Trojans that encrypt user files and try to extort a ransom from the victim in exchange for a decryptor utility are nothing new: in fact, they have been around for several years. These “Filecoders”, as we call them, are a prevalent category of ransomware, the other common type of ransomware being lockscreen scareware – ransomware that locks your desktop, displays a message designed to look as it comes from local law-enforcement and, again demands a payment in order to regain access to your computer.
The reason why we’re bringing up this old issue is that we’ve noted a significant increase in Filecoder activity over the past few summer months and in this blog post we hope to address the many questions we’re getting about this issue.
ESET detections of this malware category are usually flagged as Win32/Filecoder, Win32/Gpcode or in some cases other family names.
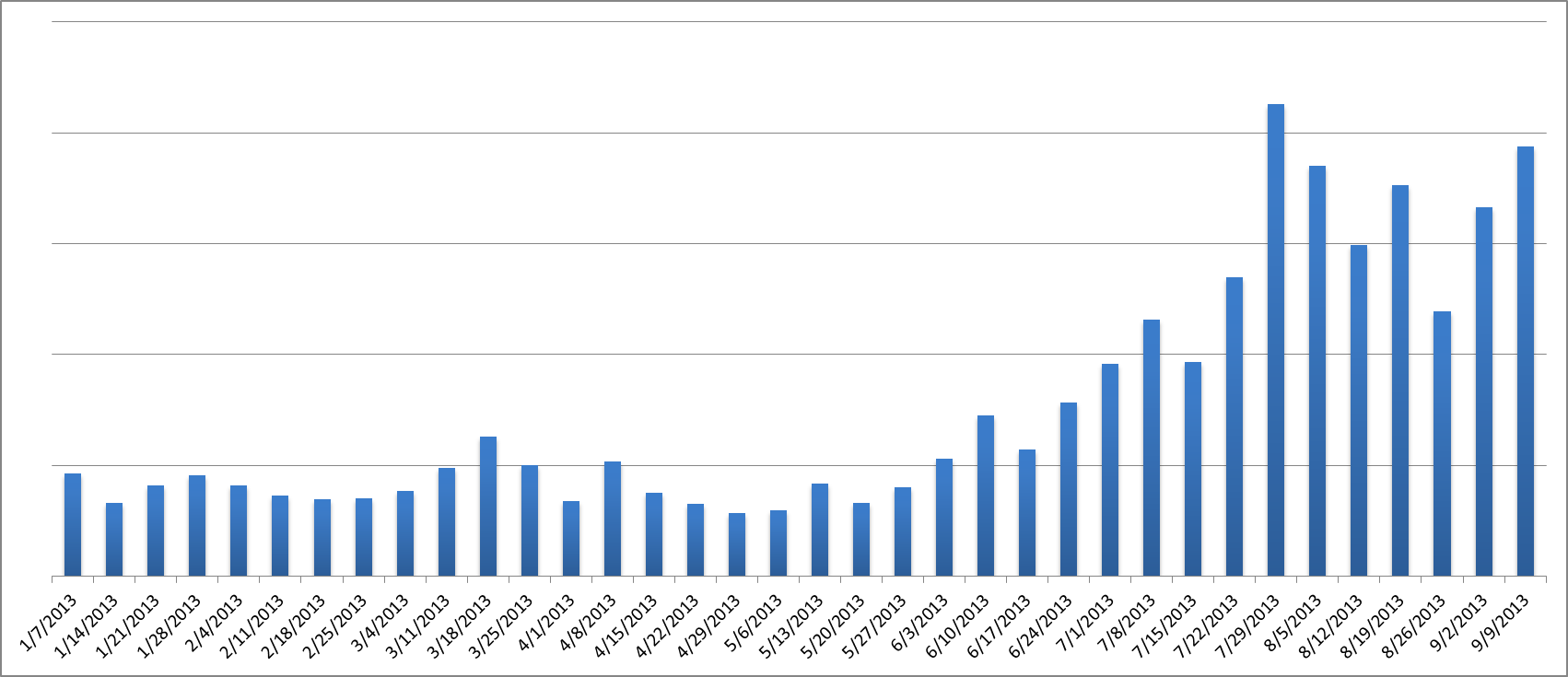
Statistics
ESET LiveGrid® telemetry shows us that the weekly number of Win32/Filecoder detections have risen by over 200% since July 2013 from the average numbers in January through June 2013.
