For over 12 hours, some Windows 7 users were left scratching their heads over a bizarre update that was seemingly pushed out by Microsoft.
The update, which purported to be an important language pack, baffled users of Windows 7 as it attempted (and failed) to automatically install itself.
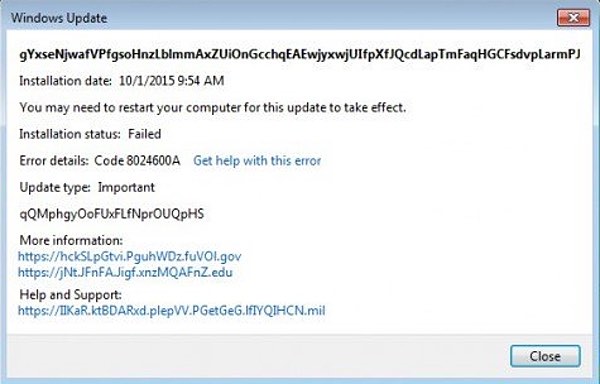
gYxseNjwafVPfgsoHnzLblmmAxZUiOnGcchqEAEwjyxwjUIfpXfJQcdLapTmFaqHGCFsdvpLarmPJLOZYMEILGNIPwNOgEazuBVJcyVjBRL
Installation date: 10/1/2015 9:54 AM
Installation status: Failed
Error details: Code 8024600A
Update type: ImportantqQMphgyOoFUxFLfNprOUQpHS
More information: https://hckSLpGtvi.PguhWDz.fuVOl.gov
https://jNt.JFnFA.Jigf.xnzMQAFnZ.eduHelp and Support: https://IIKaR.ktBDARxd.plepVV.PGetGeG.lfIYQIHCN.mil
No, you're not reading Klingon. That really is what the update said - a bunch of random characters and non-working links.
As Ars Technica reports, the bizarre message resulted in many users suspecting that Windows Update was broken or possibly had been compromised by malicious hackers.
The fear that Windows Update could be subverted to spread malware is a reasonable one - after all, in 2012 security researchers revealed how the Flame worm exploited Microsoft's updating system after generating code-validating certificates seemingly "signed" by the company.
Fortunately, that wasn't the situation in this particular case. Rather than malice, someone at Microsoft had goofed up.
Twelve hours after users started questioning the odd Windows update, Microsoft curtly blamed itself for the errant update in a statement sent to Ars Technica:
"We incorrectly published a test update and are in the process of removing it."
Of course, even if no serious harm was caused by this false update the incident does raise serious questions for Windows users - in particular, Windows 10 home users who are forced to accept security updates, whether they want them or not.
Automatic updates are a good thing - if they work.
But every time Microsoft pushes out a buggy update or suggests that it isn't running Windows Update properly, users' confidence is shaken.




