Calling all CISOs and CISSPs, all of you CCNAs, GIACs and CEHs: do you need another acronym to remember, along with HIPAA, FISMA, COBIT, GLBA, FERPA and PCI? Probably not! But try this one on for size: OFAC, as in Office of Foreign Assets Control. Let's allow their website to describe what this office does and then I will explain how it relates to cybersecurity:
"The Office of Foreign Assets Control (OFAC) of the U.S. Department of the Treasury administers and enforces economic and trade sanctions based on U.S. foreign policy and national security goals against targeted foreign countries and regimes, terrorists, international narcotics traffickers, those engaged in activities related to the proliferation of weapons of mass destruction, and other threats to the national security, foreign policy or economy of the United States."
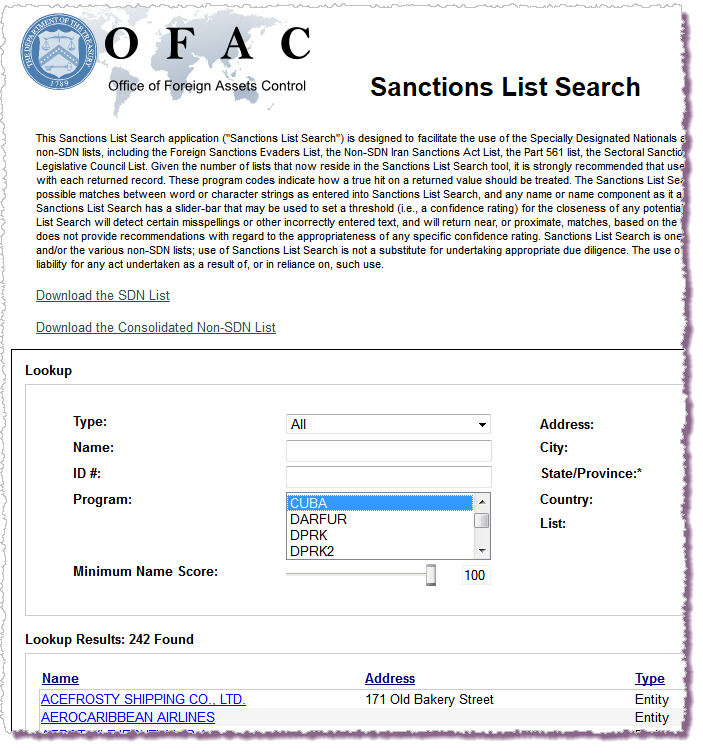
To over-simplify: OFAC is the agency that will list those entities with whom you and your company should not, in the judgment of the U.S. government, be doing business, owing to a variety of sanctions. Examples of sanctions include those applied to Cuba, Darfur, and North Korea, coded on the OFAC website search tool below as CUBA, DARFUR, DPRK, and so on:
We will soon see CYBER appear between CUBA and DARFUR on this list (and we may see CUBA disappear, but that's another story). CYBER is the OFAC code for the new cyber sanctions launched by President Obama earlier this month. The stated goal of these sanctions is to target "individuals and groups outside the United States that use cyber attacks to threaten U.S. foreign policy, national security or economic stability" (Reuters).
In other words, a website hosting company outside the U.S. that turns a blind eye to a website on which data stolen from the U.S. is bought and sold could soon see its name on this list. Consequently, any company that supplies connectivity or even electricity to said hosting firm could then be deemed in violation of U.S. sanctions, for which there may be serious consequences, of which more in a moment. What security professionals need to know is that:
- There is a new weapon in the law enforcement armory that can be used to deter cyber crime
- Some companies may need to develop a new compliance program to ensure they do not violate the terms of these new sanctions.
Malicious cyber activities: an extraordinary threat
These new cyber sanctions were put in place by Executive Order 13694 on April 1, 2015. In that document, President Obama stated that "the increasing prevalence and severity of malicious cyber-enabled activities originating from, or directed by persons located, in whole or in substantial part, outside the United States constitute an unusual and extraordinary threat to the national security, foreign policy, and economy of the United States."
Based on this assessment, which seems fair enough given the activity that we've see occurring over the last few years, the President declared "a national emergency to deal with this threat." The executive order authorizes the U.S. Secretary of the Treasury, in consultation with the Attorney General and the Secretary of State, to slap sanctions on any persons or "entities" that are deemed responsible for, or complicit in, "malicious cyber-enabled activities" that have "the purpose or effect" of the following:
- Harming or significantly compromising the provision of services by entities in a critical infrastructure sector;
- Significantly disrupting the availability of a computer or network or computers; or
- Causing a significant misappropriation of funds or economic resources, trade secrets, personal identifiers or financial information for commercial or competitive advantage or private financial gain.
