Japan has entered its annual tax filing and organizational change season, a period when companies generate a high volume of legitimate financial and HR‑related communications. A threat actor known as Silver Fox is actively exploiting this busy period by conducting a targeted spearphishing campaign against Japanese manufacturers and other businesses.
The ongoing campaign uses convincing phishing lures related to tax compliance violations, salary adjustments, job position changes, and employee stock ownership plans. All emails share the same goal – trick the recipients into opening malicious links or attachments. As employees actually expect to receive emails about these subjects this time of year, they’re more likely to trust and act on such messages without a second thought. Needless to say, this significantly increases the risk of compromise.
The operation is also a reminder for organizations to increase vigilance, reinforce awareness around phishing attempts, and ensure that employees verify the authenticity of tax‑ and HR‑themed requests – including those that look routine. Immediate reporting of suspicious emails to security teams is essential to reduce exposure and prevent successful compromise.
What is the threat?
Active since at least 2023, Silver Fox initially focused on Chinese-speaking targets before expanding into Southeast Asia, Japan, and potentially North America, running each campaign in a local language. This broadened scope shows in the range of verticals the group has hit over the years – finance, healthcare, education, gaming, government and even cybersecurity. The group also primarily operates in Southeast Asia and has a well-documented history of finance-themed spearphishing campaigns during seasonal business cycles.