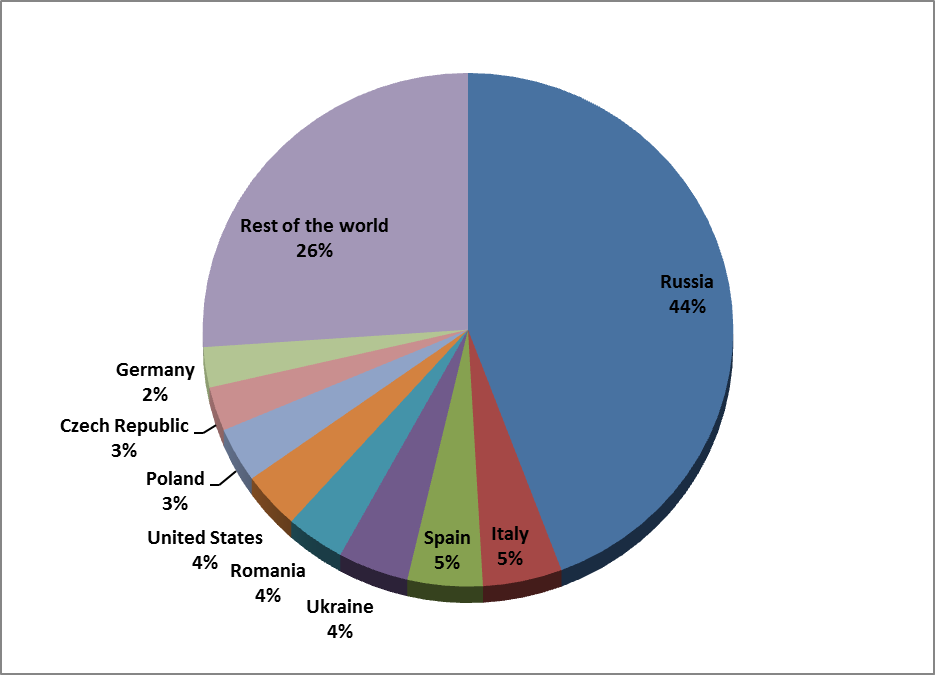
The country most affected by these malware families is Russia, but spreading campaigns are active around different parts of the world:
Infection Vectors
As is the case with other trojan families, cybercriminals using the Filecoder ransomware have a number of different methods of getting the malware onto victims' system:
-
Through drive-by downloads from malware-laden websites
-
Through e-mail attachments
-
Installation by another trojan-downloader or backdoor (see 1st example scenario below)
-
Manual installation by the attacker through RDP infiltration (see 2nd example scenario below)
-
Other common infection vectors
In one infection scenario, we have seen Win32/Filecoder.Q (and later also Win32/Filecoder.AA and Win32/Filecoder.W) spread through backdoors, such as the Poison-Ivy R.A.T. In this scenario, the victims were sent the Poison-Ivy backdoor through email and if they were duped into executing the malware, it would contact a C&C server and wait for commands. The attacker would then send the Filecoder trojan to the infected machine, which would not be saved as a file to the hard drive, but run only in memory.
We have also seen different cases, when the attacker managed to install Filecoder ransomware onto the system manually through compromised Remote Desktop Protocol (RDP) credentials. We don’t have enough information as to how the “break in” occurred – exposed RDP ports, an existing infection with a keylogger, or bruteforcing a weak password are just some possible explanations. What’s important, though, is that in such a case the attacker can gain full access to the targeted machine just as if he was sitting behind the desk, disabling any antivirus protection and doing whatever they please, including installing malware.
In some of these cases, manual installation is also needed due to the fact that some variants require some “user interaction”, e.g. setting the encryption password.
Encryption Techniques
As mentioned in the introduction, this type of ransomware is more “dangerous” than the widespread ‘police’-ransomware category, as it also encrypts the victim’s files – usually pictures, documents, music and archives. A wide range of techniques and levels of sophistication has been seen in different variants over time:
-
The encryption can be implemented in the trojan code, or by using (legitimate) 3rd party tools (e.g. LockDir, WinRAR password-protected archives, etc.)
