The devastating breach suffered by Adobe earlier this year threw one fact into sharp relief - most of us hate passwords, and a lot of us are really, really lazy.
The two million people who had chosen “123456” as their Adobe password were widely mocked online - but most of us reuse passwords, which is also a serious security sin. Remembering dozens of different, complex passwords is not possible for most people.
Four out of five people admit to having been ‘locked out’ of at least one site they use, because they’ve forgotten theirs, according to a survey of 1,000 people by Ping Internet.
The truly extraordinary thing, though, is that all the effort of memorising dozens of complex passwords is often pointless. Cybercriminals who have stolen a huge “dump” of encrypted data - such as the 38 million passwords taken from Adobe - will crack them all in the end - no matter how good yours is. All you are doing with a strong password is buying time.
ESET Senior Research Fellow David Harley says, in a We Live Security guide to creating stronger passwords: “You can increase the time it takes to crack a password. Length is helpful. But the guessability of a passphrase can be overestimated. It works up to a point.”
Password-cracking apps such as Hashcat can crunch 56-character passwords of extreme complexity - as reported by We Live Security here, and researchers have made programs that cracked these tongue-twisters: “thereisnofatebutwhatwemake” and HP Lovecraft’s famous gibberish, “Ph’nglui mglw’nafh Cthulhu R’lyeh wgah’nagl fhtagn1”.
A long-standing problem with any visual password system is that some can be fooled by photographs - hence Gooogle patented a new facial password system, where users could unlock phones using facial expressions - with users required to stick tongues out or frown at the camera instead of typing a password, as reported by We Live Security here.
The system would prompt users to perform actions such as a frown, sticking a tongue out, smiling with an open mouth or moving an eyebrow. It would then compare the position of a “facial landmark” in frames taken from a video stream to come up with a “liveness score”,
Google’s patent suggests that the system could be augmented with other technologies, such as a “3D rangefinder” and “technologies such as lasers to determine distances to remote objects, depth of remote objects.”
Wearing an electronics-laced hat as a car key might seem surreal - but according to researchers at Tottori University, the device could provide near-unbreakable security, and even prevent carjackings, unlicensed drivers taking the wheel, or accidents caused by drunk driving.
But for certain systems, authentication methods such as iris scanners and fingerprint recognition are insufficient, the researchers argue in a We Live Security report here.
Fingerprint and iris systems are “one time entry” authentication, Isao Nakanishi of the Graduate School of Engineeringargues - and for vehicles carrying valuable commodities or even public transport vehicles, this may not be sufficient.
“Measuring the driver's brain waves continually - via sensors in the headgear of the driver's headgear - would be straightforward and would allow authentication that could not be spoofed by an imposter,” the researchers write. “If the wrong brain waves are measured, the vehicle is safely immobilized.”
The system would scan the alpha-beta brain waves of the driver as they drove, to enture that they were in a fit condition to do so: “ Importantly, the ongoing authentication of drivers using their brain waves would facilitate a simple way to preclude starting the engine if the driver is intoxicated with drugs or alcohol, or even just too tired because their brain waves would not match their normal pattern under such circumstances,” the researchers write.
