The announcement of Facebook's acquisition of smartphone messaging company WhatsApp for nineteen billion dollars has been the tech news headline of the day. While an analysis of the financial details of this transaction is beyond our remit, ESET's researchers have experience with both mobile security as well as instant messaging, or chat as it's more popularly known these days.
What's up with WhatsApp?
If you are unfamiliar with WhatsApp, do not be alarmed. It is a cross-platform (Android, Apple iOS, Blackberry, Windows Phone and Symbian) instant messaging application that allows you to send text, pictures, video and audio messages to other users of the service. While none of this may be particularly impressive to people who used instant messaging programs like PowWow or AIM in the 1990s, WhatsApp also allows you to share your current location, subject to how well your smartphone is able to determine that, of course.
Also, if you are currently a user of WhatsApp, you may not have used instant messaging back then, since most WhatsApp users were born around that time, according to sources as varied as Forbes, Forrester Research and a report from The Observer, identifying teenagers as the largest demographic for chat apps on mobile platforms as they increasingly turn away from both traditional computers and Facebook, in order to avoid not only their parents and older family members, but also their teachers. So, clearly, Facebook's acquisition has the effect of returning a large number of departed customers back into the fold.
History of poor privacy practices and security problems
One of the main attractions to users of WhatsApp has been claims of its ability to offer secure, private communications between people. However, if that is the case, security and privacy have gotten off to a slow start in WhatsApp.
Aside from its own claims of security and dislike of advertisements, it is difficult to judge the suitability of WhatsApp's end-to-end encryption when their Terms of Service prohibit independent examination by tools commonly used by software developers and security researchers, alike. And even assuming that they are using encryption, it does not matter much if the encryption can be easily broken. Whenever a service provides no information about its encryption, concerns about relying on security through obscurity arise. Claims of secure delivery mechanisms and storage of subscriber data are also likewise difficult to assess. As a related issue, claims about not storing messages after they have been delivered may be impossible to confirm independently, or they may be more natural paranoia from security researchers. It is, however, difficult, if not impossible, to evaluate the risk of eavesdropping and storage elsewhere in an era of National Security Letters and bulk metadata collection, as discussed by Ars Technica here.
The WhatsApp service uses phone numbers for the username portion of its addresses, exactly as user names and domain names are combined to make email addresses. This means that in order to communicate, users are, to all intents and purposes, exchanging phone numbers. While this may be considered a non-issue for phone calls and texting, for which you already have to know the recipient's phone number, instant messaging is a different type of communication, and you may not want to expose your phone number to someone you are chatting with, especially if you do not know them that well. This poor choice for a unique user identifier has caused concern among privacy advocates, and it is not helped by WhatsApp’s behavior of automatically uploading all the phone numbers from customers' address books to its servers in order to build contact lists. A "feature" which cannot be turned off or even selectively enabled or disabled.
WhatsApp has chosen several password algorithms over the years based on information such as an IMEI or a MAC address, which can easily be obtained from a device. WhatsApp did not change these mechanisms for three years and finally did so in 2012.
Through 2011 and 2012, WhatsApp experienced a plethora of security and privacy holes in its instant messaging service, ranging from sending conversations unencrypted (and potentially making them available for anyone to read) to vulnerabilities allowing accounts to be hijacked and messages to be forged. Even as these were repaired, continued problems with cryptography allowed encrypted messages to be deciphered—it should be noted, though, that WhatsApp has fixed issues as they have been reported, and that some vulnerabilities may have required physical access to the smartphone. Once an attacker has physical access to a device, it becomes increasingly difficult to secure.
Governments on at least three continents, including the Dutch Data Protection Authority, the Office of the Privacy Commissioner of Canada and the Communications and Information Technology Commission of the Kingdom of Saudi Arabia have taken notice of WhatsApp and have publicly investigated it because of concerns about the privacy of their citizens. While those are the actions of civilian agencies concerned with privacy and telecommunications, it is not unimaginable that other, more covert intelligence and security agencies have taken notice, too, for the opposite reason. Frankly, it is likely that intelligence agencies around the world have taken advantage of the service’s initial lack of encrypted communications—and the low quality of encryption for subsequent communications—for monitoring everything from terroristic threats and dissidents to communications from journalists, conversations between attorneys and clients and perhaps even eavesdropping on foreign governments participating in trade or other delicate negotiations.
A barrel of phish, dripping with malware
Despite past concerns about privacy and security violations, WhatsApp's usage has continued to skyrocket, growing from nothing in 2009 to having 430 million active users by January 2014. That kind of success has not gone unnoticed, either by Wall Street and Facebook, or by criminals also seeking to capitalize on WhatsApp's success, but for malicious reasons.
There is at least one hoax being sent by email between WhatsApp users, according to computer security analyst Graham Cluley, which claims that WhatsApp will start charging them for messages sent via the service unless they forward the message to ten of their friends. Hoaxes of this kind are old, and benign when compared to malware, but the tricksters who are create and perpetuate them are responsible for clogging up your inbox with junk email.
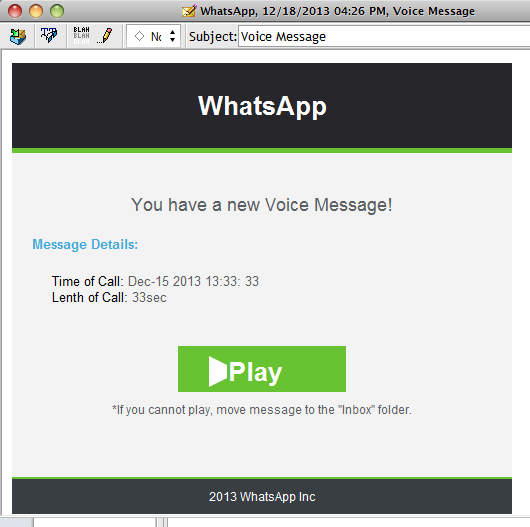
On a more malicious note, below is a screenshot captured by ESET Senior Security Researcher Stephen Cobb on a personal computer, purporting to be a voice mail left for him on WhatsApp, and urging him to click on it to listen to the message in his web browser. Had he visited the web site, his credentials could have been stolen and his computer possibly hijacked, as well. While Stephen—like our readers—knows not to click on suspicious emails (especially when claiming to be from services to which they are not subscribed), such phishing attempts are commonplace and, unfortunately, all too often successful.