The authorized sanctions include freezing the assets of, and/or banning travel by, said persons or entities. Here's an example of what can happen. In 2012, Mitsubishi UFJ Financial Group had to pay an $8.6 million fine to OFAC for violating U.S. sanctions against transferring funds to accounts held by citizens of Myanmar, Sudan, Iran, and Cuba (FT). Not only that, the bank was subject to ongoing remedial measures, including "the expansion of compliance personnel, independent monitoring and reporting to regulatory authorities, and the comprehensive revision of all compliance-related policies and procedures".
Numerous OFAC violations and their consequences are listed on this website, including the 2014 case of a car stereo company hit with a penalty of $4 million for allegedly violating the Iranian sanctions (by shipping audio and video equipment to a company "that it knew, or ought to have known" would then send it on to Iran). Apparently, the company's "lack of a compliance program" contributed to "the severity of the fine."
There is more about OFAC sanctions in general in this FAQ. The Resource Center for the Cyber sanctions is being built out here, and you can sign up for Cyber-related Sanctions e-mail updates. The most relevant web page for those security professionals to whom Compliance and Legal turn for advice is this OFAC answer page which specifically addresses the obligations of "U.S. persons, including firms that facilitate or engage in online commerce." According to OFAC, they are "responsible for ensuring that they do not engage in unauthorized transactions or dealings with persons named on any of OFAC’s sanctions lists or operate in jurisdictions targeted by comprehensive sanctions programs."So what should you be doing about this? OFAC says:
"Such persons, including technology companies, should develop a tailored, risk-based compliance program, which may include sanctions list screening or other appropriate measures. An adequate compliance solution will depend on a variety of factors, including the type of business involved, and there is no single compliance program or solution suitable for every circumstance."
The responsible use of cyber sanctions
Clearly, these sanctions are intended to reduce support for, and profit from, a whole bunch of different cyber crimes, even when those crimes are not recognized as such by the countries in which, or from which, they are committed. As suggested earlier, a typical scenario might be using the threat of sanctions to apply pressure on an upstream provider of Internet connectivity to a bullet-proof host that is knowingly facilitating spam, or a black market in stolen data, or the trading of images of child abuse.
Many security professionals, myself included, have long argued for more tools with which to attack the "cybercrime supply chain". Using a "follow the money approach" and thereby changing the risk/reward equation for criminals has proven effective in fighting many different crimes. Frankly, I don't think anyone is happy with the current situation, in which U.S. companies victimized by criminals get hauled over the coals for their failure to secure data while said criminals are raking in money selling said data on the black market, to other criminals who then use it to victimize Americans to whom said data pertains.
Unfortunately, some less attractive sanction enforcement scenarios are easy to imagine if you don't trust the government to make wise use of its powers. Reasons for such lack of trust can be found in legal cases investigated by organizations like EFF, the Electronic Frontier Foundation (EFF). According to the EFF, "creative prosecutors" have too often abused computer crime law to bring criminal charges "that aren't really about hacking a computer, but instead target other behavior prosecutors dislike" (EFF). This is possible, in part, because computer crime is poorly understood by many in congress and the judiciary; but at times we also see an excess of politics and a lack of principled leadership in law enforcement.
When agencies let big political donors push their agendas through politicians and into law enforcement decision-making we all lose. For example, many security professionals would say there were much better uses for the taxpayer money and law enforcement resources that were put into the prosecution of Andrew (weev) Auernheimer and Aaron Swartz. A lot of consumers whose credit cards were compromised in the 2013 Target and 2014 Home Depot breaches would probably agree, given that the perpetrators of those highly profitable crimes have not yet been brought to justice.
So, what are we to do? Do we trust the U.S. government to use these new powers sensibly or dismiss them as a bad joke? The EFF took the latter approach but I can't go along with that (although I generally find myself agreeing with EFF and, in the interests of full disclosure, I should note that I have donated to them in the past). Here's what I think: these are indeed extraordinary times. Unrelenting cybercrime does pose a serious threat to our economy. I think that, if countries like Russia and China choose not to cooperate with U.S. law enforcement in the pursuit and prosecution of cyber criminals, then the U.S. government needs to exercise sanctions of the kind outlined by the President. However, those sanctions should not be used against security researchers, and I hope to heck they are not. Because if they are, then the U.S. government will have squandered the precious trust of its citizens, notably the ones trying to solve a whole host of problems created by the conjunction of digital technology and human weaknesses.