Earlier this month, Tumblr revealed that it had recently become aware that user addresses and salted and hashed passwords dating back to 2013 had fallen into the hands of hackers.
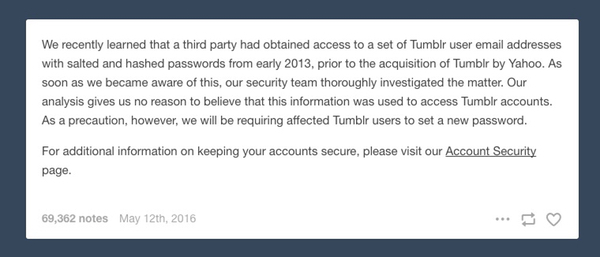
We recently learned that a third party had obtained access to a set of Tumblr user email addresses with salted and hashed passwords from early 2013, prior to the acquisition of Tumblr by Yahoo. As soon as we became aware of this, our security team thoroughly investigated the matter. Our analysis gives us no reason to believe that this information was used to access Tumblr accounts. As a precaution, however, we will be requiring affected Tumblr users to set a new password.
Quite sensibly, Tumblr said it would be asking affected users to choose new passwords.
But there were some things Tumblr didn't say.
For instance, in its brief announcement, didn't say just how many Tumblr users were impacted by the breach.
Furthermore, Tumblr didn't underline the importance of ensuring that the new passwords chosen by Tumblr users should be unique and not used anywhere else on the web. And it didn't remind users that if they were using the same password as their now (potentially compromised) Tumblr password anywhere else on the net, that those would need to be changed too.
Depending on the algorithm used by Tumblr to store salted, hashed passwords it's possible that they didn't think the chances of the passwords themselves being cracked was remote - and that's why they didn't offer the kind of advice you would normally expect if - for instance - they had made the mistake of storing the passwords in plaintext.
But there was something else that Tumblr forgot to warn users about. Even if the password database wasn't likely to be cracked easily by online criminals, the bad guys did now have users' email addresses.
Even without the passwords, attackers could spam Tumblr users using the information, perhaps distributing malware or phishing emails while posing as a genuine communication from Tumblr.
In other words, even if your password isn't cracked as a result of the 2013 data breach, even if you have since changed your password, you still have reasons to be careful.
So, just how many people need to be careful?
I found out last night, when I received a notification email from Troy Hunt's Have I Been Pwned site, warning me that my details had been found in the Tumblr data breach.
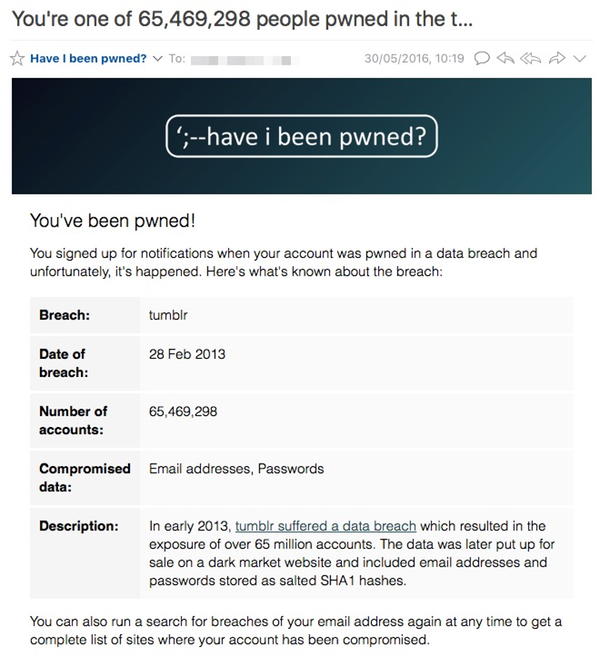
Hunt recently came across a database being sold on the computer underground containing 65,469,298 unique emails and hashed passwords.
As Motherboard reports, the database is being sold by a hacker going by the name of "Peace", for the lowly sum of $150. "Peace" also claims that Tumblr used the SHA1 algorithm to store the passwords, making them extremely hard to crack - and probably explaining the cheap price.
But even if your Tumblr password isn't at much risk of being cracked, you should still probably change it. Just make sure it's changed to something unique, hard to crack and hard to guess. I would also advise enabling two-step verification on your Tumblr account as well.
And don't think that dealing with the password breach means that you can relax. Your email address is now "out there", and criminals know how to contact you and 65 million other Tumblr users.
Always be wary of unsolicited and unexpected emails, and exercise caution over opening attached files and clicking on links.