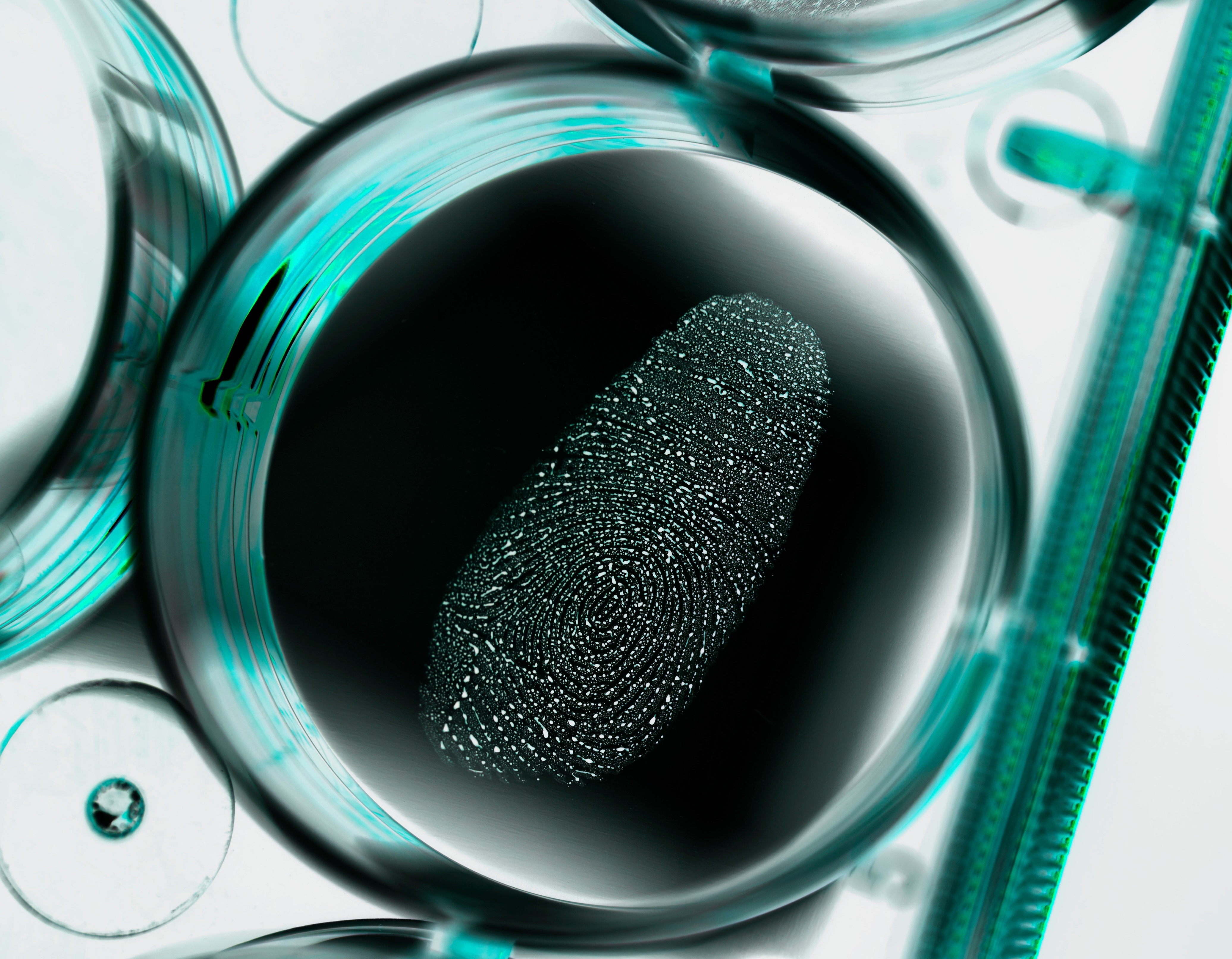 The super-fingerprint scanner which can't be fooled by dead digits
The super-fingerprint scanner which can't be fooled by dead digits
“This is the single biggest advance in identification technology since the creation of the internet,” says Klaus Zwart, CEO of Biocryptology, modestly. It's a new company which combines advanced biometrics with encrypted data stored online, so that for instance, a bank could use fingers instead of cards to identify customers at bank machines - or immigration could use prints instead of passwords, as reported by We Live Security here.
It also uses an advanced sensor which senses oxygen in the blood via ultraviolet, checking the user is alive - so it can’t be fooled with a severed finger, or a fake, its makers claim.
Because the information (the fingerprint) is encrypted and stored online, it can be transmitted safely to multiple devices - without offering cybercriminals the opportunity to hack into a database and print out fakes.
“Biocryptology also uses a UV sensor, infrared sensor and temperature sensors to look for blood flow, body temperature and pH to ensure that not only does the finger 'look' right, but that it is also a live finger - not a dead or a silicone replica finger,” the company says.
“A fingerprint on its own is meaningless. If it cannot be verified as also belonging to the actual live person it is meant to belong to then it is no more secure than a password or a pin number that can be stolen and used illegally.”
