The critical security vulnerability in OpenSSL known commonly as "Heartbleed" continues to raise alarms, with websites now warning that hackers have breached their systems by exploiting the bug, and stolen personal information about users.
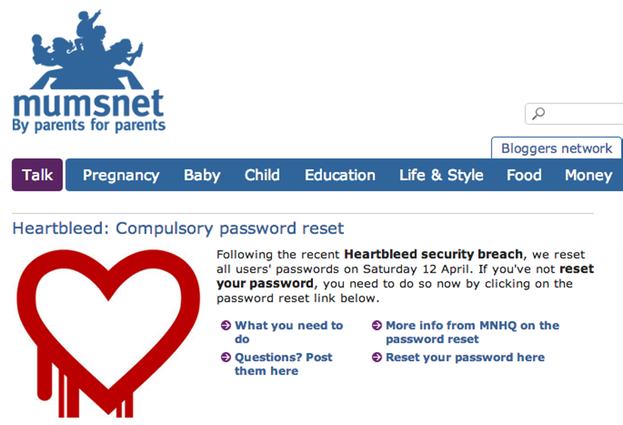
For instance, Mumsnet - a phenomenally popular British parenting website with 1.5 million registered users - has reported that its servers were not only vulnerable, but that users' data had been accessed as a result:
On Friday 11 April, it became apparent that what is widely known as the 'Heartbleed bug' had been used to access data from Mumsnet users' accounts.
Heartbleed is a security hole that existed in OpenSSL, the security framework which most websites around the world use. There's a summary of Heartbleed and its effects here.
On Thursday 10 April we at MNHQ became aware of the bug and immediately ran tests to see if the Mumsnet servers were vulnerable. As soon as it became apparent that we were, we applied the fix to close the OpenSSL security hole (known as the Heartbleed patch). However, it seems that users' data was accessed prior to our applying this fix.
So, over the weekend, we decided we needed to ask all Mumsnet users to change their passwords. So, you will no longer be able to log in to Mumsnet with a password that you chose before 5.45pm on Saturday April 12, 2014.
We have no way of knowing which Mumsnetters were affected by this. The worst case scenario is that the data of every Mumsnet user account was accessed. That's why we've required every user to reset their password.
I must admit I was a little puzzled by the statement. One of the "features" of the Heartbleed bug is that it doesn't leave any clues that systems have been compromised, making it hard for sites to know that they have fallen victim.
However, BBC technology reporter Rory Cellan-Jones got to the bottom of the mystery when interviewing Mumsnet chief executive and founder Justine Roberts about the security scare.
In that report, Roberts says that she became aware that hackers had accessed users' passwords when her own Mumsnet account was used without permission by a hacker, who subsequently posted a message claiming that they had accessed the account after exploiting the Heartbleed OpenSSL flaw.
A smoking gun and convincing evidence that Heartbleed was involved? Perhaps not. After all, perhaps Roberts was phished or had keylogging spyware on a computer that she had used that grabbed her password.
However, Mumsnet was perhaps wise under the circumstances to assume the worst and force members (known as Mumsnetters) to reset any password created on or before Saturday.
And I was pleased to see as well that Mumsnet recommended users change their passwords anywhere else on the net where they might be using the same password.
It's worth everybody realising that you should never use the same password in more than one place - otherwise you could have an account breach on a site which might not be critically important (Mumsnet, for instance) leading to much more serious hacks of your personal information elsewhere.
Meanwhile, in other news from the other side of the great Atlantic pond, the Canadian tax agency has revealed that social insurance numbers of about 900 taxpayers were removed from CRA systems by hackers exploiting the Heartbleed vulnerability.
Regrettably, the CRA has been notified by the Government of Canada's lead security agencies of a malicious breach of taxpayer data that occurred over a six-hour period. Based on our analysis to date, Social Insurance Numbers (SIN) of approximately 900 taxpayers were removed from CRA systems by someone exploiting the Heartbleed vulnerability. We are currently going through the painstaking process of analyzing other fragments of data, some that may relate to businesses, that were also removed.
Again, it's not clear how the Canadian authorities determined that the Heartbleed security hole had been the vehicle for stealing the tax payers' information.
But one thing is obvious. Now it has been publicly proven how easy it is to exploit Heartbleed, we can expect more and more online criminals to try their luck, and see what information they might be able to glean from online companies and websites that have not taken sufficient steps to protect the data on their servers.




