In the last few weeks there have been numerous stories of online criminals launching attacks against businesses with the aim of extorting money from their victims.
For instance, some 650,000 Domino's Pizza customers in France and Belgium were put at risk after hackers made off with a customer database, and demanded the restaurant paid up a hefty ransom or face having the stolen data made public.
It has also been revealed that mobile phone giant Nokia had, a few years back, found itself in the uncomfortable position of handing over millions of dollars to blackmailing hackers who had stolen encryption codes for the Symbian operating system, and were threatning to post them online.
Unfortunately, a police sting designed to catch Nokia's blackmailers is said to have failed after officers lost track of both the criminals and the cash.
More recently, RSS aggregator Feedly admitted it had been hit by a distributed denial-of-service (DDoS) attack which took its service offline, and announced that it was refusing to pay the ransom demanded by the blackmailing hackers. At the same time it was being reported that Evernote and music service Deezer were also suffering from DDoS attacks against their systems.
Of course, all of these companies have recovered and will - hopefully - be able to parry any future attacks more successfully without disruption or inconvenience to their users.
The same, sadly, can not be said of the latest DDoS extortion victim: Code Spaces.
Code Spaces, a company which provided a similar service to GitHub and describes itself as offering "Rock Solid, Secure and Affordable Svn Hosting, Git Hosting and Project Management" has closed down for ever, after saying it fell victim to DDoS blackmailers this week.
Here is part of the message you will find on the Code Spaces website right now:
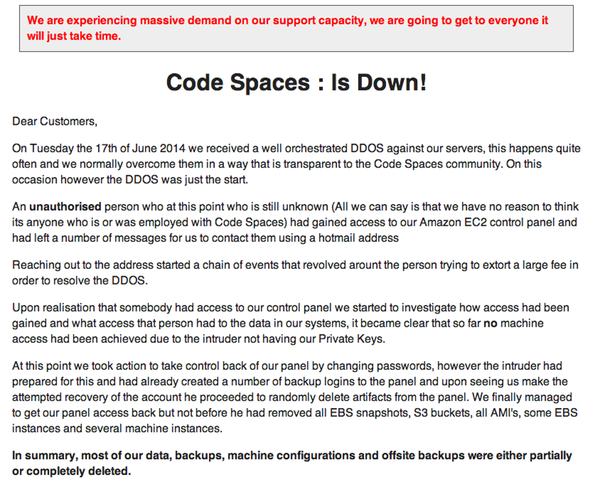
On Tuesday the 17th of June 2014 we received a well orchestrated DDOS against our servers, this happens quite often and we normally overcome them in a way that is transparent to the Code Spaces community. On this occasion however the DDOS was just the start.An unauthorised person who at this point who is still unknown (All we can say is that we have no reason to think its anyone who is or was employed with Code Spaces) had gained access to our Amazon EC2 control panel and had left a number of messages for us to contact them using a hotmail address
Reaching out to the address started a chain of events that revolved arount the person trying to extort a large fee in order to resolve the DDOS.
Upon realisation that somebody had access to our control panel we started to investigate how access had been gained and what access that person had to the data in our systems, it became clear that so far no machine access had been achieved due to the intruder not having our Private Keys.
At this point we took action to take control back of our panel by changing passwords, however the intruder had prepared for this and had already created a number of backup logins to the panel and upon seeing us make the attempted recovery of the account he proceeded to randomly delete artifacts from the panel. We finally managed to get our panel access back but not before he had removed all EBS snapshots, S3 buckets, all AMI's, some EBS instances and several machine instances.
In summary, most of our data, backups, machine configurations and offsite backups were either partially or completely deleted.
Although Code Spaces had made bold claims about its resilience and disaster recovery plans, this was clearly one problem that they were unable to recover from.
All of this, of course, is pretty bad news for Code Spaces' customers.
Code Spaces will not be able to operate beyond this point, the cost of resolving this issue to date and the expected cost of refunding customers who have been left without the service they paid for will put Code Spaces in a irreversible position both financially and in terms of on going credibility.As such at this point in time we have no alternative but to cease trading and concentrate on supporting our affected customers in exporting any remaining data they have left with us.
All that we can say at this point is how sorry we are to both our customers and to the people who make a living at Code Spaces for the chain of events that lead us here.
 It's certainly bad news for Code Spaces to go out of business, and one hopes that the authorities have been involved so they can investigate who might have been behind this malicious hack that forced the company to go kaput.
It's certainly bad news for Code Spaces to go out of business, and one hopes that the authorities have been involved so they can investigate who might have been behind this malicious hack that forced the company to go kaput.
But it should also not be forgotten that there are plenty of Code Spaces' customers who have also been inconvenienced, and might now find themselves in troubled waters because of the disappearance of this service and their code.
Code Spaces customers who wish to recover data they stored with the company are advised to email support@codespaces.com with their account URL. Code Spaces makes no promises, but it says that if it can recover any of your data it will.
The adage that the "cloud is just a different word for somebody else's computer" has never seemed more apt.
There are lots of benefits, of course, to using internet-based services but for goodness sake if you are trusting them with your sensitive or important data make sure that you ask the right questions, get the right assurances and - if necessary - have your own disaster recovery plan in place should things go pear-shaped.




