When we relayed the FBI/IC3 warning to travelers about a threat involving hotel Internet service overseas last week it produced a lot of requests for advice on how to respond to the threat. So a few of us researchers at ESET came up with a list of data security tips for travelers. These tips will help you keep your data safe while traveling and should defeat this particular threat (IC3 says a pop-up appears as you are signing in to the hotel Internet and asks you to update perform a software which is actually a malware infection).
 Below the list are some additional strategies and one example of what not to do with your laptop and your car, wherever you happen to be driving. If you have more suggestions we would love to hear them. Please use the Comment section below to share.
Below the list are some additional strategies and one example of what not to do with your laptop and your car, wherever you happen to be driving. If you have more suggestions we would love to hear them. Please use the Comment section below to share.
- Make sure your operating system and antivirus software are updated before you go on the road.
- Backup your data before you head out (and store the backup in a safe place).
- Consider leaving some data behind or move sensitive data from your laptop hard drive to an encrypted USB stick.
- Make sure you have password protection and inactivity timeout engaged on all devices including laptops, tablets, and smartphones.
- If possible, only use reputable hotel Internet service providers (ask the hotel who their provider is before you book).
- If the hotel Internet asks you to update software in order to connect, immediately disconnect and tell the front desk.
- If you use hotel Internet to connect to your company network use a VPN.
- Do not use WiFi connections that are not encrypted with WPA (avoid WEP encrypted connections which are easily hacked).*
- Consider getting a 3G or 4G hotspot and using that instead of hotel Internet.
- Avoid online banking and shopping while on any hotel or public Internet connection.
- Disable pop-ups in your web browser.
Bonus tip #1: If you are on the road and suspect that your Windows laptop has become infected you can get a free online scan from ESET.
Bonus tip #2: Don't assume your laptop is safe from malware when traveling just because it is a Mac. Consider installing a reputable antivirus product, for example, you could install a free 30-day trial of ESET Cybersecurity for Mac OS X before you head out on your travels.
What not to do when on the road with your laptop
 Do not park your car and then place your laptop in the trunk. Place your laptop in the trunk before you reach the place you are going be parking.
Do not park your car and then place your laptop in the trunk. Place your laptop in the trunk before you reach the place you are going be parking.
The reason? Someone who sees you place a computer in the trunk and then walk away from the vehicle knows the car is worth breaking into or stealing. A former colleague learned this the hard way in Venice Beach in 1996, back when a high-end laptop could cost over three grand.
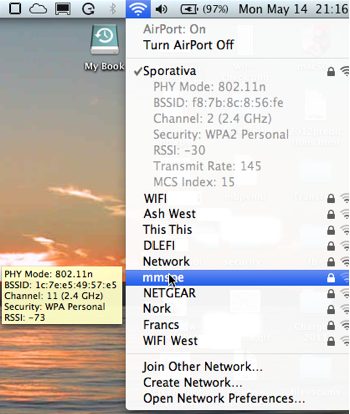
WEP/WPA? How to know which encryption scheme an access point offers
If you are using a Windows 7 laptop you can see the encryption type for any available access point when you display the list of access points from the network icon in the Taskbar (typically lower right of the screen). You may have to hover over the point in the list to see the information.
If you are using a MacBook you can Option-Click the Airport icon for a list that will display the encryption type of your current connection and, on hover, other connections, as shown on the right.
(With many thanks to Aryeh Goretsky and Cameron Camp for their contributions to the tip list.)




