* Clarke's Third Law: Any sufficiently advanced technology is indistinguishable from magic.
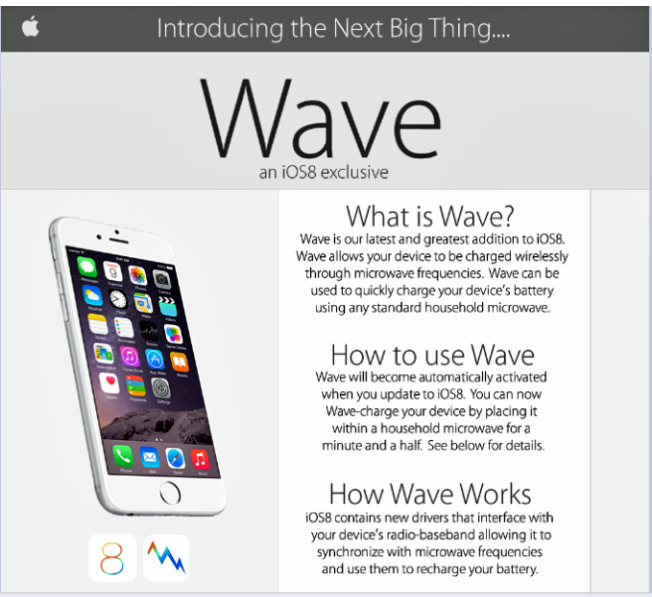
The starting point for this article at first struck me as being so ridiculous that I wasn’t sure whether or not to write about it at all, let alone at length: that is, the claim that you can recharge an iPhone using iOS 8 ‘Wave’ technology in a minute and a half by putting it in your microwave oven. Is anyone really going to fall for that? But then, unlike Mark Twain’s Hank Morgan, who is enabled by his 19th century understanding of technology and science to improve the lives of the 6th Century subjects of King Arthur, most of us in the 21st century have a pretty sketchy knowledge of technology that we don’t work with or use directly. Even Stephen Fry doesn’t know everything. In any case, knowledge of the human/technology interface is not, of course, the same as understanding the technology itself, or the science behind it.
Ordeals by Fire and Water
To the proverbial man on the Clapham omnibus, sitting there with his iPhone, it may be that the idea of a software driver that somehow magically alters the relationship between microwave cooking technology and that same iPhone is no more unlikely than the idea of broadband transmitted domestically through electrical wiring. (It’s even a little easier to swallow than the idea that upgrading to iOS 7 would make an iPhone waterproof, a hoax prevalent in 2013 and, like the microwave hoax, attributed by numerous sources to 4chan.)
Not Waving but Browning
There are some posts and photos drifting around the Internet that suggest that some have actually tried it out and discovered, as one wit described it, that their iPhones were toast. (And let’s not even think about the effect on the microwave of its conversion to helter smelter.) There is certainly some doubt as to whether some of the posts are just trolls at work (fol-de-rol), and some of those photos that have turned up (all done on that side) look suspiciously as if they have been borrowed from a 2012 YouTube video.
Certainly, our friends at Sophos thought it was worth flagging for the benefit of any of their readers who aren’t as proficient with technology as security bloggers are supposed to be. Indeed, Lisa Vaas made some very good points:
- iOS 8 certainly hasn’t repealed the laws of physics. (Of course, our understanding of the laws of physics changes over the time, and even now it’s an oversimplification to say that you can’t put any metal in a microwave, but it’s fair to say that microwave ovens and phones aren’t a good mix.)
- The graphic used to convince the victims was unusually well executed. It’s not so surprising if people really have been persuaded by it.
(The graphic as published by The Independent has a note at the bottom advising ’60 seconds at 100W or 70 seconds at 800W. Do not Wave-charge for over 300 seconds’, which strikes me as a particularly cute (in a bad way) example of social engineering.)
The ‘waterproofing’ hoax was also reinforced by a very Apple-like (but fake) poster.
How to Make one of the Seven Dwarves Grumpy
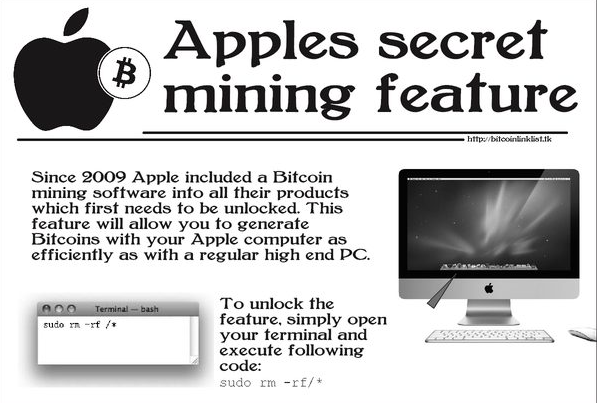
In fact, it’s not only iOS updates that inspire this kind of activity: also back in 2013, another hoax claimed that Apple had been including a Bitcoin mining feature into its computers that allowed Mac users to generate Bitcoins.
