If you have received an unexpected email, claiming to come from British Airways, about an upcoming flight that you haven't booked - please be on your guard.
Online criminals are attempting to infect innocent users' computers with a variant of the malicious Win32/Spy.Zbot.AAU trojan, by disguising their attack as an e-ticket from the airline.
To maximise the potential number of victims, the attackers have spammed out messages widely from compromised computers.
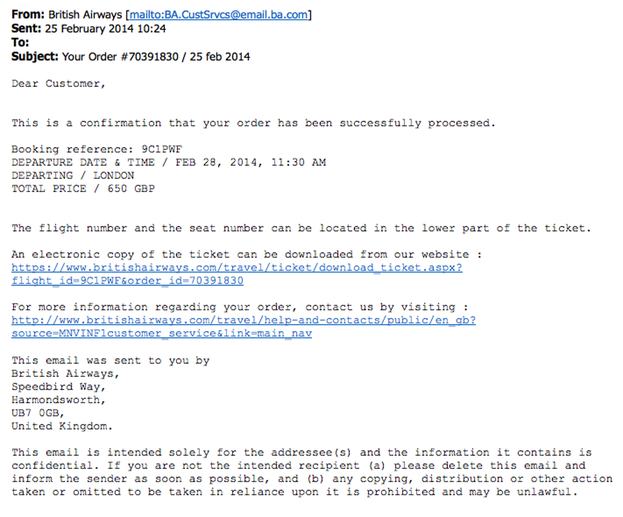
Here's an example of what part of a typical malicious email spread in this spammed-out campaign looks like:
From: British Airways [mailto:BA.CustSrvcs@email.ba.com]
Subject: Your Order #70391830 / 25 feb 2014Dear Customer,
This is a confirmation that your order has been successfully processed.
Booking reference: 9C1PWF
DEPARTURE DATE & TIME / FEB 28, 2014, 11:30 AM
DEPARTING / LONDON
TOTAL PRICE / 650 GBPThe flight number and the seat number can be located in the lower part of the ticket.
An electronic copy of the ticket can be downloaded from our website :
[LINK]For more information regarding your order, contact us by visiting :
[LINK]
Of course, although the email claims to come from British Airways - it is nothing of the sort.
In a classic example of social engineering, criminals are hoping that email recipients will worry that their credit card has been fraudulently used to purchase an air ticket, and click on links inside the email to find out more.
However, if users download the supposed e-ticket and launch its contents, they will be infecting themselves with a trojan horse that can spy on their computer activity and give malicious hackers third-party access to their data.
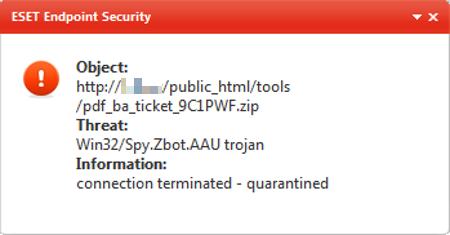
ESET antivirus products detect the malware as a variant of Win32/Spy.Zbot.AAU.
Users of other anti-virus products would be wise to check that their systems are updated, and protected against the threat.
In this case, the malware has been spread via malicious links after cybercriminals forged email headers to make their messages look like they really came from British Airways's customer service department. But it's equally possible for attackers to spread their malware via email attachments, or for other disguises to be deployed if those behind the spam blitz believe that they have a greater chance of success.
Remember to always be suspicious of clicking on links in unsolicited emails, and the social engineering tricks that are frequently used to lure computer users into making unwise decisions.




