The human brain is a funny old thing, and remarkably smart.
But sometimes it's too smart for its own good.
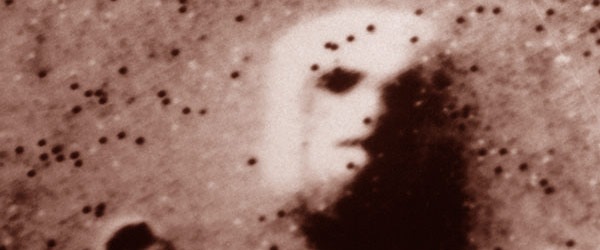
Take, for instance, the infamous "Face on Mars" photographed by the Viking 1 Orbiter in 1976, which lead to rampant speculation and excitable headlines in the media that it must be evidence of intelligent extraterrestrial life.
But was it really an ancient giant statue left by former inhabitants of the Red Planet?
Or was it, in reality, evidence that humans are hardwired to seeing human faces, based upon minimal data, and are prone to seeing faces - in clouds, on the moon, on the surface of Mars - where none really exists? Scientists call this psychological phenomenon pareidolia.
Observations by other spacecraft visiting the Cydonia region of Mars in the decades since have revealed that there is no giant face carved into the rock. Our eyes decided us, and we saw what we wanted to see.
And, perhaps surprisingly, this is relevant to computer security.
Because, just as people can see a face where none is present - so people can be duped by fraudsters and online criminals into believing they are reading one thing when in fact they are not.
Take this URL for instance:
http://www.exɑmple.com
Nothing wrong with that, right?
Wrong.
You see, that's not a link for example.com. It's a URL for exɑmple.com.
 Your mind read "a", when it was actually an "ɑ".
Your mind read "a", when it was actually an "ɑ".
And when it comes to computers there is a world of difference between Unicode character U+0061 (an "a") and U+0251 ("ɑ").
http://www.exɑmple.com and http://www.example.com are going to take you to entirely different places on the internet. And it could mean the difference between you visiting the right website, or visiting one created by cybercriminals to infect your computer with malware or phish your login credentials.
All this talk of extended character sets and the opportunities for abuse is relevant, because last week Google announced support for non-Latin characters in Gmail.
Fortunately, Google is aware that some scoundrels might take the development as an opportunity to make more effective spam campaigns.
As Google describes in a blog post, it's trivial for internet attackers to exploit near-identical looking characters to dupe unsuspecting users into clicking on dangerous links:
Scammers can exploit the fact that ဝ, ૦, and ο look nearly identical to the letter o, and by mixing and matching them, they can hoodwink unsuspecting victims.* Can you imagine the risk of clicking “ShဝppingSite” vs. “ShoppingSite” or “MyBank” vs. “MyBɑnk”?
And it's not just links, of course. I've lost count of the number of times that I've received emails mentioning vιαgяα. I instantly know that the bad guys are referring to the little blue pills that enhance bedroom performance, even though they didn't spell it v.i.a.g.r.a.
Some attempts, naturally, are more sophisticated than others.

The truth is though that they don't always have to fool you, the user.
The first task of any spam campaign is to fool the computer - most of them actually *want* to be human-readable, but they don't want to be easily interpreted by the computer program that is filtering your inbox for spam.
As Google explains, its Gmail service will now be rejecting suspicious letter combinations that could have been deliberately used in spam and phishing attacks:
The Unicode community has identified suspicious combinations of letters that could be misleading, and Gmail will now begin rejecting email with such combinations. We’re using an open standard—the Unicode Consortium’s “Highly Restricted” specification—which we believe strikes a healthy balance between legitimate uses of these new domains and those likely to be abused.
Iτ's gяεατ το sεε Gοοgℓε τακε sτερs το βεττεя ρяοτεςτ τнειя gмαιℓ μsεяs. Iτ ωιℓℓ βε ιητεяεsτιηg το sεε нοω ωεℓℓ ιτ ωοяκs, αηδ ωнετнεя sραммεяs ωιℓℓ ƒιηδ ηεω мετнοδs το gετ τнειя мεssαgεs ιη ƒяοητ οƒ мιℓℓιοηs οƒ ελεβαℓℓs.
Lετs нορε τнατ οτнεя οηℓιηε sεяvιςεs ƒοℓℓοω Gοοgℓε's εχαмρℓε, αηδ ςοηsιδεя ωнατ sτερs τнεy ςαη мακε το βοτн sμρροяτ α мοяε "gℓοβαℓ" ωεβ, αηδ ατ τнε sαмε τιмε ςμяταιℓ τнοsε ωнο τяy το αβμsε ιτ.
Feel free to leave a comment below. You get extra points (sorry, no prizes) if you manage to use some εχτεηδεδ ςнαяαςτεяs in your response that we have to decode.