but you may have thought of more. Please use the Comments to share. Bear in mind that, regardless of what you think about the Ashley Madison website and business model, the staggeringly irresponsible actions of the person or persons who illegally distributed this stolen data have created real threats to corporate and consumer well-being to which we need to respond calmly but effectively.
* With Ashley Madison claiming 37 million "users" assume 80% are in the US and 75% of those are male = 22.2 million. US census data for 2010 plus annual growth through 2015 indicates there are 105.8 million US males between 20 and 74 = 21% or 1 in 5 (22.2/105.8). Note that assumptions could be wrong, or the Ashley Madison starting number could be wrong. But even at 1 in 10, a US company with 100 male employees is likely to encompass a handful of "users".




