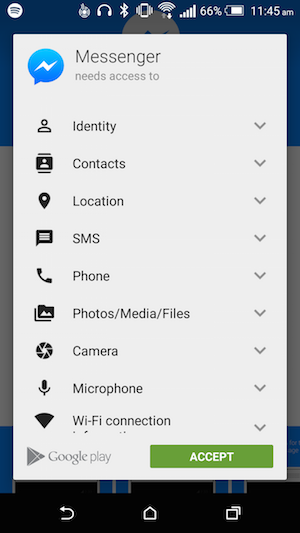
Mobile applications increasingly want access to various functions on your smartphones and tablets, such as your location and contacts book. But some of these app permissions should not be granted.
App Store, Google Play and Windows Phone store users will know by now that, when installing an app or using a particular feature for the first time, the app will ask their permission to access certain features of the device. For example, a map application will ask for access to the GPS, while VoIP and other voice-calling applications may require access to the phone and device ID.
On most occasions, this tie-up is a good thing, as it helps developers to offer better services and users to make the best use of their devices. However, there are times when these app permissions are unnecessary.
As a general rule, you should always be wary what apps you’re downloading and think about how they’re used and if you trust them. App permissions can usually be restricted via settings, remember.
Location
App developers’ wanting your location is perhaps the biggest problem area at the moment, and for good reason.
Allowing GPS permission allows an app to determine the user’s location to suggest local coffee shops, restaurants, shopping centers and other places that may be of interest. But the risk is that this information, if seen by a malicious third-party, could lead to social engineering campaigns used against the user for future phishing attacks, or perhaps even opportunistic robberies.
Furthermore, and perhaps most likely, this harvested information could be sold onto advertisers for Minority Report-style location-based ads.
Messages and phone calls

Messages and calls are often on the list of requested app permissions.
Developers also often ask for permission to access your phone and messages. Text message widgets often require permission to messages, while the likes of WhatsApp and Facebook want it for SMS confirmation of your phone number. Both do this as a form of two-factor authentication.
Malicious messaging and phone call-related apps could trick the user into dialing or texting an expensive premium number.
In-app payments
A huge number of apps, especially in gaming, are available for free but make money via in-app purchases. For example, a user may pay $2.99 for new game features or content.
The obvious risk with this is, if you’ve set up payment details, and let your child play on the device without parental controls, the costs can rack up pretty quickly. These have been notable examples, and it was a big enough concern to push Apple to pay $32.5 million to settle the issue with the FTC.
Ensure you set restrictions in iOS, or set-up a PIN for in-app purchases on Android.
Photos

Some apps will ask permission to access your photographs and pictures.
Millions of people take to Instagram and other photo-sharing apps every day, but allowing an app this permission should be treated with caution.
For example, Instagram became embroiled in a legal challenge two years ago when, under its terms and conditions, it decided that images uploaded to its web servers would be under their copyright. One user found their image being used on T-shirts that were selling for under $10, while Vogue got in trouble for taking photos and not attributing them to the photographer.
If you’re going to accept this permission, check the developer’s terms and conditions carefully.
Device details
This permission allows the app to potentially tap into sensitive log data, retrieve your system’s internal state, read web bookmarks and history, and retrieve a list of running apps.
Most app developers want this data, sent in the form of log reports, so to see how their app is being used and how it can be improved. However, there have been some instances where these app permissions have been used to send sensitive private information about the user to analytics companies.
Full internet access

Generally its quite easy to spot why apps would legitimately need internet access.
Applications are increasingly asking for full internet access, which is okay if used for communicating online or any type of downloadable content. If it’s not, it might mean that you’re going to get hit by ads.
This is because to send you ads, the ad network needs to pull them in from the internet. If the app you're using is ad-free, has no need to contact the outside world, and doesn't have any type of add-on content, be very skeptical.
In addition, cybercriminals could also look to exploit this connectivity via malicious apps which, having been installed already, could be used to communicate back to their command centers to download malware. As such, you should always be sure to protect your device.
Wi-Fi
Enabling Wi-Fi to apps is virtually a no-brainer given almost all applications want to connect to the Internet. Accepting this gives apps access to Wi-Fi network information, such as the list of configured networks and the current active Wi-Fi network.
The dangers are that you do not know if the information, which may be being sent over the open Wi-Fi network by the developer, is secured, while cyber-criminals could also take advantage of device bugs to steal passwords transmitted over Wi-Fi. This was the case with HTC back in 2012.
Hadrian / Shutterstock.com