Moonpig, the online personalised card company, has blocked the accounts of an unspecified number of customers after users' details were published online.
In an advisory posted on its website, Moonpig explained that it became aware that customers' email addresses, passwords and account balance had been made public.
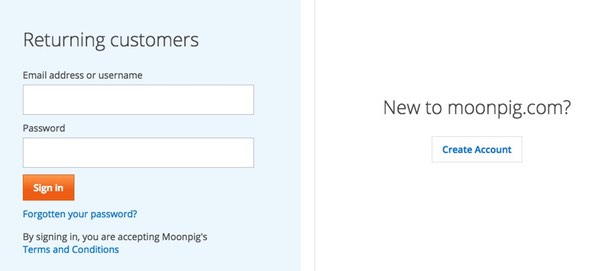
log
However, the firm was quick to stress that it believed the source of the passwords was not directly from its own services, but from other online sites where users had made the mistake of using identical passwords.
"As a precautionary measure, we promptly closed our Moonpig site and apps to help us investigate and contain this issue.""Following these investigations, we now have strong evidence that the customer email addresses and passwords we identified were taken previously from other third party websites, and not directly from Moonpig.com. This data was then used to access the account balances of some of our Moonpig.com customers. As a reminder, we do not store full credit card information ourselves so this data was not accessible in any event."
Moonpig goes on to say that it has contacted affected customers, telling them they will need to reset their passwords the next time they attempt to login, and that they should also ensure that they are not reusing the same passwords anywhere else on the net.
And that's sensible advice. You should never use the same password for different sites, because if one gets hacked and login credentials are stolen then the attacker could use that data to break into your other online accounts.
All this, of course, means that if information from the Moonpig accounts has been published on the net, and includes passwords and email addresses, there's a good chance that online criminals will be attempting to use that same information to break into other sites that may lead to more dangerous scenarios than just unauthorised purchases of personalised birthday cards.
And don't forget - if the passwords came from elsewhere, there's a good chance that passwords from people who *aren't* customers of Moonpig are impacted too.
It's a shame that Moonpig hasn't shared more information about where it believes the passwords may have originated - was it a partner of theirs or completely separate third party sites? It's also disappointing that they give no indication regarding how many accounts may have been exposed - as that would surely have helped people judge the seriousness of the incident.
But at least the company appears to be doing the right thing. Perhaps it's keen to show a good face when it comes to security issues after it was discovered earlier this year that an unpatched security hole had left millions of Moonpig customers at risk for 17 months.
One assumes that this latest security scare is not related to that incident.
All of this comes down to a central problem: most people have no clue about how to use passwords properly on the internet.
One of the golden rules about passwords is not to share them. That doesn't just mean don't tell strangers and your work colleagues your password, it also means that you shouldn't share them between different services and vendors.
You need different passwords for different websites.
Of course, even if you understand that, the next mistake you might make is choosing dumb passwords: passwords that are dictionary words or that are based upon a formula ("moonpigpassword") that is easy to crack.
Strong passwords are not just unique, they're also complex and long, making them a tough nut to crack.
And if like me you think it's impossible to remember dozens of different, complex, gobbledygook passwords then my answer is a simple one. Get yourself a decent password manager that stores your passwords securely, and suggests new ones that are more random and complex than your puny human brain would ever be able to manage.
That way you only have to remember one complex password - the master password that unlocks your password vault.