In the ongoing campaign, the group is taking advantage of Japan’s annual cycle of tax filing, financial reporting, salary adjustments, and personnel changes. This pattern isn’t new – similar activity was observed during the same period last year, indicating that Silver Fox deliberately aligns its operations with this season. The volume and urgency of legitimate internal communication around these topics is high this time of year, which is exactly what Silver Fox is counting on and what makes its campaigns effective.
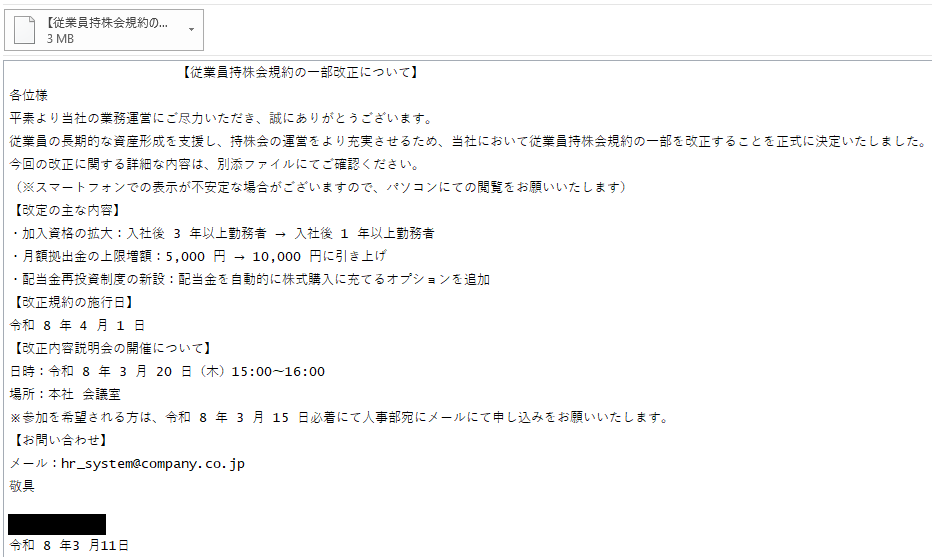
In this operation, Silver Fox sends tailored spearphishing emails crafted to look like legitimate HR or tax-related messages. To make the emails appear authentic, the attackers often include the name of the targeted company directly in the subject line. Examples of subjects observed in this campaign include:
- 「会社名 」【従業員持株会規約改正に関するお知らせ】
(Translation: <Company Name> Notice of amendments to the ESOP terms and conditions]) - 「会社名 」【従業員持株会規約の一部改正について】
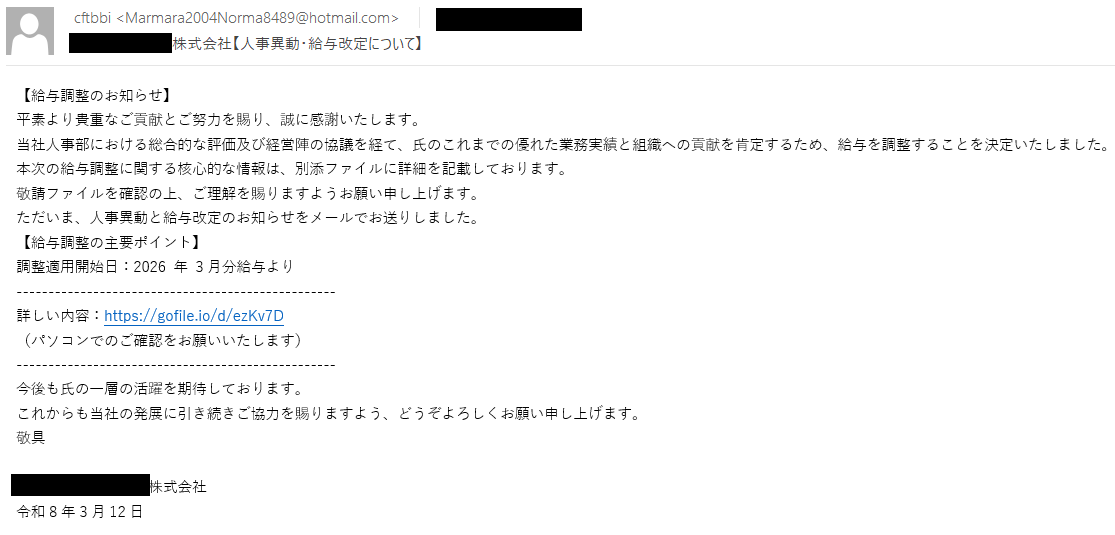
(Translation: <Company Name> [Revisions to the ESOP Terms and Conditions]) - 「会社名 」【人事異動・給与改定について】
(Translation: <Company Name> [Personnel Changes and Salary Adjustments]) - 税務コンプライアンスおよび罰金通知
(Translation: Tax Compliance and Penalty Notice)