According to the hoax, all you need to do is to open the terminal app and run this command: sudo rm -rf/*
There is, of course, no such bitcoin mining feature. Unfortunately (for anyone who tried it without knowing what it really does), the command does exist, but what it actually does is to attempt to delete all files. It’s a slight variation on a command that Dr Fred Cohen – who in more than one sense ‘wrote the book’ on computer viruses – cited in one of his early books as an example of how destructive a small program can be (in that case the command was rm -rf $HOME/*). Here, to save me some typing, is an extract from one of my other blogs that explains exactly what these commands really do:
- sudo allows, potentially, an unprivileged user to use a command that otherwise has to be run by a user with administrative privileges.
- rm is a Unix command for removing files.
- the -r switch is recursive: that is, it removes all files and directories in the specified directory.
- the -f switch stops rm from prompting the user for confirmation before removing write-protected files.
- $HOME is an environment variable representing the directory tree owned by the current user.
- the slash (or forward slash) character / is used in Unix as a path delimiter.
- the * character is used as a wildcard to denote any number of any characters in a filename.
So the command rm -rf $HOME/* means “delete all files in my home directory, including all sub-directories and the files they contain, and if you find a file that’s write-protected, go ahead and delete it without asking me.” While the command sudo rm -rf/* means “pretend I’m a system administrator so that I can delete all files and subdirectories starting from the root directory. (Unix directory trees, for some reason, have a single ‘root’ at the top of the tree. This may seem counter-intuitive but it wasn’t my idea.)
Perhaps the more recent hoax ‘advice’ is potentially more effective, in that it doesn’t require potential victims who don’t realize the destructive potential of the command to find out how to access to esoteric environments such as the OS X terminal application. In any case they probably wouldn’t have risked accessing the /b/ board if they even knew about it. However, it’s clear that destructive hoaxes are likely to be migrated to other channels and services, perhaps with the social engineering tweaked.
Xbox to Xbrick
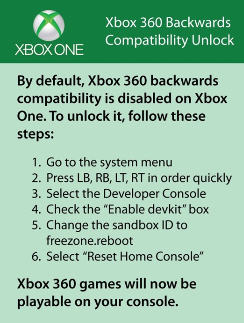
A little earlier on, Microsoft had warned Xbox One users that a ‘tip’ concerning how to turn on ‘Xbox 360 backwards compatibility’ that there was no such compatibility mode, and that following these ‘instructions’ would actually render the Xbox One useless.
However, it’s not these specific hoaxes I’m most concerned with in this article. In fact, this kind of malicious, destructive hoaxing, based on tricking the victim into trashing his own system was around before the World Wide Web in various forms. In this case, the common denominator is – or appears to be – 4chan, and especially its /b/ or ‘Random’ board – a minimally-regulated forum that you can only access if you click to agree that you won’t hold 4chan responsible for any damages resulting from your use of the site.
While the site is most notoriously associated in the media with the unsanctioned release of nude celebrity photographs – which the site has now addressed with a DMCA takedown policy – 4chan’s boards are actually concerned with a wide range of graphical content. There is actually a rich assortment of rules that are meant to govern those boards: however, not all the global rules apply to all boards. Some of them even apply to /b/, but /b/ isn’t – most notably – subject to global rule 3 (which among other things forbids ‘Trolls, flames, racism, off-topic replies, uncalled for catchphrases…’) and the rules and FAQ don’t specifically address hoaxes and destructive ‘advice’ at all, as far as I can see. 4chan founder Christopher Poole has himself described /b/ as “kind of the dark heart of the Internet.” You might describe Poole as the anti-Zuckerberg, being as much in favour of anonymity as Zuckerberg is against it: 4chan does not require registration. As Poole also said, according to that Forbes article:
Anyone can come in to contribute, there are no structural barriers,” said Poole. It’s also ephemeral: “There’s no archive… posts that are created fall off within minutes.”
The Biter Bit
That ephemerality of content also makes it difficult to confirm much of the activity that is attributed to 4chan, and much of its impact in the media comes from its dissemination to other sites. It turns out that this has implications for 4chan that Poole might not altogether welcome. The threatened misogynistic revelation of photographs of Emma Watson in ‘retaliation’ for her feminist speech at the UN, attributed to 4chan, turns out to be not only a hoax. Not only (as expected) in terms of the existence of the photographs, but in terms of the complicity of users of 4chan. In fact, Business Insider describes the story as ‘[not] a marketing stunt at all, but a social experiment run by the most notorious gang of pranksters on the internet’, and it’s not referring to 4chan, or the (apparently fake) Rantic Marketing, but SocialVEVO.
This multilayered hoax, the admission of a DCMA policy, and the occasional hint of a slightly less arbitrary approach to rule enforcement, might all make you feel more comfortable with the way 4chan operates, even /b/, where apparently nurturing and supportive discussions can occasionally happen. No wonder CNN is confused...
But it probably shouldn’t make you feel at all comfortable with the way that the Internet has evolved into an environment where half-truth, rumour and deception often seem more the rule than the exception, to the extent that even dedicated security sceptics can sometimes be taken in and may even feel obliged to eat (some of) their words.
* Profiles of the Future (revised edition, 1973) http://en.wikipedia.org/wiki/Clarke%27s_three_laws
David Harley
ESET Senior Research Fellow