Zwart expects his scanners to replace ATM cards, passports, and government ID - and suggested that it might eliminate fraud entirely. Zwart says, “Biocryptology is a impenetrable technology - it goes beyond any security solution that exists today.”
 IBM’s Digital Guardian - ‘Steve’
IBM’s Digital Guardian - ‘Steve’
Machine learning could offer a new line of defense for users, IBM believes - with a ‘digital guardian’ which watches behavior, looking for “deviations” which could mean stolen identity.
It’s not an out-there idea - Google’s Now software, built into Android, stores a vast amount of information to ‘predict’ user wishes. ‘Steve’ is merely a security-conscious version - with IBM giving the example of ‘Steve’ shutting down a device when a vegetarian ordered a hotdog. Other researchers have found that the pattern of a user on a keyboard and mouse can “fingerprint” them accurately, with Iowa State researchers achieving false acceptance and rejection rates of just 0.5% as reported by We Live Security here.
“Today, IBM scientists are using machine learning technologies to understand the behaviors of mobile devices on a network in order to assess potential risk. Security will assimilate contextual, situational and historical data to verify a person’s identity on different devices. By learning about users, a digital guardian can make inferences about what’s normal or reasonable activity and what’s not, acting as an advisor when they want it to.
 The ID card you CAN'T share with a friend
The ID card you CAN'T share with a friend
Most of us are used to carrying ID cards - but one start-up, BluStor, aims to give them a serious upgrade, and “eliminate hacking and identity theft” and perhaps even save lives.
The cards store your voiceprints, fingerprints and iris readings in near-unbreakable encrypted form, then connect to an app via Bluetooth, which then randomly scans voiceprints, fingerprints and iris readings , so an app can confirm a user’s identification instantly.
The card stores biometric details for users, and connects to BluStor’s Secure Mobile Briefcase app, which checks fingerprints, iris scans or voiceprints against the ones stored on the card, as reported by We Live Security here.
“That input is compared with the user's biometric files stored on the BluStor card. If the offered biometric does not match the stored file, the SMB remains locked,” the company says. The app can be used to lock devices entirely, or to lock sensitive data.
The card connects to nearby devices via Bluetooth 4.0, and stores up to 8GB of data - the U.S. government has already expressed interest in using the cards for storing medical data, and a Middle Eastern country for national ID.
BluStor also sugggests that the cards could be used for remote employee authentication - allowing home workers to access sensitive data freely. The cards also have room for file storage for email, medical records or work files.
The high-capacity cards allow the biometric details of a user to be stored in full on the card, and are encrypted with high-grade AES encryption. BluStor claims it is “virtually impossible for a hacker to gain access to a user's device.”
Perhaps the craziest idea of all was demonstrated by an employee of Motorola, Regina Dugan, who leads special projects for the Google-owned company. Dugan used to work for DARPA, the ‘research’ wing of the American military once rumoured to have seriously researched building a time machine - and which developed an early version of the internet. Dugan showed off a password tattoo on her arm, as well as a password pill - which she said is entirely safe, and already certified by the FDA.
Dugan's tattoo is made by company MC10, and was shown off on her own arm at D11, the All Things Digital conference earlier this year. Motorola said it planned to work with the company on authentication systems for future smartphones, as reported by We Live Security here.
"Authentication is so annoying that only about half the people do it,” says Dugan. “Despite the fact that it is a lot of data on your smartphone that makes you far more prone to identity theft. We are thinking about a whole variety of things to make that better. "
The password pill - reportedly already certified by the FDA - is powered by a chemical reaction with stomach acid, and produces a machine-readable 18-bit signal which can be used for authentication.
"I take a vitamin every day, why can't I take a vitamin authentication every day?" asked Dugan."Your entire body becomes an authentication token. It becomes your first superpower. When I touch my phone, my computer, my door, my car I am authenticated.”
"This isn't stuff that is going to ship anytime soon, but we have demoed it working. We are trying to think big again," said Motorola CEO Dennis Woodside.