-
Some variants encrypt the whole file, others only parts of it (for example when slower RSA is used)
-
Various methods have been used to dispose of the original file: in some cases, the clean file is deleted and could be recovered by using “undelete” recovery tools, other times the file was deleted securely (e.g., by using Microsoft SysInternals SDelete) or simply overwritten
Different encryption methods are used:
…and also the encryption keys can be:
-
Hard coded in the binary
-
Entered manually (by command-line or through a dialog box, when the attacker has RDP access to the infected machine)
-
Randomly generated (using various random-functions) and sent to the attacker
Some active examples
A Filecoder family that has been spreading via RDP and has noticeably improved its tactics over time also uses scareware tricks and introduces itself as an “Anti-Child Porn Spam Protection” message or as being from the “ACCDFISA” (“Anti Cyber Crime Department of Federal Internet Security Agency”) – no such agency exists, of course. A comprehensive write-up of different versions can be found on Emsisoft’s blog. Although this particular variant, detected by ESET as Win32/Filecoder.NAC, has been around for quite a while, it is still active in the wild.
This trojan also stands out because of the amount of money it asks for. While other samples in this malware category usually request sums around 100 – 200€, Win32/Filecoder.NAC has been seen extorting up to 3000€. The high amount is consistent with the fact that the attacker usually targets businesses that can usually afford to pay higher ransoms than individuals.
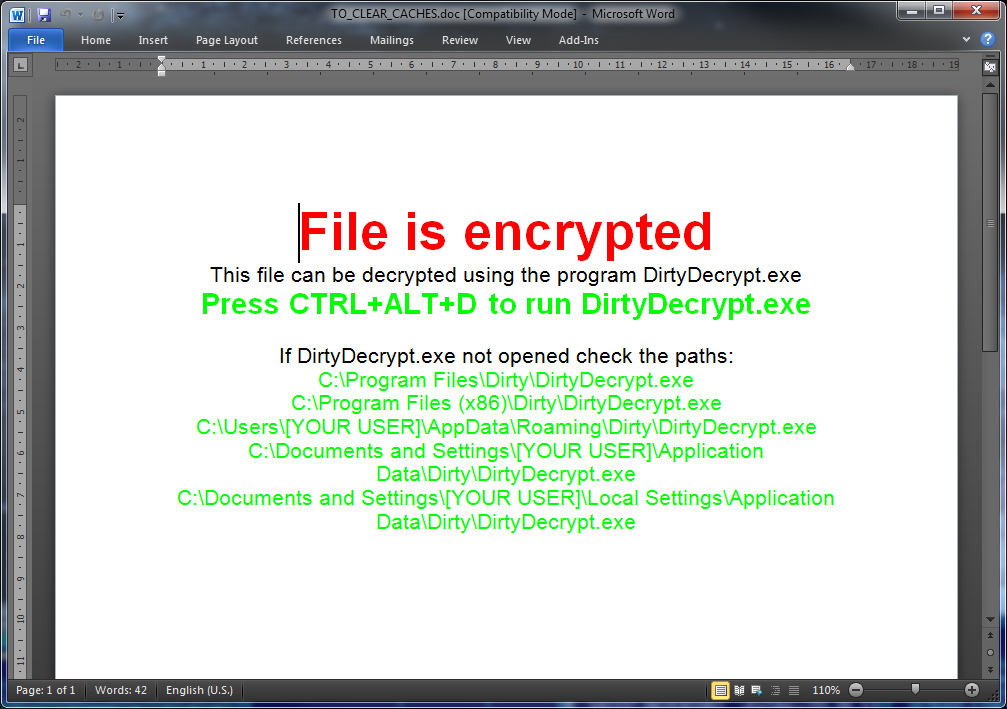
Win32/Filecoder.BH, also known as DirtyDecrypt, features an interesting method of displaying the ransom notice to the user. During the encryption cycle the content of image files, as well as documents, is overwritten with the notice followed by the encrypted original bytes.
