When I first saw people tweeting about it a few weeks ago I thought, "that sounds like a good idea."
Folks who stay at Hilton Hotels and are members of the company's HHonors program were being encouraged to update their PIN or password to a more secure password, in exchange for 1000 Hilton HHonors points.
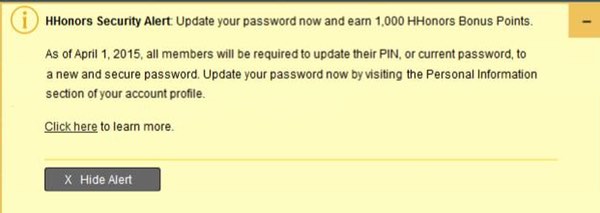
HHonors Security Alert: Update your password now and earn 1,000 HHonors Bonus Points.As of April 1, 2015, all members will be required to update their PIN, or current password, to a new and secure password. Update your password now by visiting the Personal Information section of your account profile.
Encouraging members (some of whom were using vulnerable four digit PIN codes) to change their login credentials to a more secure version sounds like a good idea - as we all know, human nature means that such a mundane task can be easily put off with a shrug of "I'll do that tomorrow."
 I must admit though that the wording used by Hilton made me raise a querulous eyebrow. "Security alert?"
I must admit though that the wording used by Hilton made me raise a querulous eyebrow. "Security alert?"
Sure, they were announcing that security would be tightening on April 1st 2015 and that four digit PINs would no longer be allowed, but if it was really an *alert* wouldn't they enforce a password change immediately?
For a moment I wondered if the Hilton HHonors site might have suffered a compromise that had instigated this change... but then forgot about it, and went about my day.
It turns out, however, that I might not have been the only one intrigued by the message on the Hilton HHonors site.
As security blogger Brian Krebs reports, vulnerability researchers Brandon Potter and JB Snyder discovered a vulnerability on the website which made it relatively straightforward to hijack any other user's account:
The two found that once they’d logged into a Hilton Honors account, they could hijack any other account just by knowing its account number. All it took was a small amount of changing the site’s HTML content and then reloading the page.After that, they could see and do everything available to the legitimate holder of that account, such as changing the account password; viewing past and upcoming travel; redeeming Hilton Honors points for travel or hotel reservations worldwide; or having the points sent as cash to prepaid credit cards or transferred to other Hilton Honors accounts. The vulnerability also exposed the customer’s email address, physical address and the last four digits of any credit card on file.
The vulnerability appears to have been an Insecure Direct Object Reference flaw, through which attackers could bypass authorisation and access database records directly.
Such vulnerabilities, unfortunately, are worryingly common in web applications and the threats typically come from an authorised user of a system altering a parameter value to access records that they shouldn't be allowed to access.
Krebs informed Hilton of the flaw, which says it has now fixed the vulnerability:
"Hilton Worldwide recently confirmed a vulnerability on a section of our Hilton HHonors website, and we took immediate action to remediate the vulnerability. As always, we encourage Hilton HHonors members to review their accounts and update their online passwords regularly as a precaution. Hilton Worldwide takes information security very seriously and we are committed to safeguarding our guests’ personal information."
Unfortunately, the site still reportedly fails to ask members to re-enter their existing password before setting a new one. That would be a simple step which would reduce the chances of account hijacking in future.
Of course, this isn't the first time that a hotel rewards scheme has found to have an alarming security hole. Earlier this year, Marriott International was forced to fix a vulnerability in its Android app that had left customers' personal details exposed.
If you run an organisation which collects users’ information, make sure you tightly control access to the sensitive data and build you website and applications with security in mind. After all, you don't want to be the next red-faced company having to admit that you had needlessly put your customers at risk.




