Malicious software that gets updates from a domain belonging to the Eurasian state of Georgia? This unusual behavior caught the attention of an analyst in ESET's virus laboratory earlier this year, leading to further analysis which revealed an information stealing trojan being used to target Georgian nationals in particular. After further investigation, ESET researchers were able to gain access to the control panel of the botnet created with this malware, revealing the extent and the intent of this operation.
Finding a new botnet is not unusual these days and most are not particularly interesting from a nerdy, techie point of view, but it turns out that this one (dubbed Win32/Georbot) is both unusual and interesting. Amongst other activities, it will try to steal documents and certificates, can create audio and video recordings and browse the local network for information. One unusual aspect is that it will also look for “Remote Desktop Configuration Files” that enables the people receiving these files to connect to the remote machines without using any exploit. That approach will even bypass the need for RDP exploits such as the one that was revealed last week (MS12-20).
Win32/Georbot features an update mechanism to get new versions of the bot as an attempt to remain undetected by anti-malware scanners. The bot also has a fall-back mechanism in case it can’t reach the C&C (Command and Control) server: in that case it will then connect to a special webpage that was placed on a system hosted by the Georgian government. This does not automatically mean that the Georgian government is involved. Quite often people are not aware their systems are compromised. It should be also noted that the Data Exchange Agency of the Ministry of Justice of Georgia and its national CERT were fully aware of the situation as early as 2011 and, parallel to their own – still ongoing – monitoring, have cooperated with ESET on this matter.
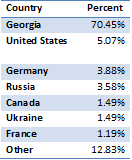 ESET’s researchers were also able to get access to the bot’s control panel which displayed clear details about the number of affected machines, where they are, possible commands, and so on. The most interesting information found on the control panel was a list with all the keywords that were searched for in documents on infected systems (including a lot of three letter agencies like KGB, FSB and CIA).
ESET’s researchers were also able to get access to the bot’s control panel which displayed clear details about the number of affected machines, where they are, possible commands, and so on. The most interesting information found on the control panel was a list with all the keywords that were searched for in documents on infected systems (including a lot of three letter agencies like KGB, FSB and CIA).
Win32/Georbot uses various obfuscation techniques to make static analysis more difficult, but for experienced malware analysts that is not much of a problem to overcome, and Win32/Georbot was well worth the time it took to undertake a detailed analysis. The full white paper containing the detailed analysis can be found here.