The sender fields impersonate real employees and even CEOs at the targeted companies. Silver Fox is clearly doing some reconnaissance on each target before sending what aren’t generic blasts. The attackers are picking names that the targets are likely to recognize and trust, which makes it more difficult for the recipients to distinguish the malicious messages from real internal notifications.
The emails typically contain either a malicious attachment or a link leading to a malicious file. The files are named to resemble common HR, financial, or tax-related documents, such as:
- 【給与調整のお知らせ】
(Translation: Salary Adjustment Notice) - 人事異動・給与改定について
(Translation: Personnel Changes and Salary Adjustments) - 人事異動及び給与改定に関するお知らせ
(Translation: Notice regarding personnel changes and salary adjustments) - 【従業員持株会規約の一部改正について】
(Translation: [Partial amendment to the Employee Stock Ownership Plan terms and conditions])
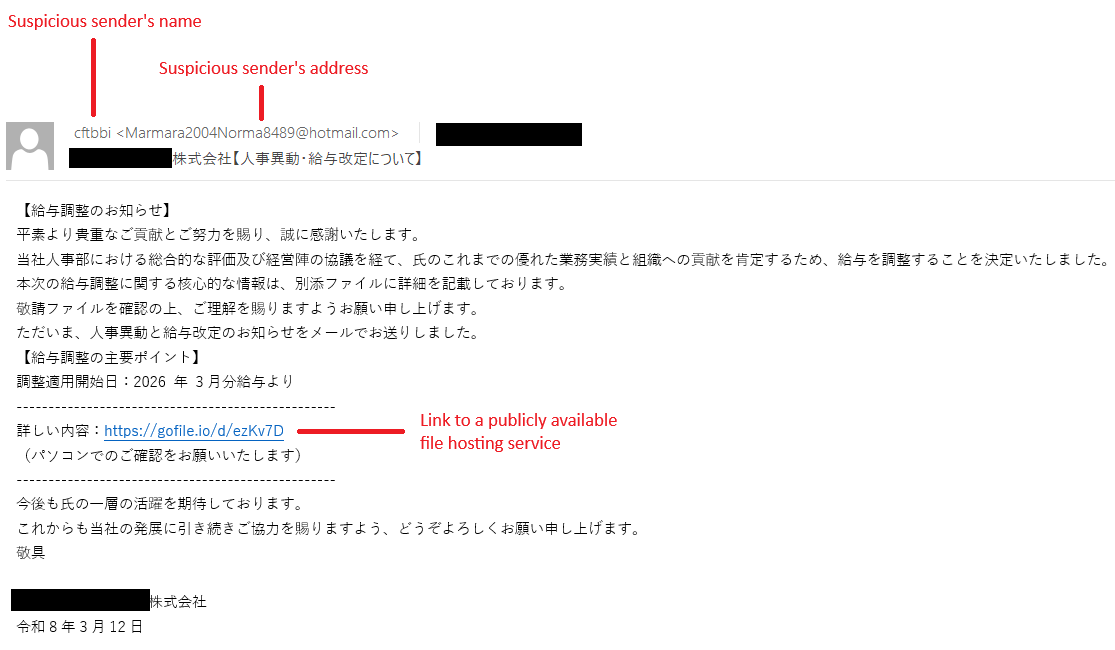
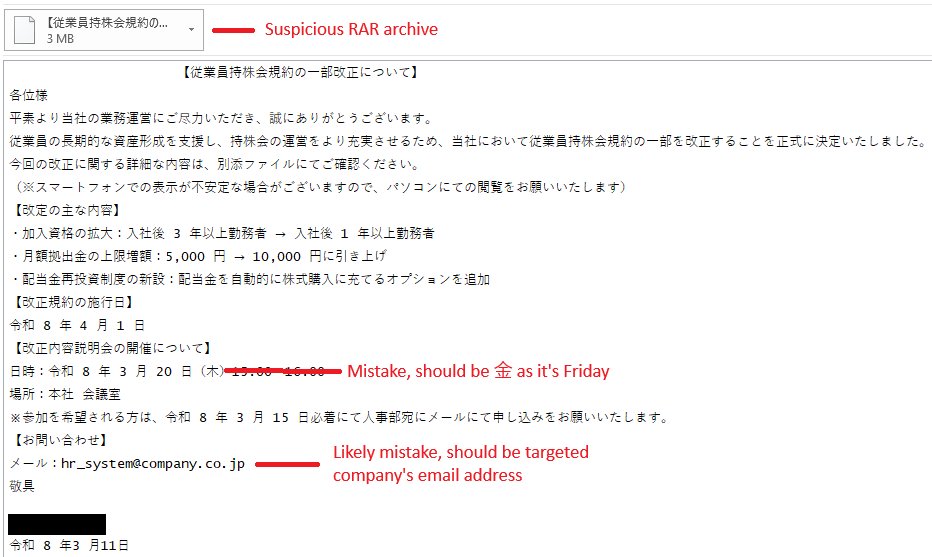
The following are examples of observed emails and lures:
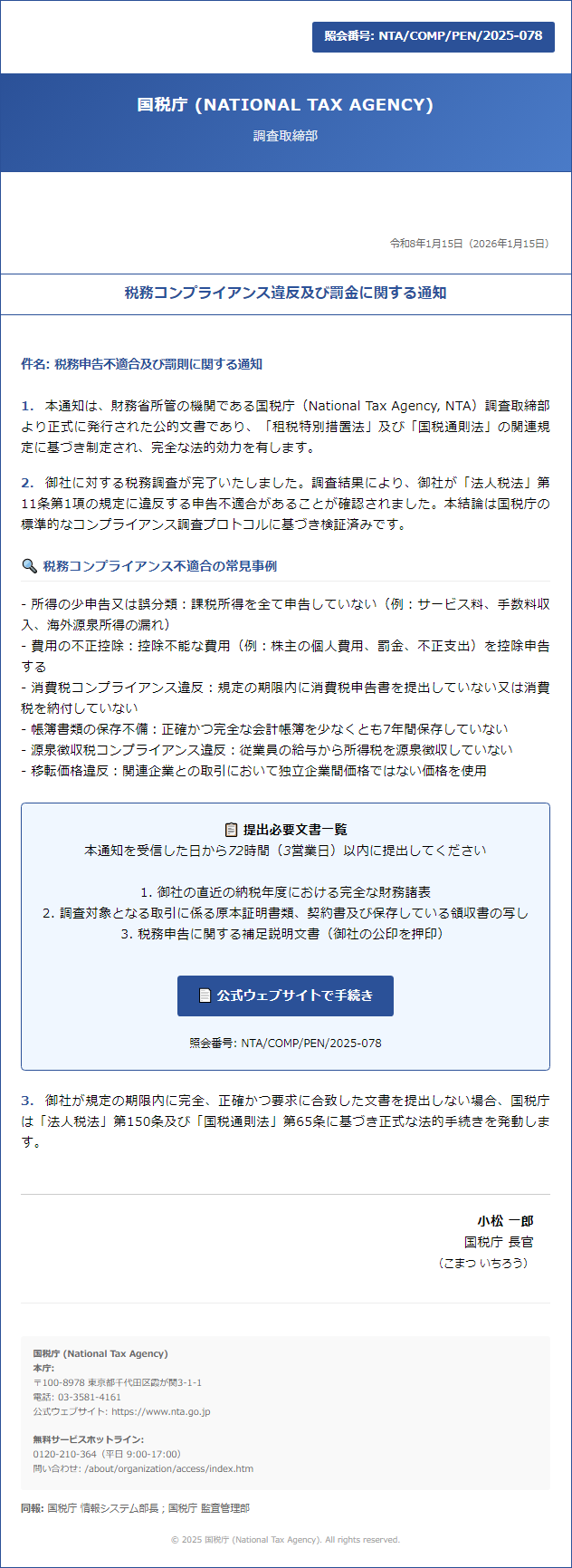
Opening the malicious files drops ValleyRAT, a remote access trojan that Silver Fox has used across multiple campaigns. ESET products detect this malware as Win64/Valley. Once deployed, ValleyRAT enables the actor to take remote control of the compromised machine, harvest sensitive information, monitor user activity, and maintain persistence in the targeted environment. This can allow the attacker to burrow deeper into the network, steal confidential data, or prepare additional stages of an attack.
How to recognize the threat and protect yourself
