Over the past few years, counter surveillance gadgets which might have been the preserve of secretive government departments a decade ago have suddenly hit mainstream shops - from Mission Impossible-stlye self-destructing drives to some rather eerie counter-surveillance masks.
Whether it's Edward Snowden's revelations, or mass theft of private data such as the Target breach, people have have woken up to the fact that their data isn’t safe - whether from governments around the world, or from cybercriminals looking to sell it for profit.
These gadgets reflect that world. Each claims to offer ways to spy-proof your life, ranging from the sensible right up to gadgets fit for the tinfoil hat brigade...
Counter-surveillance mask
A Chicago artist has created a cheap, effective way for the public to fight back against the growing profusion of security cameras - rubber masks which make the devices unable to identify the wearer.
The URME device works very simply - everyone who wears the mask has the face of creator Leo Selvaggio, so biometric software is fooled into thinking the streets are filled with copies of the same person, according to CNET.
CNET describes concept images of same-faced clones walking together as “like Matrix 3.” Selvaggio says, “I have an overwhelming urge to protect the public from such surveillance. Everyone has a right to privacy.”
Selvaggio says, "Our world is becoming increasingly surveilled. For example, Chicago has over 25,000 cameras networked to a single facial recognition hub. We don't believe you should be tracked just because you want to walk outside and you shouldn't have to hide either. Instead, use one of our products to present an alternative identity when in public."
The product is made from a 3D scan of Selvaggio’s face, 3D-printed over a mesh by That’s My Face. The company seems to share URME’s libertarian views: they also sell a 3D action figure of Edward Snowden.
The ‘self-destruct’ hard drive
Merely wiping a hard drive or encrypting its contents seems not to be enough for anyone truly worried about surveillance - although good encryption is a good first step to spoiling someone’s day if they want to look through yours.
The new ultra-secure Autothysis SSD actually includes a built-in self-destruct device that smashes the memory chips to bits - and which can be activated by text message from anywhere.
You simply send a pre-programmed, ‘kill command’ from any phone, and the gadget smashes itself to bits. First the security processor smashes the NAND flash, then it smashes itself - and it activates if any spook attempts to open the drive as well.
The best bit is the remote-kill function: a built in execution device which fractures the Flash storage and security processor, which its makers promise gives, ‘the same result as taking a hammer to the drive’. Don’t imagine you’ll be able to do this too many times, though - each Secure Drives Autothysis will cost over $1500.
The iPhone case which turns your phone into a spy-phone
The Vysk iPhone case offers some smart ideas if you are keen to indulge in a bit of Bring Your Own Device counter-surveillance - it offers a hardware-based way to switch off the camera and microphone on two highly popular smartphone models.
Phone malware could, in theory, be ‘listening’ or taking photographs at any time, and having a foolproof way to block the camera and microphone is a fairly smart take on privacy.
The Vysk is available for iPhone 5S and Samsung Galaxy S5, and also offers built-in call encryption using a proprietary processor inside the case - and a subscription service offering encrypted messaging.
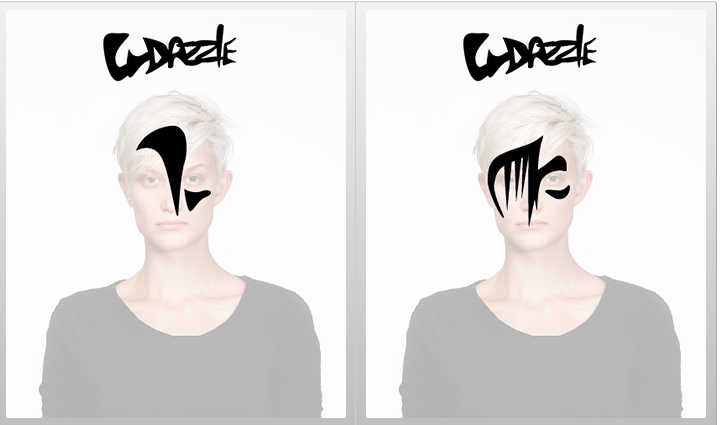
The anti-face-recognition makeover
Artist Adam Harvey created a series of fashion ‘looks’ which also have the privacy-boosting effect of blocking some of the most popular facial recognition algorithms.
It’s an interesting idea - and widely covered by publications such as the New York Times - but obviously depends on your knowing which algorithms any camera is using. This information is not always provided by the relevant government departments.
Harvey says, ‘The name is derived from a type of World War I naval camouflage called Dazzle, which used cubist-inspired designs to break apart the visual continuity of a battleship and conceal its orientation and size. Likewise, CV Dazzle uses avant-garde hairstyling and makeup designs to break apart the continuity of a face."
"Since facial-recognition algorithms rely on the identification and spatial relationship of key facial features, like symmetry and tonal contours, one can block detection by creating an “anti-face.”’
This phone will destruct in five seconds
Boeing’s Black phone takes ordinary paranoia to the next level - with a phone that actually ‘self-destructs in five seconds’.
Boeing furnished the world with scant technical details on its Black handset - to protect the safety of field operatives - but it ships with a ‘self-destruct’ button built in, which renders the entire gadget inoperable.
The 5.2-inch handset uses dual SIM cards to switch between government and public networks, and is built for encrypted calls, the company said. It can also run on solar power – its back panel is removable to add a variety of James Bond-esque gadgets, The Verge reports.
Tampering with the casing destroys the phone’s software – and all the data within it. Ars Technica quotes a letter to the Federal Communications Commission from Boeing’s legal counsel saying, "Any attempt to break open the casing of the device would trigger functions that would delete the data and software contained within the device and make the device inoperable."