When you read about Stuxnet and that it used stolen digital certificates from Realtek and JMicron to sign the worm, you may have wondered what the significance of that is or why they did that. There are actually a couple of factors to consider.
When you try to install certain types of software on Windows Vista or Windows 7 it needs to be digitally signed with a trusted certificate. On Vista there is a warning dialog if the software is not digitally signed or has an untrusted certificate. On Windows 7 the file MUST be properly signed with a trusted certificate.
Now the authors could have obtained a valid certificate themselves, but they would have to buy it and it wouldn’t have the name of a major company on it. By stealing the certificate of a trusted vendor they decrease the chance of their malicious software being detected as quickly.
The digital signature on a file only tells you that the file has not been tampered with or corrupted. If a virus infects a file after it has been digitally signed then it breaks the digital signature and Windows will not run the file. If a file is infected and then digitally signed it means that you have functional malware in a program that has a valid digital signature. This is precisely why Microsoft runs drivers through a huge array of virus scanners before
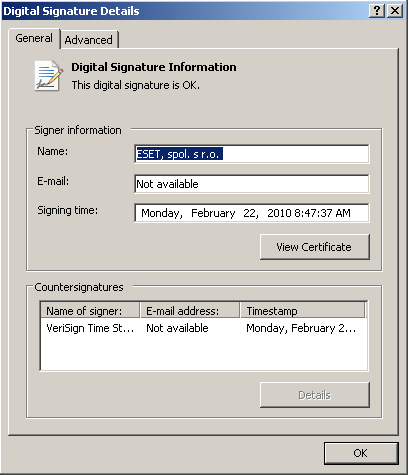
In theory the digital signature also tells you who signed the file, and who issued the digital certificate so you can decide if you trust the person or company who signed the file and if you trust the organization who issued the certificate. In practice if a digital certificate is stolen then you don’t know who really signed the file. If a company is hacked and the attacker gets access to the code signing computer then you don’t know who really signed the file, but it says someone who you likely do trust.
When the creators of the Stuxnet worm signed their driver files with a stolen certificate they made sure that Windows would install the driver without warning and that if someone looked at the certificate they would not be suspicious.
There has been speculation that the certificate may have been stolen by the Zeus malware. The Zeus bot does steal certificates, however because this is associated with banking I suspect they are trying to steal web site certificates, a different kind of digital certificate, so that they can fool web browsers into thinking that their phishing site is a legitimate financial web site. The fact that JMicron and Realtek, the two companies that Stuxnet uses stolen digital certificates from, have offices in the same industrial park in Taiwan raises more suspicion that it may have been an inside job.
Randy Abrams
Director of Technical Education
ESET LLC