While Silver Fox’s emails may appear credible at the first glance, especially during Japan’s busy tax and organizational change season, a closer look reveals hints rendering the emails suspicious. The following signs are the key to recognizing and stopping the attack:
- If you receive an email about salary changes, tax penalties, or personnel updates, verify it through a separate channel (Teams, phone, or direct email lookup) before acting on it. This applies even if the message looks routine.
- Even if the sender’s name belongs (or seems to belong) to a colleague, make sure that the email address and the name match. If they don’t or the address looks unfamiliar, treat the email as suspicious.
- Ask yourself whether this communication follows your company’s usual HR or Finance process.
- Be cautious if the language feels overly formal, stiff, or mismatched with typical internal communications. Since the threat actor is not a native Japanese speaker, the emails may contain awkward phrasing and subtle giveaways.
- Documents are unlikely to be shared through a publicly available file hosting services such as gofile[.]io or WeTransfer.
- Pay attention to the attachment type. If it’s an archive such as RAR or ZIP, look at what’s actually inside before opening the files.
- Install software updates when prompted.
- Ensure your security software is running and up-to-date.
- If something feels off about an email, forward it as an attachment to your IT or security team. Reporting is never a mistake – even if the email turns out to be legitimate.
The following are illustrative examples of what to watch out for:
IoCs
A comprehensive list of indicators of compromise (IoCs) and samples can be found in our GitHub repository.