Another recent variant, Win32/Filecoder.BQ, tries to put the victims under pressure by displaying a countdown timer showing how long it will be before the encryption key is permanently deleted. Interestingly, victims are given the option to pay the ransom with Bitcoins, along with usual ransomware payment methods like MoneyPak or Ukash. More details on this variant can be found in ESET’s Threat Encyclopedia entry: Win32/Filecoder.BQ.
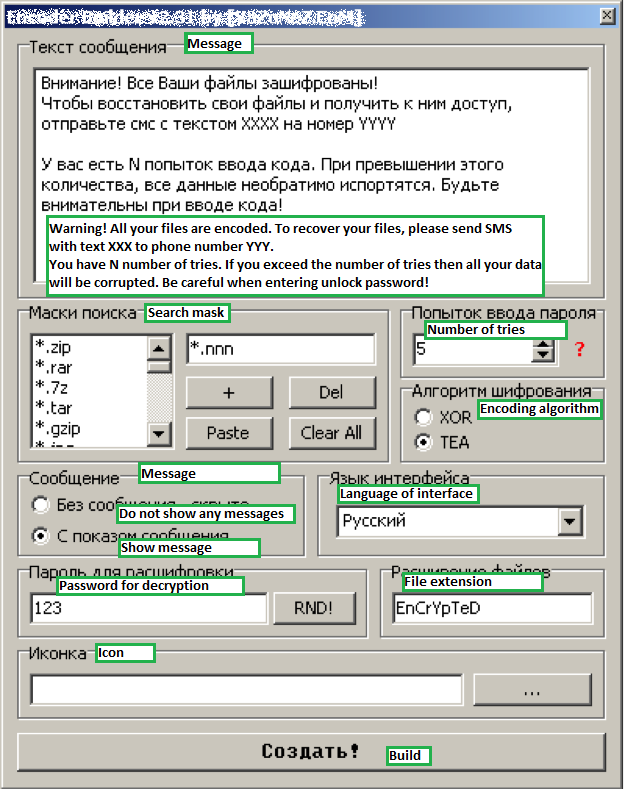
Some Filecoder variants are even built by using a special builder utility, similarly to banking trojan builders sold on underground forums. The builder allows the attacker to select what file types are to be encrypted, the desired encryption method, displayed ransom message, and so on.
A few words of advice
In some cases, when the Filecoder uses a weak cipher, or a faulty implementation, or stores the encryption password somewhere to be recovered, it may be possible to decrypt the files. Unfortunately, in most cases, the attackers have learned to avoid these mistakes and recovering the encrypted files without the encryption key is nearly impossible.
If remote access to a computer is required, proper security measures must be taken, RDP should not be open to the public Internet and a VPN with two-factor authentication should be used.
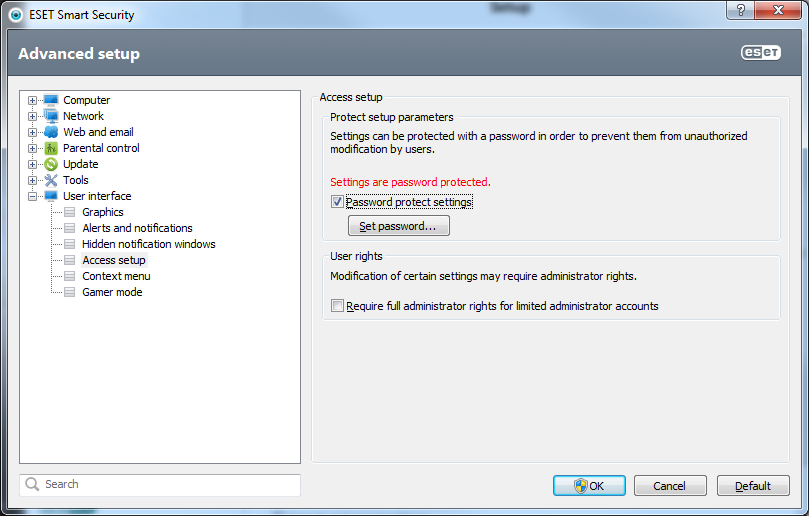
It is also a good idea to password-protect your anti-malware software's settings to prevent them from being altered by an attacker.
The general computer security advice about being cautious and keeping your anti-virus and all software up-to-date applies, of course, but in this case, most importantly: backup regularly!