This, of course, is just one example of a phishing campaign targeting users of WhatsApp. There have also been numerous campaigns designed to deliver various forms of malware as well, according to multiple reports from Jeff Goldman of eSecurity Planet , Hoax Slayer, Softpedia, The Inquirer and Help Net Security. The malware included—but was certainly not limited to— Win32/Inject.NHN, MSIL/Bladabindi.O, numerous variants from the Win32/TrojanDownloader.Banload and Win32/Spy.Bancos families, and even malware from the ZBot and the Delf family of trojan horses. ESET detects all of these threats, and in some cases, has done so for years. This widespread use of so many different families of malware is not the result of one criminal gang, but rather an example of how numerous organized criminal groups have responded en masse to the rising ubiquitous of WhatsApp.
Fear of a dystopian future: Will WhatsApp offer up your privacy to Facebook?
Jan Koum, the CEO and cofounder of WhatsApp, has stated in a post on his company's blog that nothing will change for its users, however, it is hard to imagine any program or service for which the user experience does not change over time, especially after such an acquisition.
Perhaps the closest parallel is Skype. Founded in 2003, the company was acquired by eBay in 2005 and subsequently acquired by Microsoft in 2011. After Microsoft's acquisition, numerous changes were made (reported by Ars Technica here), ranging from replacing the P2P infrastructure of public supernodes on which the service runs with a cluster of Linux-based servers run by Microsoft, to integrating logins with Microsoft accounts (formerly known as Microsoft Passport and Windows Live ID). Microsoft also shares with the public some of the information about how law enforcement requests for Skype's users are handled.
Facebook is already notorious for the erosion of its user's privacy, constantly changing—and, in some cases, removing—privacy controls in order to generate greater revenue by selling ever-increasing details of their customers to advertisers (as reported by Electronic Privacy Information Center, the New York Times, Matt McKeon and The Washington Post here). And the assimilation of WhatsApp into Facebook's empire represents an unprecedented opportunity to learn more about people's daily lives—all with the purpose of targeting them with more and more detailed advertising.
Imagine letting your spouse know you are pregnant over WhatsApp, only to find that the next time you log in to Facebook you are presented with advertisements for baby furniture, diapers and college savings plans. If you think this scenario is far-fetched, remember this is how webmail providers like Google's Gmail service have been data-mining your emails for several years in order to display advertising relevant to whatever is being discussed in each message (as described by Google itself here).
Conclusion
Facebook's acquisition of WhatsApp represents a boon to that small company, rewarding not just dozens of employees for their hard work, dedication and perseverance but their customers as well, who chose to trust the company by using their instant messaging software. Trust, however, is not immutable and can be damaged, even lost, when the relationship between a company and its customers is abused. Facebook is known for playing fast and loose with the privacy of its users (who are, after all, not its customers; Facebook's customers are advertising agencies). It remains to be seen if Facebook's acquisition of WhatsApp will allow the service to continue to grow, or whether its users will flee from the combined grasp of Facebook and WhatsApp in favor of companies that offer more secure and private instant messaging.
We would be remiss if we did not point out that many of the issues ESET has explored are potential concerns based on what might happen in the future. Or, in other words: Don't panic. If you are using the WhatsApp or Facebook apps on your smartphone right now, there's no need to uninstall either program because of concerns about privacy in the future. However, it would be a good idea for you to review their settings as well as terms of use and privacy policies now as well as any time after each app updates to a newer version.
The author would like to thank his colleagues Bruce Burrell, Graham Cluley, Stephen Cobb, David Harley, Lysa Myers and Thomas Uhlemann for their research and contributions to this article.
Aryeh Goretsky, MVP, ZCSE
Distinguished Researcher
References and further reading
Jauregui, Paul. "What's up with WhatsApp's Security?" Praetorian. http://www.praetorian.com/blog/whats-up-with-whatsapps-security-facebook-ssl-vulnerabilities.
Levine, Yasha. "The problem with WhatsApp's privacy boasts: They're not true." PandoDaily. http://pando.com/2014/02/21/the-problem-with-whatsapps-privacy-boasts-theyre-not-true/.
Kurtz, Andreas. "Shooting the Messenger." http://www.andreas-kurtz.de/2011/09/shooting-messenger.html.
Page, Carly. "Facebook's Whatsapp buy is a privacy nightmare for users, but it makes sense for the social network." The Inquirer. http://www.theinquirer.net/inquirer/opinion/2329985/facebooks-whatsapp-buyout-is-a-privacy-nightmare-for-users-but-it-makes-sense-for-the-social-network.
Saudi Gazette. "CITC warns Skype, Viber, WhatsApp." http://www.saudigazette.com.sa/index.cfm?method=home.regcon&contentid=20130401159359.
Wikipedia. "WhatsApp." https://en.wikipedia.org/wiki/WhatsApp.
Williams, Martyn. "WhatsApp could face prosecution on poor privacy." CSO Online. http://www.csoonline.com/article/727756/whatsapp-could-face-prosecution-on-poor-privacy.




