Cybercrime investigators from across the world joined a training exercise recently that had them dealing with a simulated attack launched through an Internet-of-Things (IoT) device.
A total of 43 investigators and experts in digital forensics from 23 countries investigated the would-be attack on a bank. The exercise, called the ‘INTERPOL Digital Security Challenge’, was organized by INTERPOL in Vienna, Austria, and took place over three days in February.
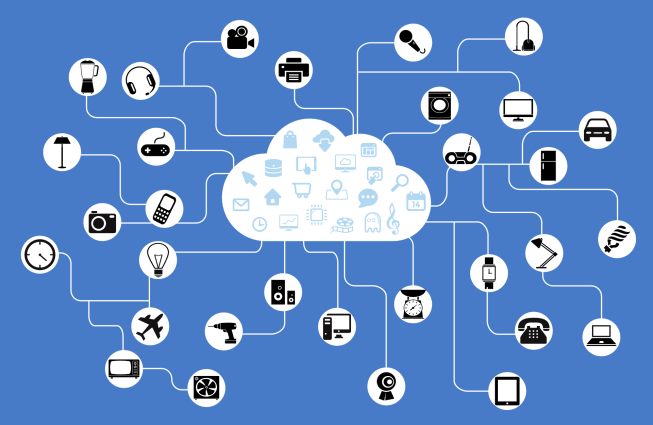
The organization noted that police forces worldwide are often unaware of how to collect forensic evidence from devices other than computers and mobiles. This issue is especially relevant considering the significant cybersecurity risks that the proliferation of vulnerable IoT devices represents.
“Cybercrime investigations are becoming more and more complex and operational exercises such as the Digital Security Challenge, which simulate some of the hurdles that investigators face every day, are vital for the development of our capacities,” Peter Goldgruber, Secretary General of the Austrian Ministry of the Interior, was quoted as saying.
The set-up
In INTERPOL’s scenario, adversaries deployed malware in an attempt to siphon off large amounts of money from the bank.
The investigators applied digital forensics to establish when and where on the bank’s computers the malicious code was installed.
“Through this digital forensic examination, the teams discovered the malware was contained in an e-mail attachment sent via a webcam which had been hacked, and not directly from a computer,” said INTERPOL. The organization added that this “emerging modus operandi” is aimed at helping cover up the source of the attack.
After examining data on the hacked webcam, the investigators identified the command and control (C&C) server that was used for controlling the webcam remotely and for carrying out the attack itself.
The investigators later identified another C&C server, as well as a number of server vulnerabilities that “could be used to prevent further attacks”, said INTERPOL.
The financial sector in general remains a juicy target for cyber-thugs, as shown by recent incidents in Russia and India, and earlier in Bangladesh.
In INTERPOL’s Digital Security Challenge in February 2017, investigators were tasked with tracking down the perpetrator of a ransomware attack.
In the first incarnation of the event in 2016, they had to come to grips with the challenge of identifying, within 52 hours, a blackmailer who demanded a ransom of 10,000 bitcoin on pain of releasing sensitive corporate information.