Yesterday the U.S. president, Barak Obama, held a conference at the White House to announce that the leader of Al Qaeda, Osama Bin Laden, was killed in Abbottabad, Pakistan. With no doubt, this is a story with an international impact, which the people will remember in the coming days and... attackers as well. As expected, malicious code began to spread with different social engineering techniques based on this incident and we can also see from our Laboratory in Argentina, that there are a few threats in Latin America related to this news.
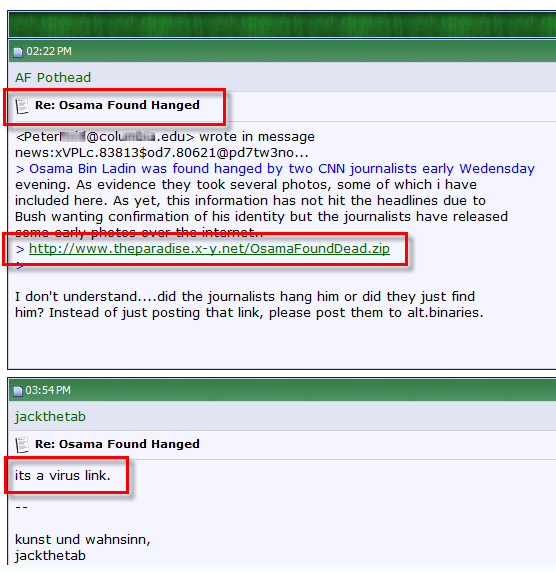
As Randy wrote earlier today, fake videos and Black Hat SEO techniques are being used by attackers to propagate malware, regarding the latest news on Bin Laden's death. These techniques, have been used commonly any time the terrorist was on the news, as we had been detected before on some forums, with alleged pictures of the terrorist's body hanged:
The image link has been disabled and it was a Trojan. As you can see, a forum user tries to alert the other readers, saying the link is malicious. The attackers take clearly advantage of the curiosity of users.
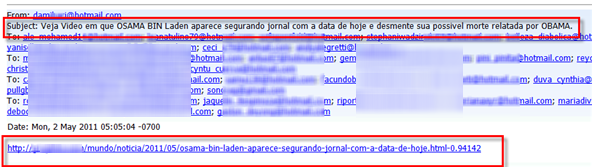
Moreover, early today we are seeing some attacks in Latin America that use the death of Bin Laden as an excuse to spread malware. This time, it is an email in Portuguese, which is entitled (translated into English) "Watch video where Osama bin Laden, is shown holding a newspaper with today date and denies his possible death":
The link, as you can imagine, offers the download of a banking Trojan detected as a probably variant of Win32/TrojanDownloader.Banload.PYR Trojan. If user runs the malicious file, it will modify the host file to redirect some banks web sites to phishing servers, as you can see in the following image:
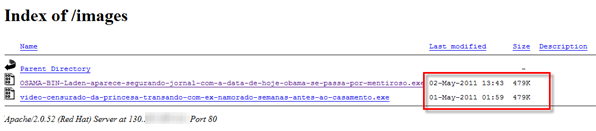
Also, in the analysis of the server where the file is hosted, you can see that from the same folder you can download another file, this time based on the real wedding (an alleged video of the princess with a lover before her marriage):
If you look in detail, note that today was added the second fileand that both files have the same size. By downloading, we found that both files have the same MD5 (9EE8023B94D6186F09857DBDAD14ED09), so, it is the same threat and only the file name was changed.
Different media were also alert about scam attacks using Social Engineering:
- http://www.foxnews.com/scitech/2011/05/02/usama-bin-laden-death-joy-cyberscammers/
- http://www.eweek.com/c/a/Security/Osama-Bin-Ladens-Death-a-Party-for-Spammers-Fake-AV-Scammers-721672/
As Randy told, "Look carefully at your search results and stick to well known sites", also a valid tip for email, social networks and any site where you can find news regarding to Osama Bin Laden. Be careful!
Sebastian Bortnik
Awareness & Research Coordinator
ESET Latin America