Normally, the boys in blue at UK police forces do a fantastic job on social media - offering advice to the local community on how to fight crime, and putting a human face on the officers who protect us.
But sometimes things can go wrong.
Take, for instance, this tweet that appeared earlier today on the @EssexPoliceUK Twitter account:
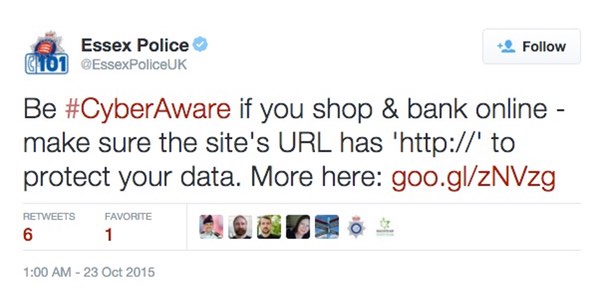
Be #CyberAware if you shop & bank online - make sure that the site's URL has 'http://' to protect your data. More here: [LINK]
At first glance you may think that that's a piece of good advice, and... woah! hang on a minute!
HTTP?
As hopefully you all know, HTTP is inherently insecure - opening up opportunities for criminals, companies and governments to spy on what we're doing, hijack accounts and steal information.
What you actually want to look for is HTTPS, which encrypts communications between your web browser and the website you're trying to access. Hopefully you have noticed the little green padlock in your URL bar when you access sites that need to secure your information, such as your online bank or webmail accounts.
But there's still nothing to stop bad guys from creating websites that use HTTPS - so don't be fooled into believing that it is *proof* that a site is safe to log into.
So, at first I thought Essex Police force had simply made a typo. A pretty silly mistake to make, considering they were trying to raise cybersecurity awareness at the time, but a funny one regardless.
But the mistake I had made was not checking out the link that Essex Police was directing users to.
It transpired that the link, which went through a goo.gl link shortener, didn't take you to sensible computer security advice but instead to a webpage on a site claiming to be related to nursing books.
According to The Guardian, followers who clicked on the link could find themselves viewing an "offensive" picture.
After numerous tweets from people who know the difference between HTTP and HTTPS, Essex Police deleted the offending tweet.
But, perhaps surprisingly, they revealed that it was not the case that someone had made a keyboard fumble and tweeted the wrong link, but that their account had been hacked.
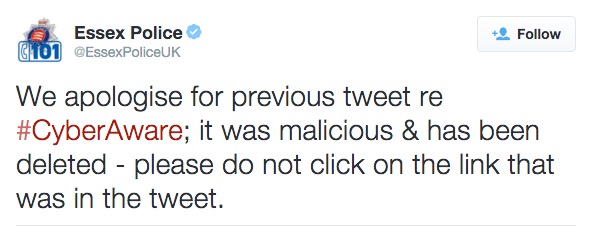
The implication of the tweet is that their Twitter account was hacked.
It's the kind of "It was a hacker what done it" excuse you normally see from rappers after they tweet something highly offensive, but I have to assume that the Essex Police were telling the truth and are now investigating who gained unauthorised access to their account.
Maybe they would be wise to enable Twitter's two-factor authentication (known as Login Verification) to protect their account as well.
Organisations of all sizes need to do more to protect their social media accounts from being hijacked. That's one piece of #CyberAware advice I'm happy to share for free.




